Maximizing Google Apps Security, Privacy and Compliance

What You Need to Know to Secure Your Data
Enterprises of all sizes turn to Google Apps for Work (now known as G Suite) to migrate their teams to the cloud. Google’s collaboration, sharing, and ease of use are second to none. In recent years, Google has bolstered its offering with new data security and privacy capabilities.
As security, privacy, and meeting regulatory requirements become top priorities for enterprise IT, it’s critical to understand how Google protects you, and when additional security measures might be beneficial.
In the cloud era, data security, privacy, and compliance are shared responsibilities between service providers like Google, enterprise IT organizations and end users. In this blog, we address the default data security features included in Google Apps for Work, highlight situations where you may need to add supplementary layers of data protection, and offer tips for maximizing your organization’s cloud safety.
1. How Does Gmail’s Built-in Encryption Protect My Data?
Google protects your data in two important ways. First, it enforces transport layer security (TLS) between Gmail clients and Google servers. Secondly, it secures your data at rest while in the Google ecosystem.
By providing TLS, Google for Work adds a critical layer of security that some on-premise solutions lack, and helps to ensure communications sent to or from your mail server will remain encrypted–provided the other servers that they travel through also support TLS. In addition, Google has made significant efforts to convince other service providers to use TLS.
TLS provides a solid foundation for email security, particularly for communications that remain inside the Google ecosystem. But since no cloud provider has control over servers outside of their own ecosystem, you ultimately have no control over how many servers your emails pass through, and no way to predict the security measures that these servers provide.
Through configuration options, administrators can mandate that communications only occur through encrypted channels. However, if the receiving party’s server that does not support TLS, the communication will not be allowed. This means the email will not reach its intended recipient.
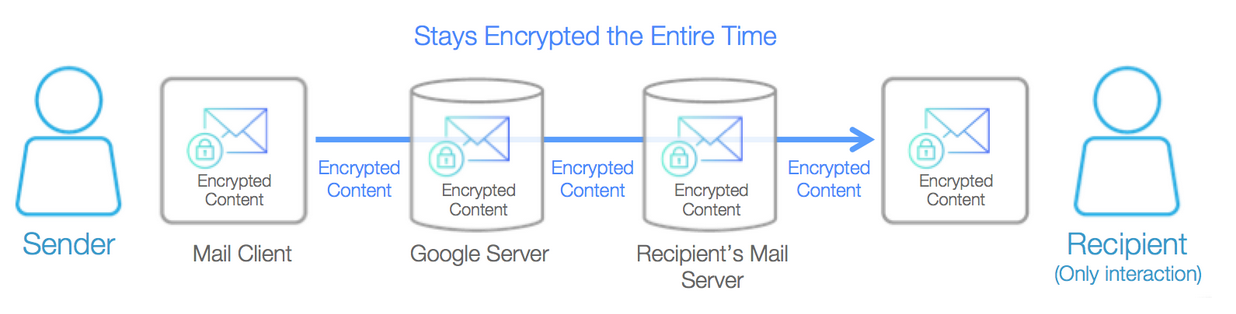
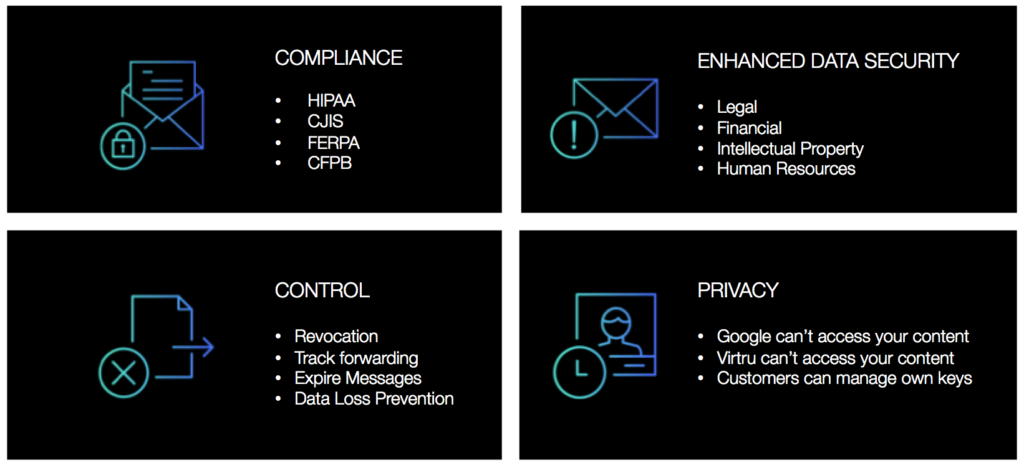
Given these circumstances, and the fact that some on-premise email platforms do not support TLS like Google does, you might consider adding a client-side encryption tool like Virtru to your Google Apps domain. As the name implies, client-side encryption protects your data from the time it is created until it is consumed by your recipients, or anyone else to whom they send it. This additional layer of protection ensures security regardless of where you or your recipients share your data.
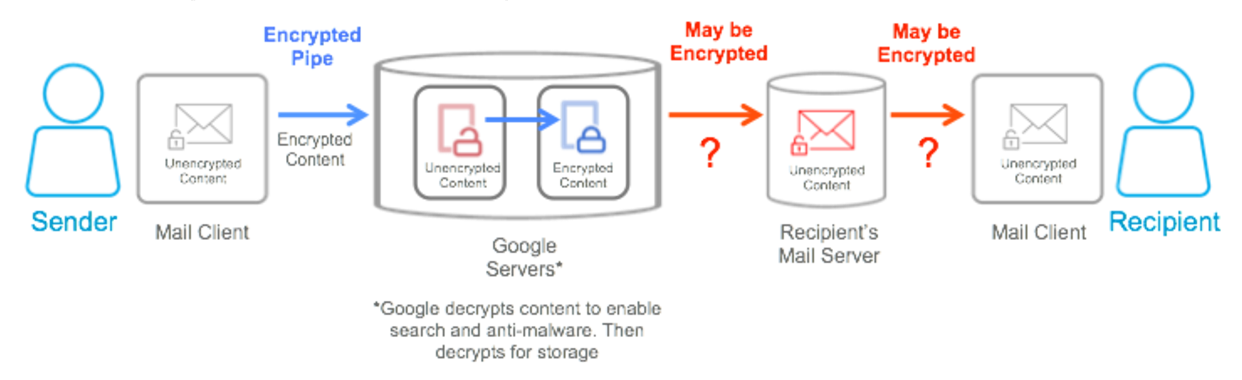
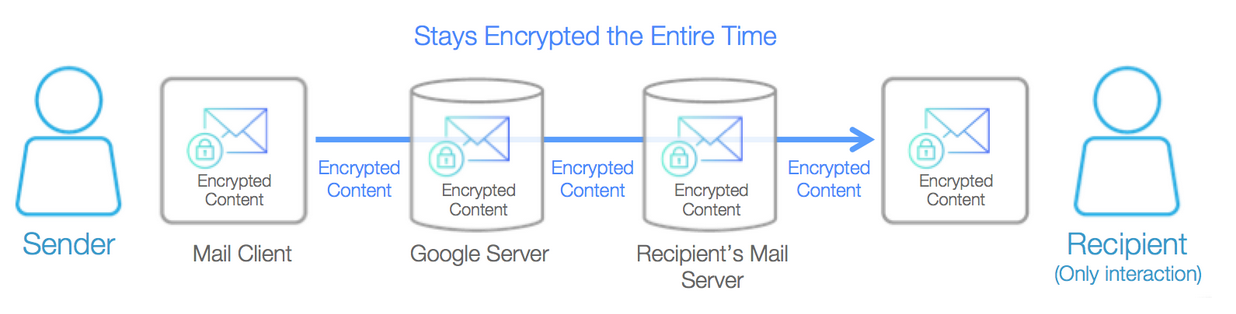
The below diagrams highlight where Google ensures encryption by default, and where client-side encryption adds additional protections.
Standard Gmail Point-to-Point Encryption
Virtru Client-Side Encryption
2. What Kind of Built-In Data Loss Prevention (DLP) Capabilities Do Gmail’s Content Compliance and DLP Features Provide?
Google Apps administrators can use Gmail’s Content Compliance and DLP features to scan content after it has already left the sender’s inbox and assign appropriate actions. You can use these rules to, for instance, reject a message that contains a certain keyword.
This feature works by routing email through Google’s servers, where it is decrypted, scanned by the content compliance engine, and then acted upon before being re-encrypted and sent to recipients. By necessity, this means that content is not encrypted on the client-side, and that Google can access unencrypted content.
To ensure that no third-party has access to unencrypted content, DLP must be pushed to the client side, where content can be scanned and acted upon before it hits the cloud. Virtru offers client-side DLP capabilities for organizations looking to ensure that sensitive info never leaves their devices unencrypted. Virtru DLP scans content before it ever leaves the sender’s inbox, keeping your most valuable data from ever hitting the cloud unprotected.
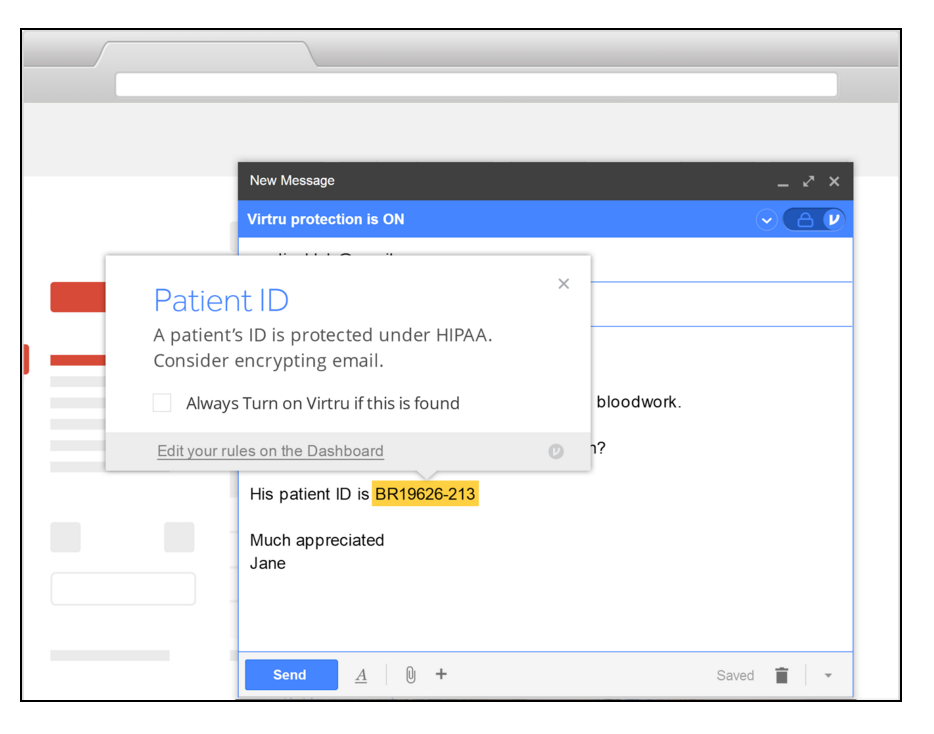
Virtru DLP adds some additional protections that Gmail DLP also provides, including the ability to:
- Set rules to automatically encrypt sensitive emails and files.
- Prevent sensitive content from ever leaving a sender’s inbox unprotected.
- Inform end users of real-time compliance violations in the body of their emails.
- Create complex custom rules using multiple criteria.
- Easily view compliance violations on a per email and per user basis.
3. How Does Google Help Me Achieve HIPAA Compliance?
One of the benefits of Google for Work’s secure cloud platform is that it helps organizations meet many HIPAA compliance requirements for data encryption and security. By leveraging its shared infrastructure, Google offers its customers greater security and compliance than legacy on-premise solutions–at a fraction of the cost.
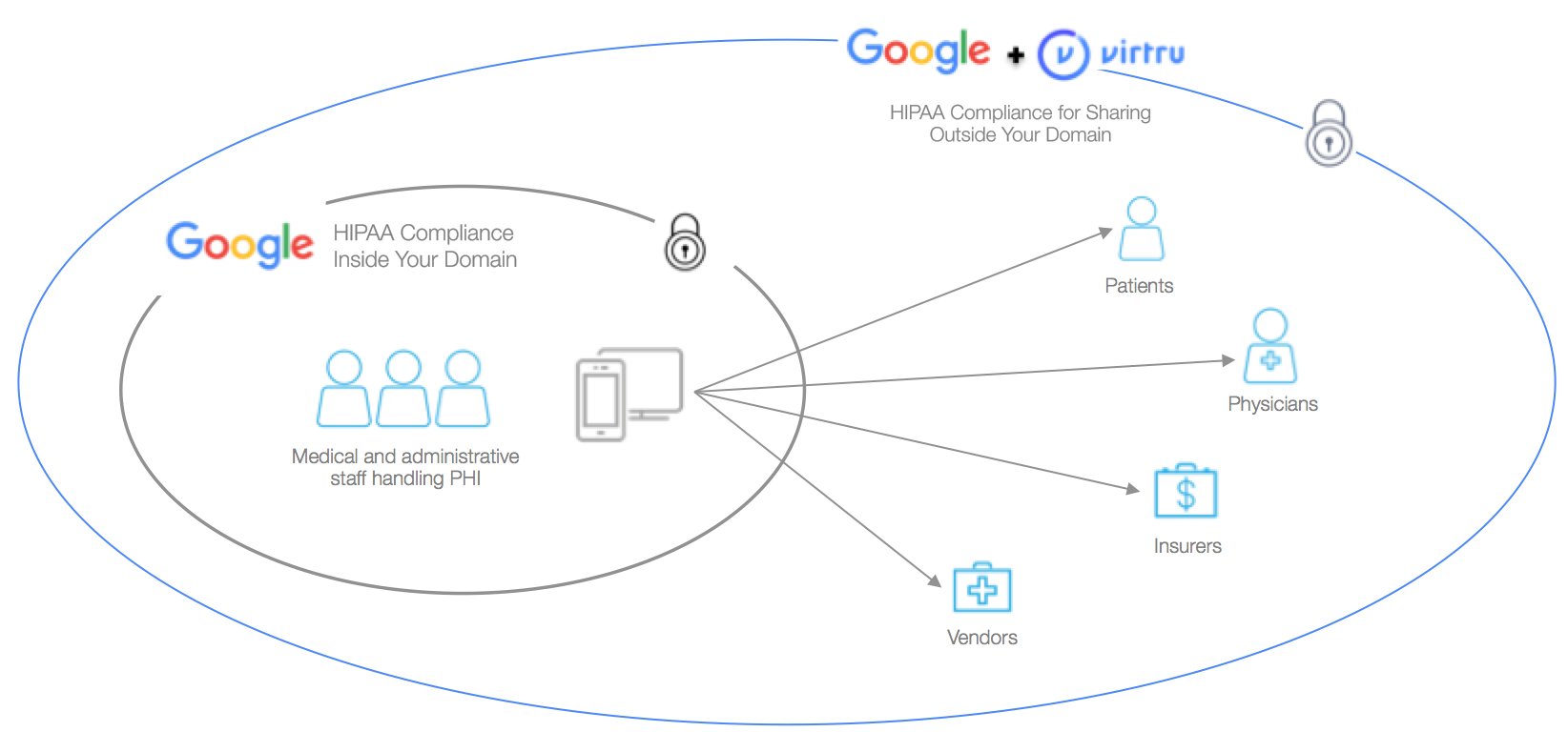
However, as with all things in the cloud era, security relies on shared commitments from platform providers and customers. Google has developed tools and guidelines to ensure security and compliance, and they have strongly encouraged other service providers to leverage encryption, too. Despite these efforts, there are no assurances that your data will remain secure once it leaves Google’s protected ecosystem.
Since many covered entities must share PHI with patients, providers, insurers, and other organizations who do not use Google for Work, it is prudent to add a client-side encryption solution like Virtru to always ensure compliance. This additional layer of protection ensures perpetual HIPAA compliance, regardless of where you or your recipients share your data.
As the diagram below shows, Virtru encrypts emails and files from the client-side, which ensures HIPAA compliance no matter what platforms your recipients use:
In addition, Virtru DLP can provide a pre-populated rule pack for HIPAA compliance that can be easily installed across a Google Apps domain.
4. What is Google Apps Message Encryption (GAME) from Zix Corporation, and How Does It Protect My Content?
GAME by ZixCorp is a portal-based email security tool. Emails are flagged for protection by Zix, and messages and attachments are stored on a Zix portal server. Recipients are notified by email, and can then establish a user ID and password to access their content within the Zix Portal application.
This architecture adds additional security because by requiring new usernames and passwords to access sensitive content. However, Zix does not provide client-side encryption. Unencrypted plaintext is sent over an SSL connection, giving intermediate providers access to this unprotected content.
This distinction means that ZixCorp manages the encryption keys and could have access to unencrypted versions of emails and attachments sent through GAME. This architecture introduces additional security risks and does meet the requirements of certain regulations like ITAR and CJIS, which mandate that no intermediate party can ever have access to unencrypted content.
Only client-side encryption approaches like S/MIME, PGP, and Virtru ensure that content remains encrypted until it arrives on the intended recipient’s device. As a result, only senders and receivers ever have access to the decrypted email content. Third parties do not.
GAME by ZixCorp (And All Other Portal-Based Encryption)
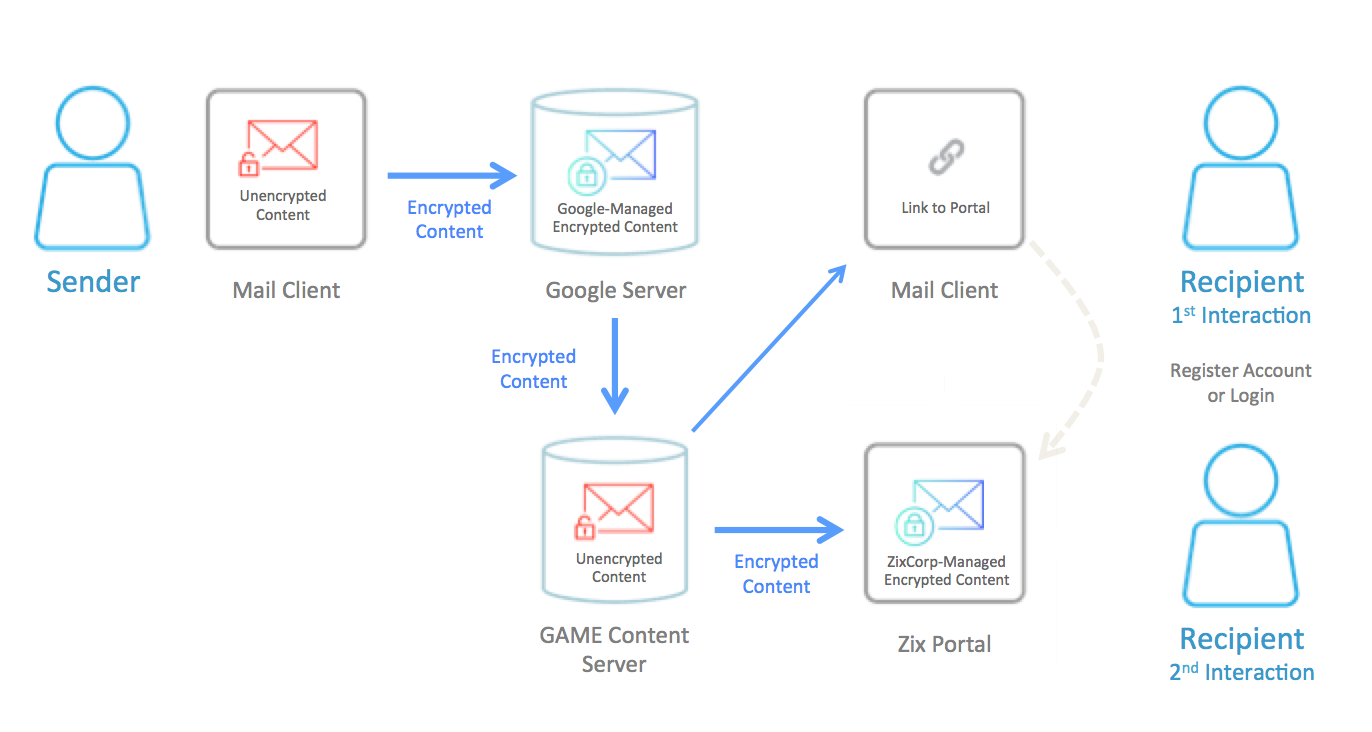
Client-Side Encryption (S/MIME, PGP, Virtru)
5. Does Google “Undo Send” Let Me Revoke Emails I’ve Already Sent?
Earlier this year, Google announced that it was making its ‘Undo Send’ tool a standard Gmail feature. Undo Send delays email transmission by 30 seconds, giving you time to change your mind. If you choose to “undo” within 30 seconds, your message will not be sent. Once sent, your email becomes irrevocable, just like any other Gmail message.
If you are looking for the ability to revoke a message that you’ve already sent at any time, regardless of whether or not the recipient has already read your message, Virtru will do the trick. When you revoke a message with Virtru, you signal to Virtru’s servers that the indicated recipient should no longer have access to the keys needed to decrypt that message content. Thus, when the recipient goes to read the revoked message, all he sees is this:
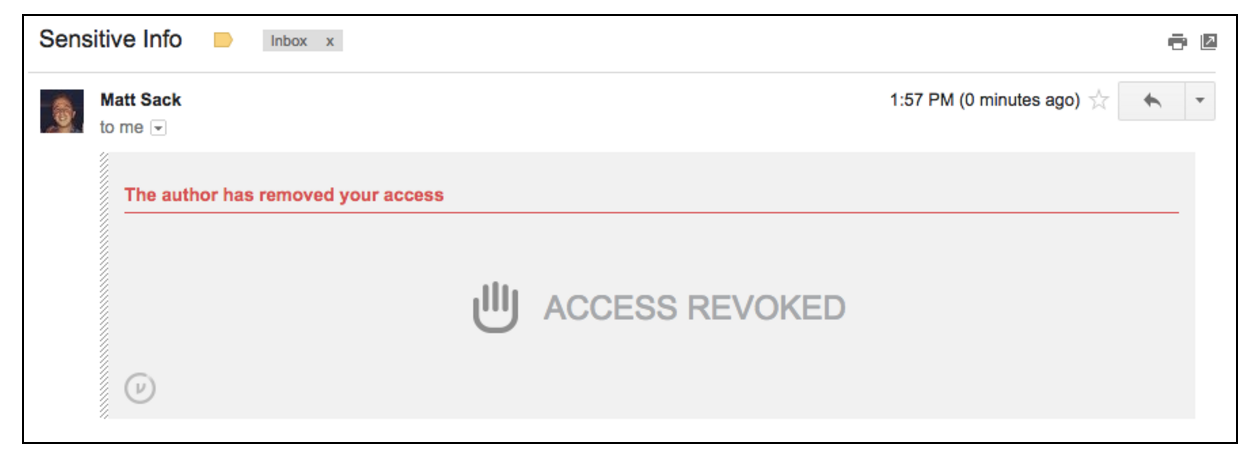
In addition to revocation, Virtru also adds additional controls including message expiration and forwarding control. Taken together, these capabilities allowing granular control of content, even after it has been opened by a recipient — enabling greater security and control.
Bottom Line: Google offers best-in-class security and privacy controls. To meet regulatory and data security compliance, additional protections like Virtru client-side encryption may be beneficial or required.
Google for Work provides many built-in data security protections, particularly for information shared within the Google ecosystem. To maximize security and ensure regulatory compliance, most experts recommend a layered security approach.
Add-ons like Virtru enable you to meet additional regulatory and data privacy requirements. By adding Virtru client-side encryption to your Google domain, you ensure that only authorized parties can ever access your content–making an already super secure Google for Work cloud platform even more secure.
If you’re using Google Apps for Work, you’re already in a good position. Here’s what else you should consider:
- Ensure that your Google Apps security controls have been configured properly for maximum security when sharing with parties inside of the Google ecosystem.
- Add a client-side data encryption service to ensure regulatory compliance and data security when sharing with parties outside of the Google ecosystem.
- Avoid data leaks caused by human error by using revocation and data loss prevention (DLP) to automatically detect and client-side encrypt sensitive content before it leaves your device.
- Enable data security measures to retain control of sensitive information even after it has been shared. The ability to revoke messages and files, even after they’ve been opened, set expirations, and restrict forwarding adds an additional layer of data security and compliance.
As a trusted Google partner, Virtru complements your Google Apps security experience with granular control capabilities like revocation, client-side DLP, and client-side encryption that prevents unauthorized parties or service providers from ever accessing your data.
 If you’re interested in finding out more about how Virtru can work with your organization, let’s chat. Request a demo today.
If you’re interested in finding out more about how Virtru can work with your organization, let’s chat. Request a demo today.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial Team









