Data Encryption Software for Compliance with ISO 27001
Virtru’s Zero Trust data encryption provides enhanced security for information in transit and at rest, supporting many data security aspects of ISO 27001 Certification.

What is ISO 27001?
Information security is a critical component of every business. Defending against internal and external threats — from accidental data loss to sophisticated cyber attacks — is a top priority for organizations to safeguard their essential data.
ISO 27001 is a globally recognized standard that specifies a framework for an information security management system, or ISMS, encompassing people, processes and technology.
ISO 27001 is a set of procedures that outlines how you are addressing information security as a whole. It will push you to consider the following questions:
- How do you assess your risks?
- How do you review these risks?
- How much risk is your organization prepared to take on?
ISO 27001 is applicable to organizations of all types and sizes, making it one of the most popular information security standards in the world. It helps organizations manage their security practices clearly, effectively, and cost-efficiently.
Enable ISO 27001 Compliance for Your Business with Virtru Data Encryption
Virtru’s Zero Trust security solutions help you meet ISO 27001 standards by cryptographically tying attribute-based access controls to your data — protecting your most sensitive information everywhere it moves.
Encrypt Emails and Files in Microsoft 365 and Google Workspace
Email represents a massive surface area of risk, making it a smart place to start when working toward your ISO 27001 Certification. Virtru’s email encryption layers into the applications your employees already use, so they can safeguard sensitive data without changing the way they work.
Safeguard Inbound and Outbound Data Flows
Sending sensitive documents over email is not always a viable option. For sensitive data in motion and at rest, an encrypted file-sharing solution with complete data privacy is required. Secure Share enables you to securely send and receive files of nearly any size with individuals inside and outside your organization.
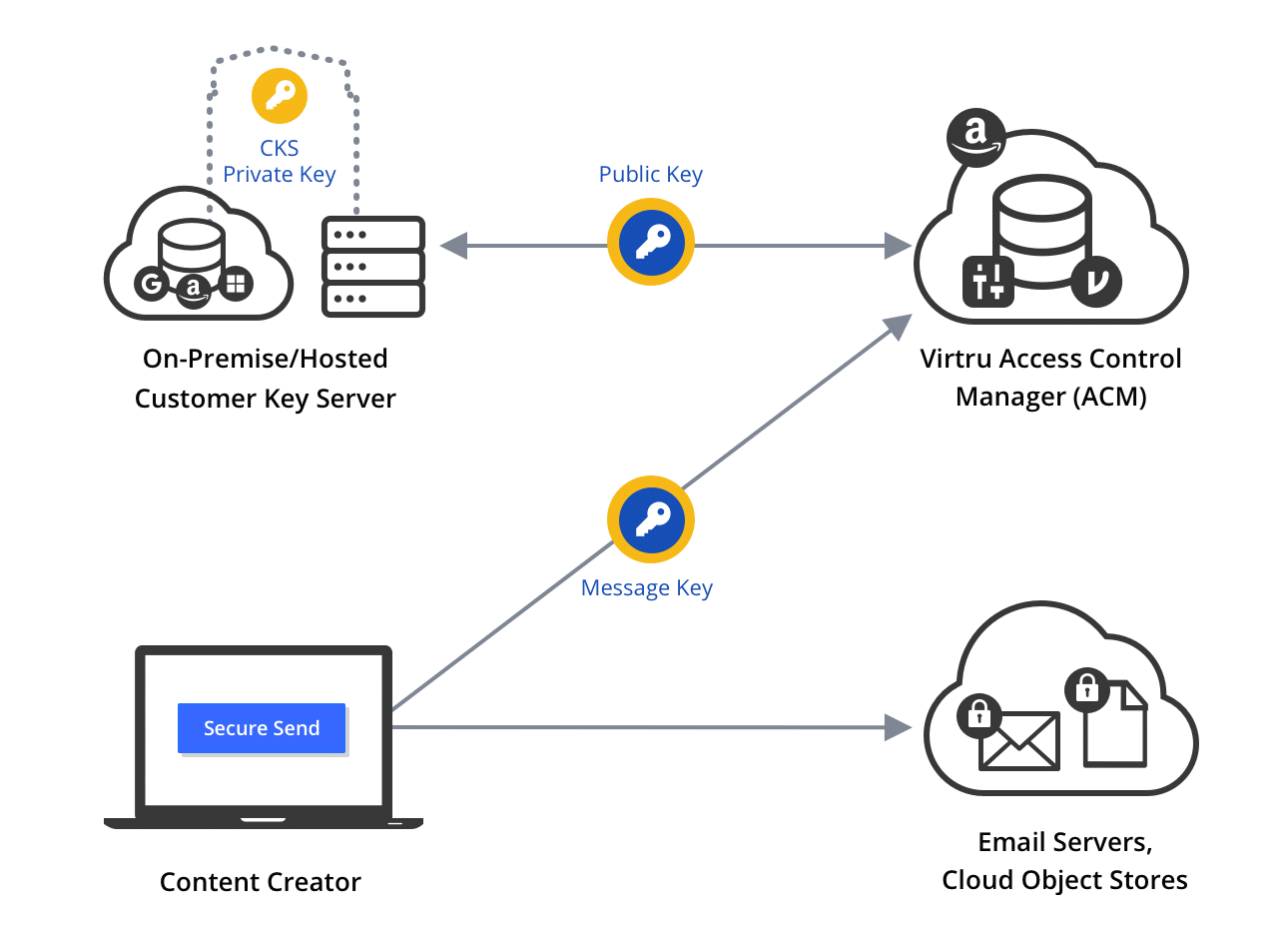
Manage Your Own Encryption Keys for Zero Trust Data Control
For the ultimate control of your sensitive data, everywhere it lives, leverage Virtru's Customer Key Server, which puts you in complete control over your own encryption keys. This way, no third party — not Google, Microsoft, or even Virtru — can access your encrypted information.
Automate Encryption for SaaS Apps like Salesforce and Zendesk
Sensitive data flows throughout your organization. Safeguard that information by putting Virtru’s data protection gateway in place to automatically encrypt and decrypt data moving in and out of apps like Salesforce, Zendesk, and others.
3 Key Facets of ISO-27001 Compliance
Confidentiality
Ensure that data is only accessible to the intended people or entities. For the strongest security, leverage attribute-based access controls to grant access only to those with a need to know.
Integrity
Availability
Resources
Get expert insights on how to address your data protection challenges.
Ready to take the next step?
6,700+ CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.