Virtru Data Protection Gateway
Automated Email & SaaS Encryption
Automatically secure sensitive data domain-wide—shared via email, unprotected endpoints, and SaaS apps like Salesforce and Zendesk without disrupting workflows.
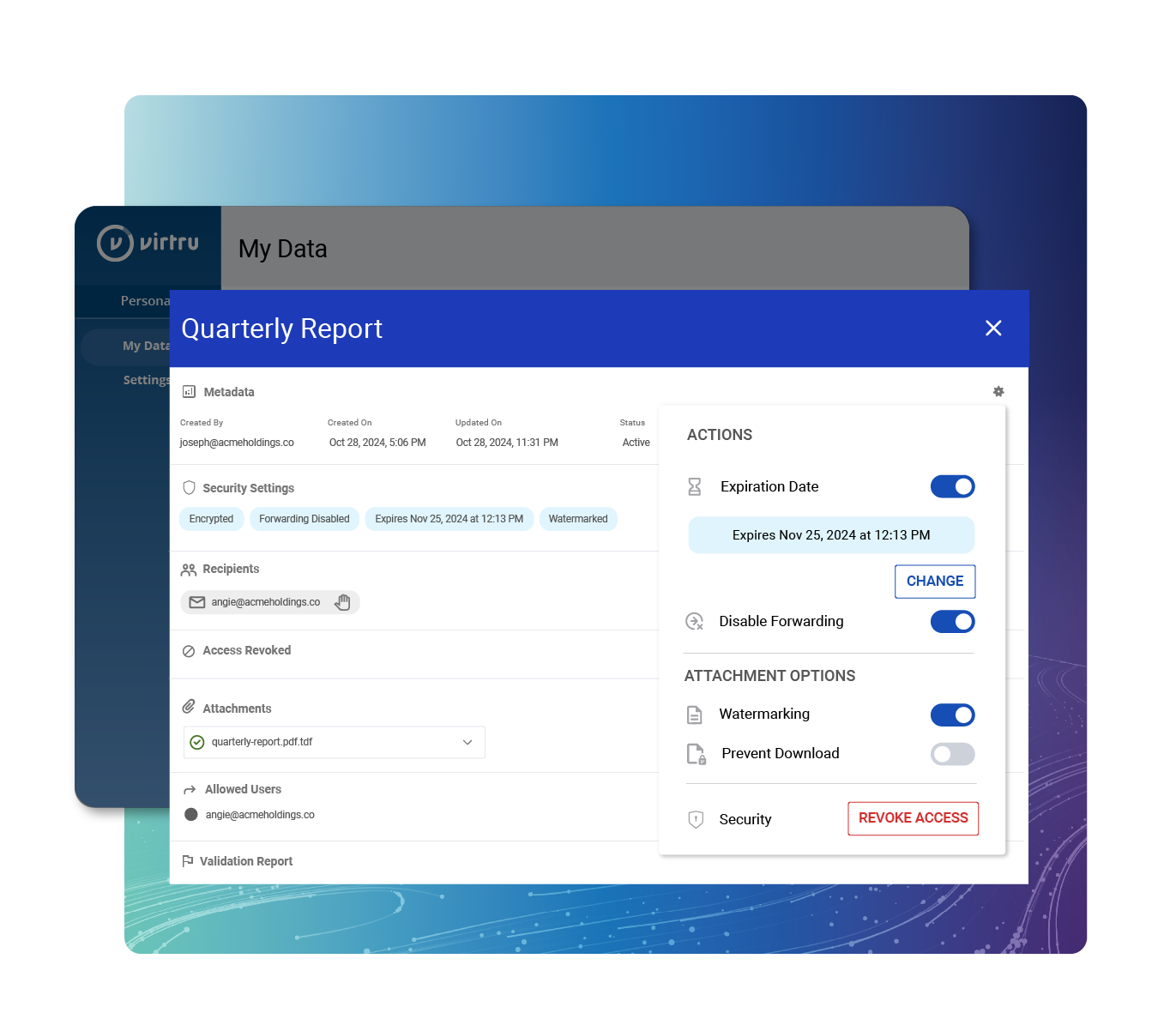
Data-Centric Protection for Email and Application Workflows
Virtru Data Protection Gateway smoothly fits into your current email and SaaS apps, protecting against data breaches and boosting your team's collaboration to its fullest potential. Secure all sensitive information flowing through your organization with a single solution that automatically protects everyone - no need to decide which employees "need" security.
/control-center-users.webp)

/control-center-users.webp)

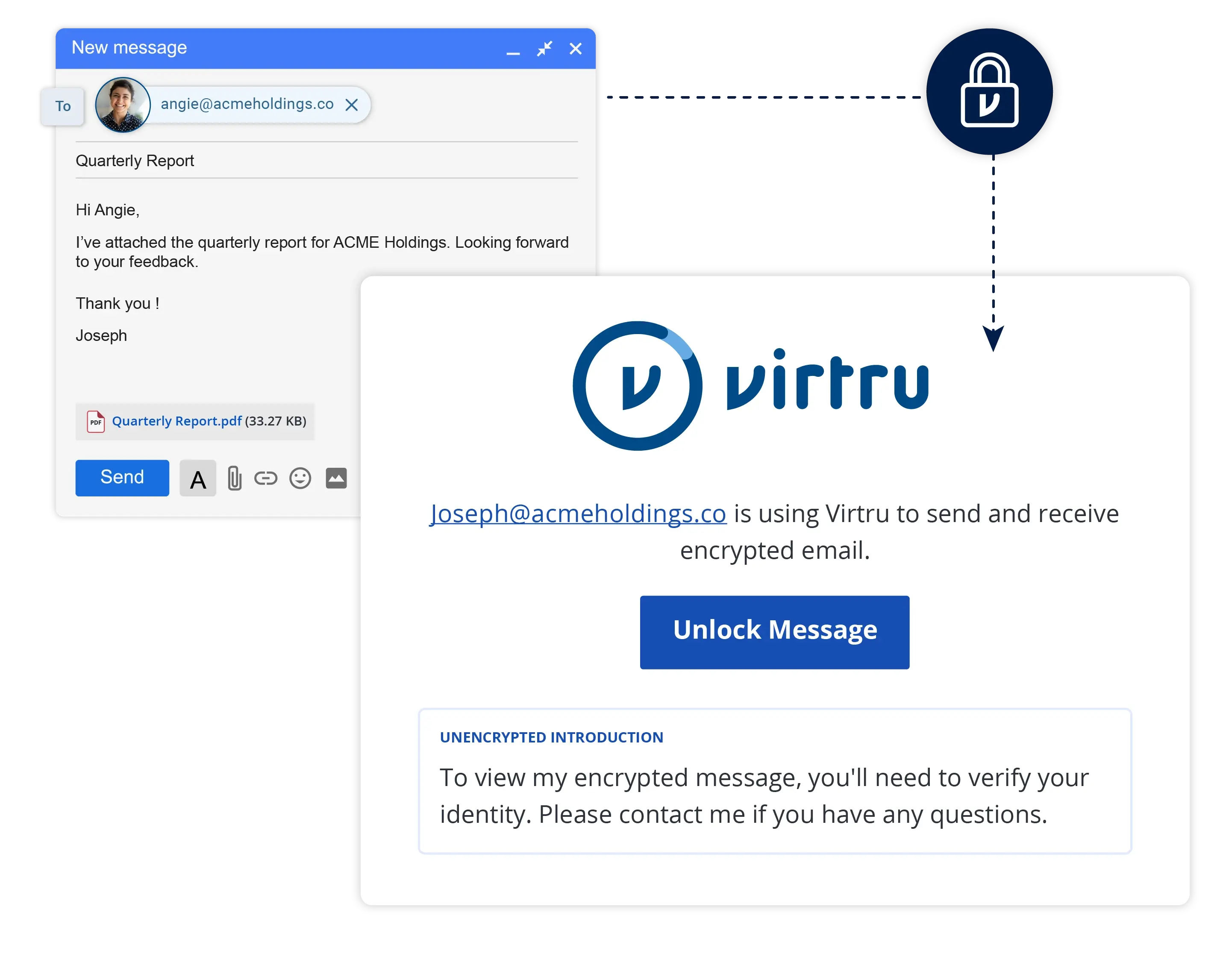
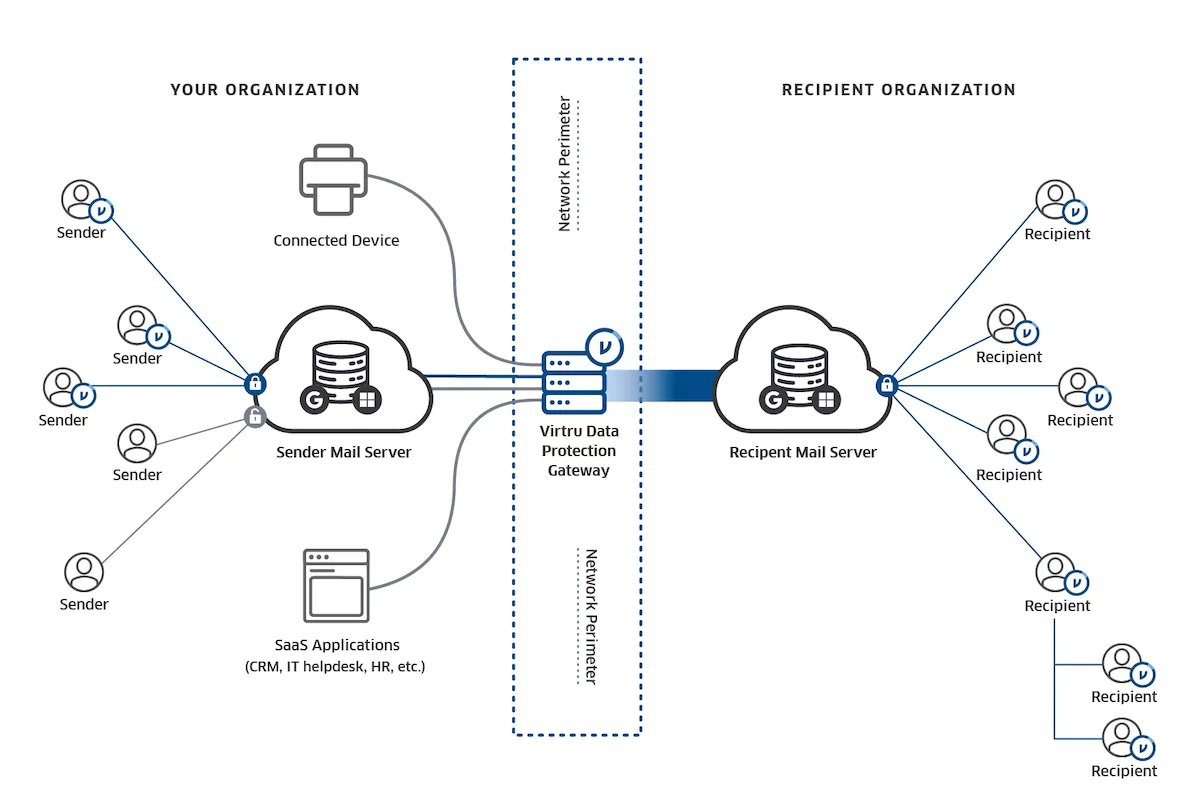
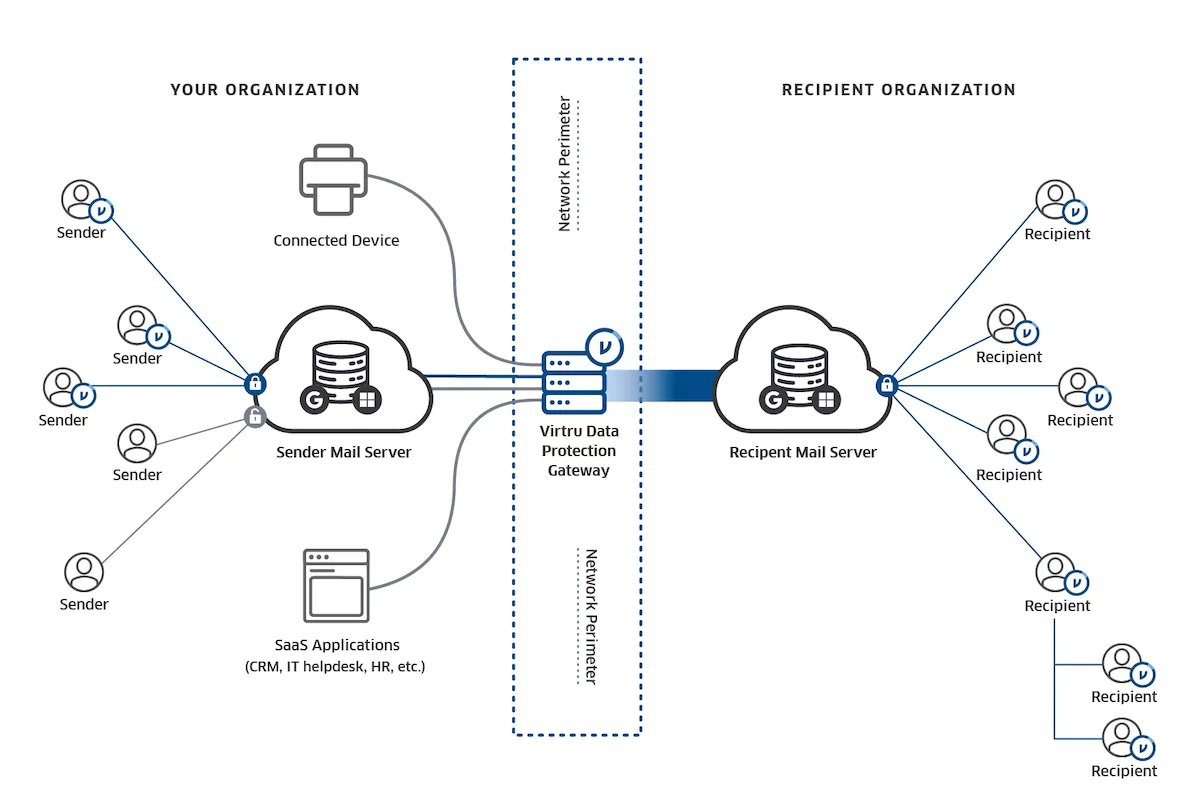
How the Gateway Works
Protecting You Where You Already Are
The Virtru Data Protection Gateway automatically protects and controls emails and attachments flowing through custom applications and enterprise SaaS apps.


“Virtru helps us maintain HIPAA compliance within new and existing communication platforms, while providing an incredibly easy experience for our patients. Our Virtru integration with Salesforce supports seamless, secure exchange of PHI without interrupting existing processes.”
Steven Schwartzberg
IT Director, Tribeca Pediatrics
Your Organization’s Data Safety Net
Effortlessly Improves Compliance
Virtru Data Protection Gateway is your “safety net” to help meet compliance for data privacy regulations such as HIPAA, GDPR, PCI, FTC Safeguards, CCPA, and more.
Kunes Auto Group Uses Virtru to Encrypt Data For FTC Safeguards
Read the Case Study
Protects Workflows, Instead of Inhibiting
Promote security and efficiency with targeted encryption that protects data flowing in and out of your organization in apps, email, and more - with little to no effort for users.
Why a Global Banking Giant Chose Virtru for Easy-to-Use Email Encryption and Compliance
Read the Case Study
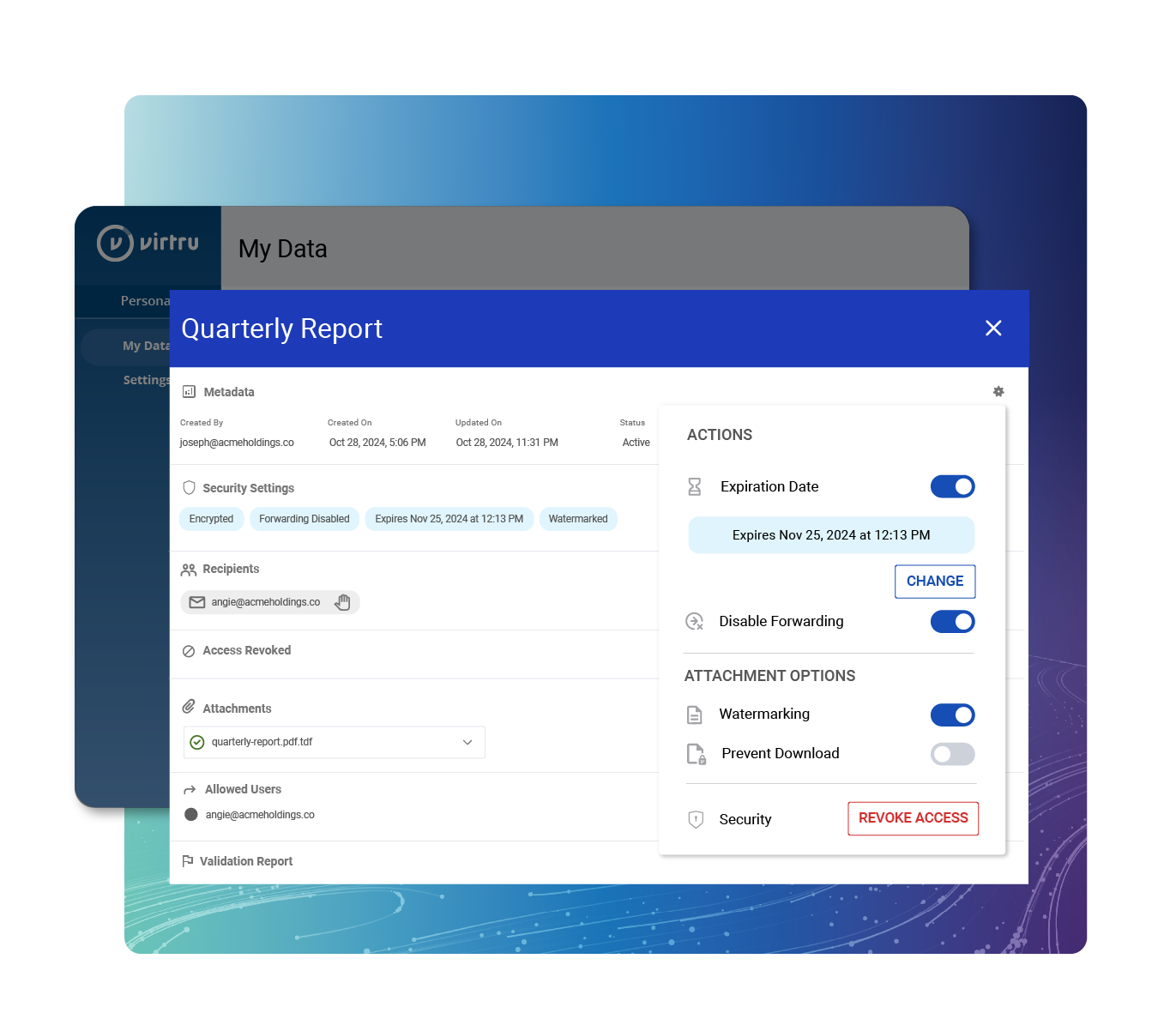
Hold the Keys to Your Data
Achieve seamless, integrated data security and compliance with Virtru Private Keystore, eliminating the need for multiple vendors in a true zero-trust architecture.

HR Tech Innovator Maki Uses Virtru Private Keystore for Advanced Google Cloud Security
Read the Case Study
Virtru Data Protection Gateway Pairs Well With:

Virtru for Microsoft 365
Safeguard your messages and attachments in both Outlook for desktop and Microsoft 365. Virtru seamlessly integrates, offering an elegant blend of security within Microsoft Outlook.
Virtru for Microsoft 365
Virtru for Google Workspace
Your organization holds a wealth of sensitive data in Google Workspace. With Virtru, ensure this critical information remains private and protected throughout your Google environment.
Virtru for Google Workspace
Virtru Private Keystore
It's your data. Let's keep it that way. Take complete ownership of your encrypted cloud data. Host your private keys wherever you like. Let Virtru do the rest, from high volume key exchanges to policy management.
Virtru Private KeystoreResources
Get expert insights on how to address your data protection challenges
Easy, Affordable Zero Trust Security
Deploy Virtru today, and equip your teams to share data confidently and securely.
6,100 CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.




Book a Demo
Become a Partner
Contact us to learn more about our partnership opportunities.
Become a Compliance Champion
Contact us to learn more about our partnership opportunities.