Virtru Collaborate
Store, share, and collaborate on sensitive files with external partners — without losing control.
Every organization that handles sensitive data faces the same impossible choice: Lock it down and lose productivity, or share it freely and lose control.
Virtru Collaborate eliminates that tradeoff, making your data both protected and productive. This cloud-based solution provides a FedRAMP authorized space to encrypt, store, and share files containing information like CUI, PHI, and CJI — with granular policy and controls that travel with the data across organizational boundaries, powered by the open-standard Trusted Data Format (TDF).
Supports CMMC Level 2, ITAR, HIPAA, PCI, SOX, GLBA, and other regulatory compliance obligations.


FedRAMP Authorized Security That Adapts to How You Actually Collaborate
Virtru Collaborate provides a secure environment where you can store, organize, share, and collaborate on sensitive files with external parties without hindering workflows or losing control:
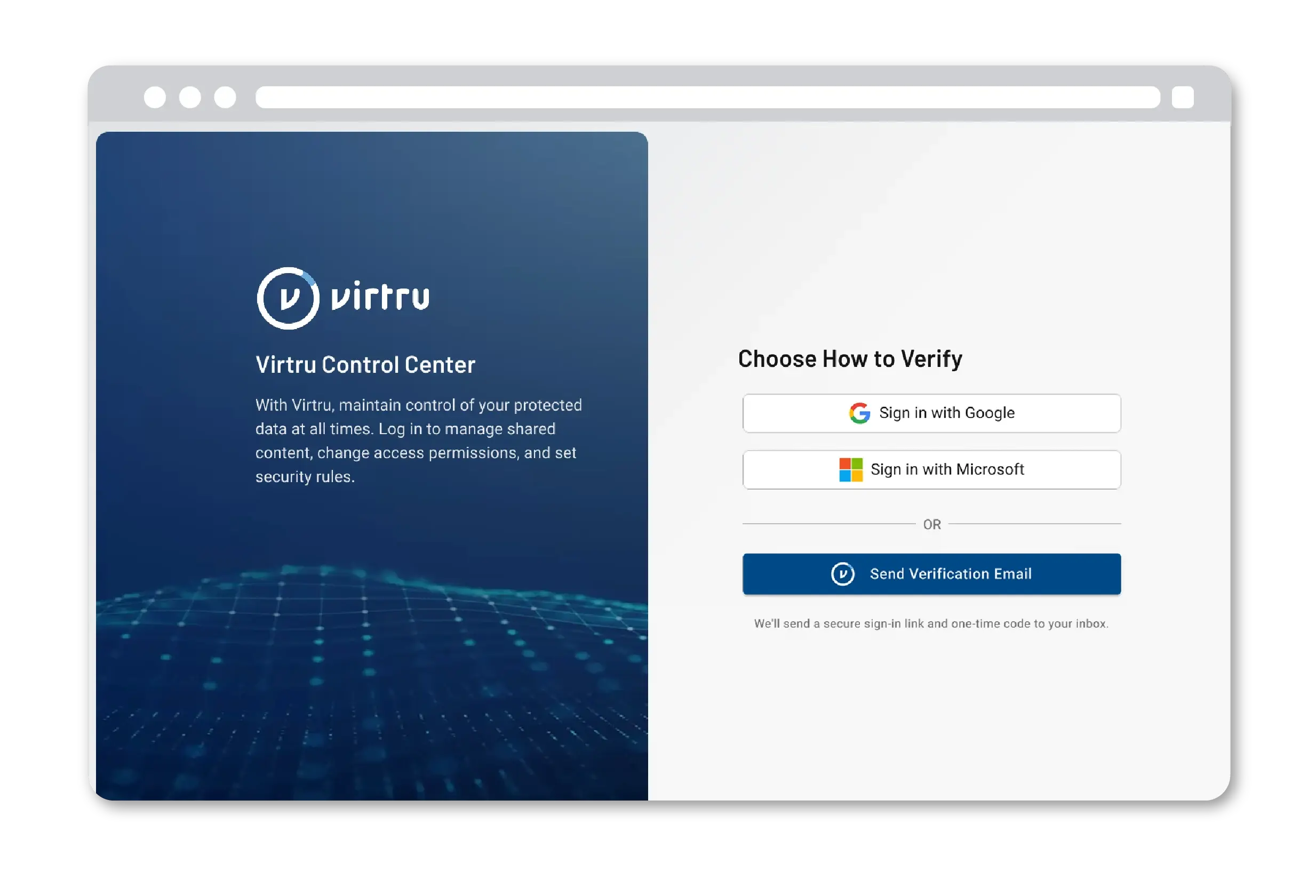
Security shouldn't create friction for legitimate users. Virtru Collaborate makes external collaboration straightforward for both your teams and external partners.
- Simple browser-based access with your existing credentials — no account creation or software installation required
- Confidently share files directly, or create secure folders for project-specific collaboration
- Integrate with existing DLP solutions to maintain consistent data protection policies across your environment
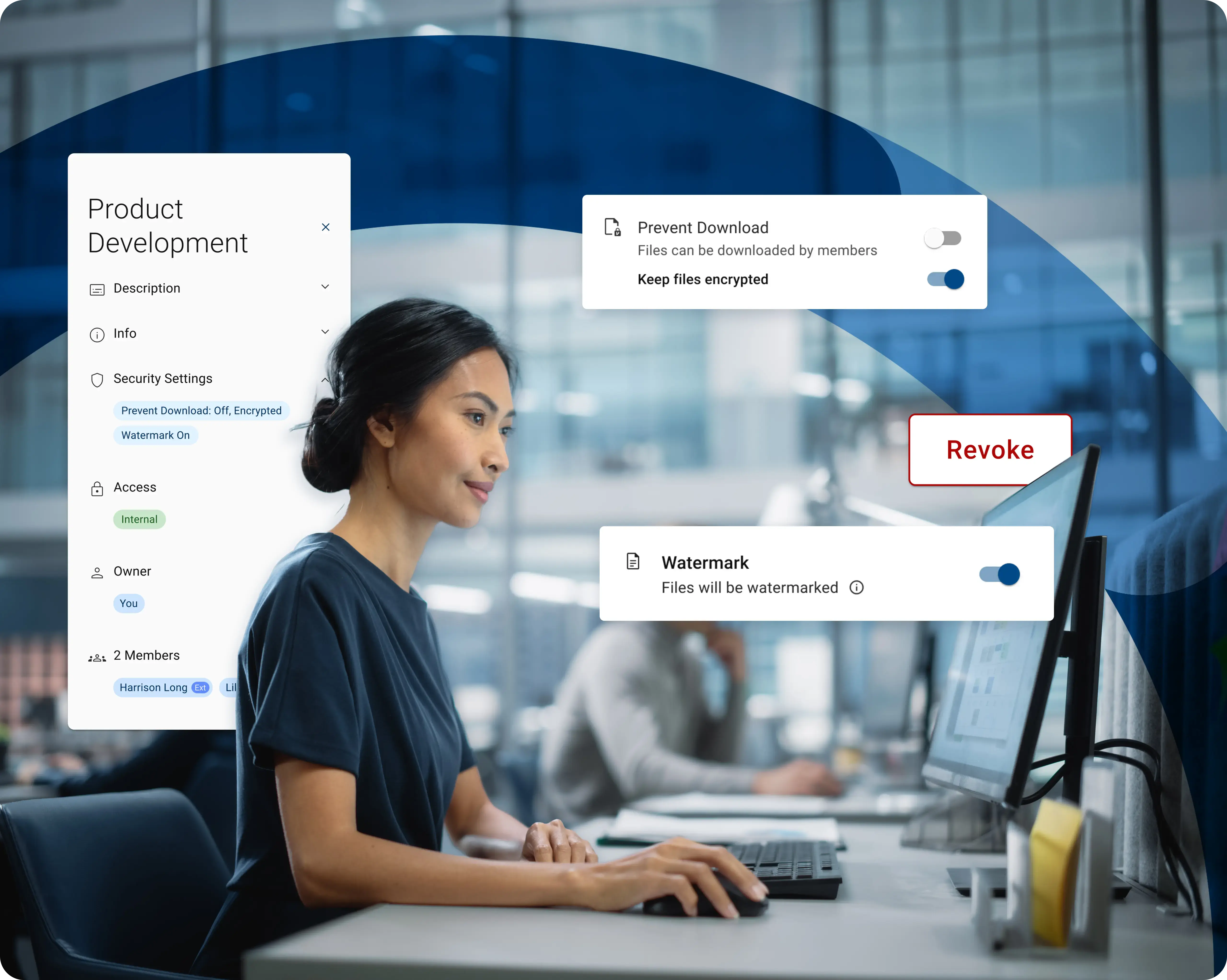
Protection doesn't stop when files leave your environment. The Trusted Data Format (TDF) open standard binds encryption and access policies directly to each file, so your authority travels with your data.
- Permissions travel with the data object, so you maintain control even when files are shared with contractors, partners, and other external collaborators
- Enable essential collaboration without the security compromises that conventional sharing tools require
- Confidently share files externally, knowing you can revoke or adjust access at any time–even after files leave your environment
Projects shift direction. Contractors change roles. Security incidents require immediate action. Maintain dynamic control over files you shared weeks or months ago.
- Revoke access in seconds, even after files have been accessed by external users
- Modify permissions on-demand without touching recipients' devices or asking them to re-download
- Context-aware access controls automatically adapt when user entitlements change or file classifications are updated
- Eliminate lingering access risk from forgotten permissions that become compliance violations
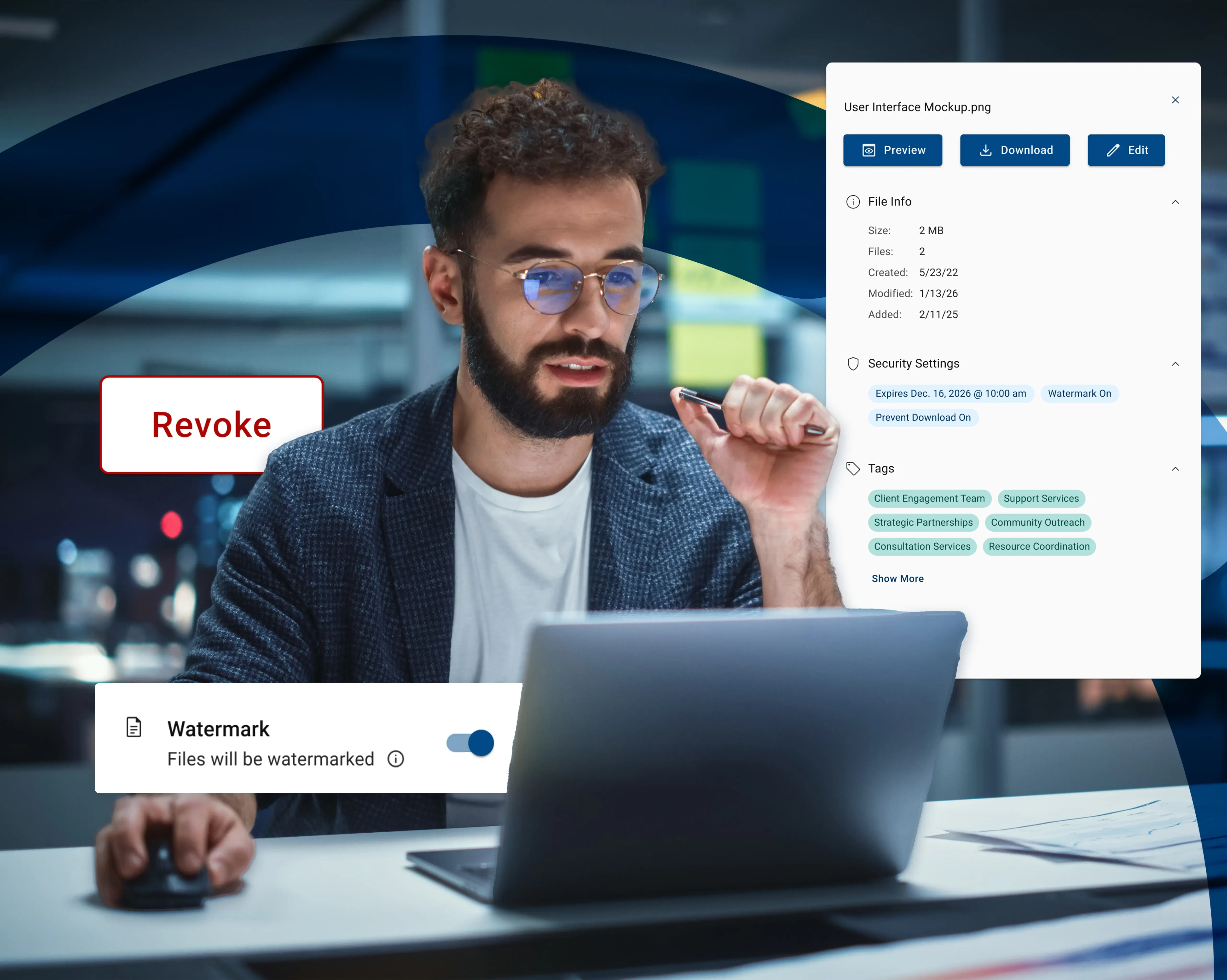
Your audit trail shouldn't end at your firewall. Track every interaction with shared files, regardless of where they're accessed.
- Track every interaction with your shared files, including access attempts, views, and downloads
- Meet audit trail requirements with comprehensive logs that capture activity on shared files, even after they leave your environment
- Answer auditor questions about who accessed sensitive data, when, where, and from which device
- Identify potential issues before they become security incidents or compliance violations
Collaboration Without Compromise
Protection That Travels With Your Data
Virtru Collaborate takes a fundamentally different approach to secure collaboration, embedding protection into the file itself to ensure only the right people access the right content at the right time.
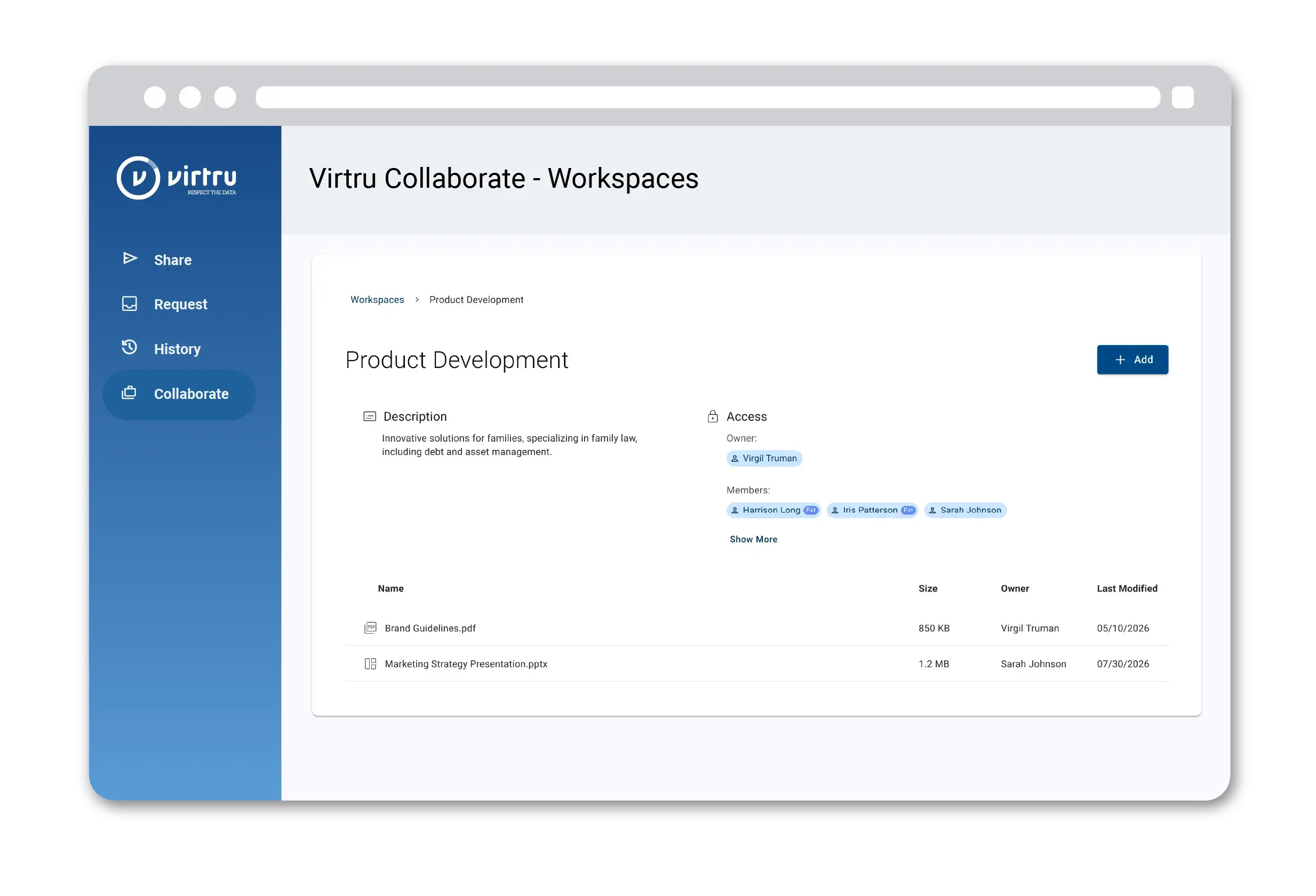
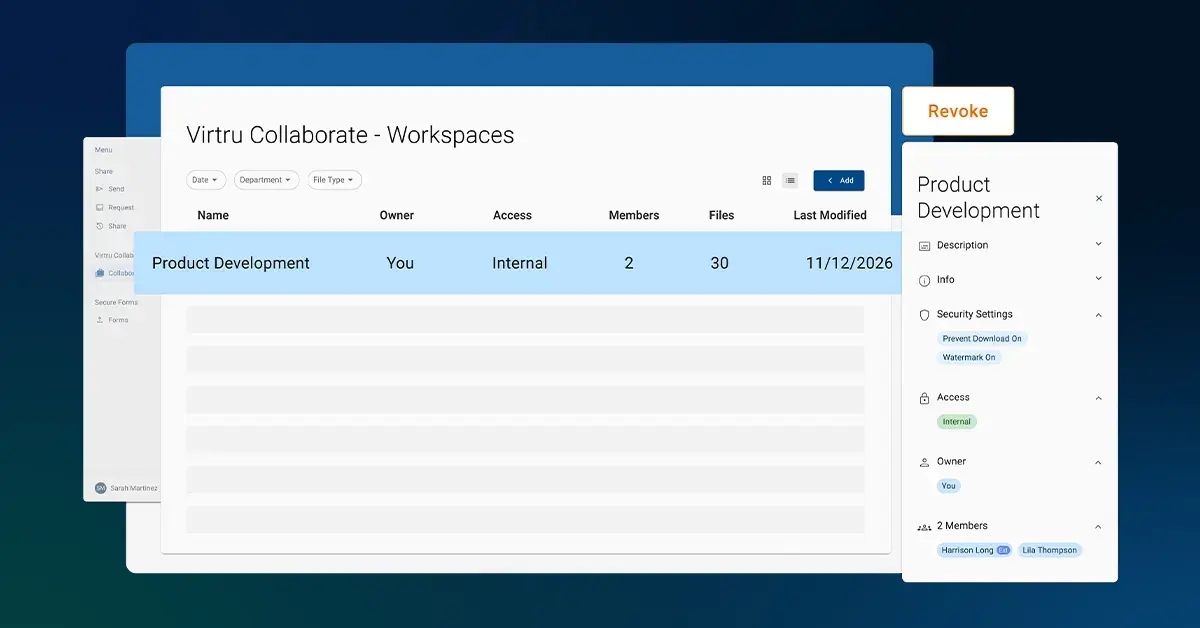
Create secure files and folders
Set up secure collaboration folders for specific projects or share individual files directly to recipients. You define who can access what and under which conditions.
/Copy%20of%20DSP-TDF.webp)
Protection travels with your files
Every file is wrapped in the Trusted Data Format (TDF), which binds encryption and access policies to the data itself. When external collaborators access or receive files, those protections remain active and enforceable at any time.
Maintain continuous control
Adjust permissions, revoke access, or let the system automatically adapt policies based on changing user entitlements or data classifications. Dynamic, granular access controls reduce lingering access risk after contracts or projects are complete.
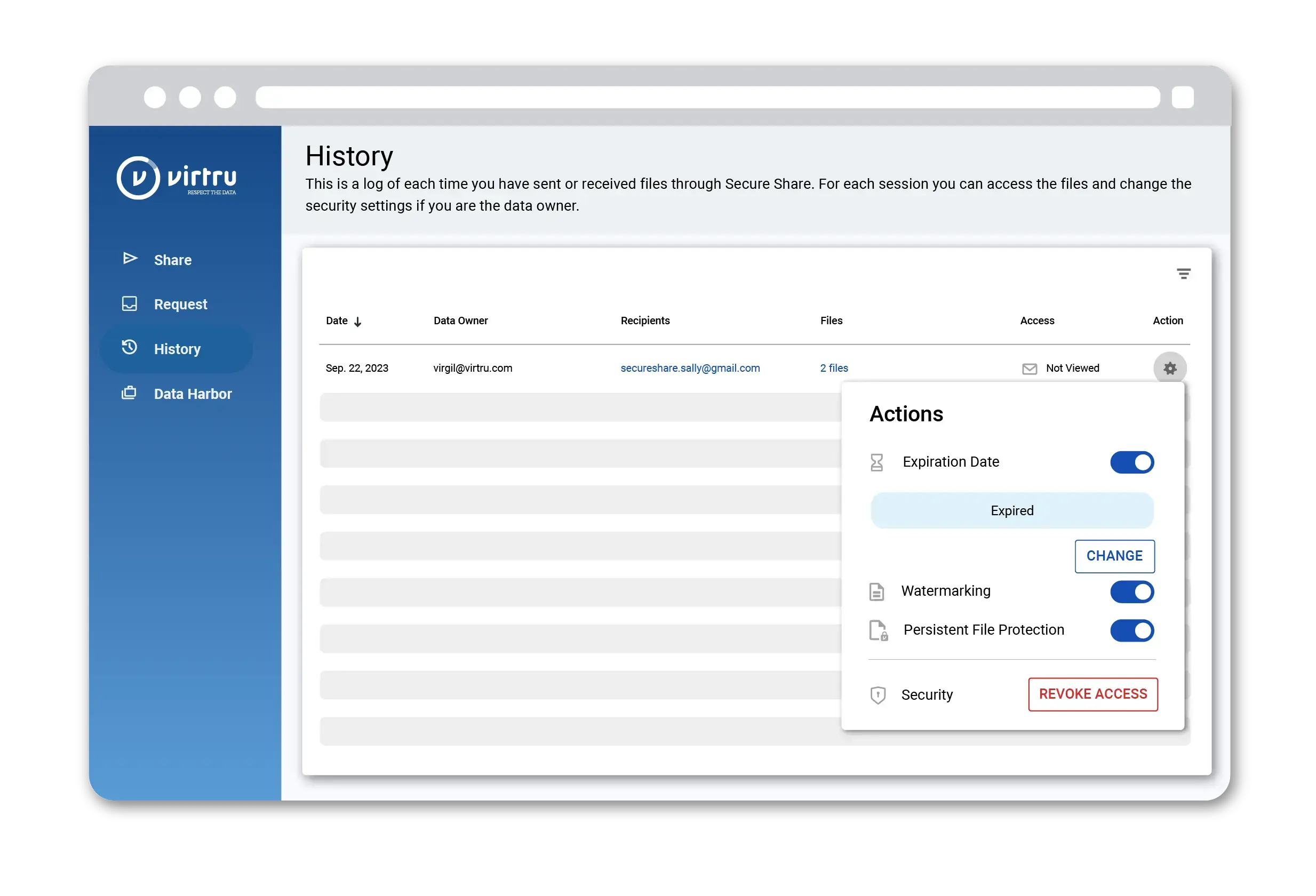
Track activity across all environments
Comprehensive logging captures every interaction with shared files, creating audit trails that extend beyond your perimeter to contractor systems, partner networks, and external devices.
Defense Contractors Sharing CUI
Defense contractors and subcontractors need to share Controlled Unclassified Information (CUI) across the supply chain while meeting CMMC Level 2 requirements. Virtru Collaborate enables collaboration with partners and suppliers while maintaining the continuous protection and audit capabilities that CMMC demands—even when files move to external contractor environments.
/blog-atx%20defense%20recap/atx-defense-webinar-recap.webp)
Healthcare Organizations Collaborating on PHI
Healthcare providers, payers, software vendors, and research organizations must share Protected Health Information (PHI) with external partners for care coordination, claims processing, product onboarding, and research initiatives. Virtru Collaborate ensures PHI remains encrypted and access-controlled throughout external collaboration workflows, supporting HIPAA compliance requirements without blocking critical operations.

Due Diligence for Financial Transactions
M&A teams, auditors, and financial advisors need to exchange sensitive financial records, personally identifiable information, and strategic documents with external parties during due diligence, audits, and advisory engagements. Virtru Collaborate provides the governance and audit trails required by SOX, GLBA, and internal compliance policies while enabling the rapid document exchange these time-sensitive processes demand.

Law Firms Managing Client Confidentiality
Legal teams share privileged documents, case files, and confidential client information with co-counsel, expert witnesses, and clients themselves. Virtru Collaborate maintains attorney-client privilege protections and confidentiality requirements even after documents are shared externally, with the ability to instantly revoke access if engagement terms change or conflicts arise.

Virtru Collaborate Pairs Well With:
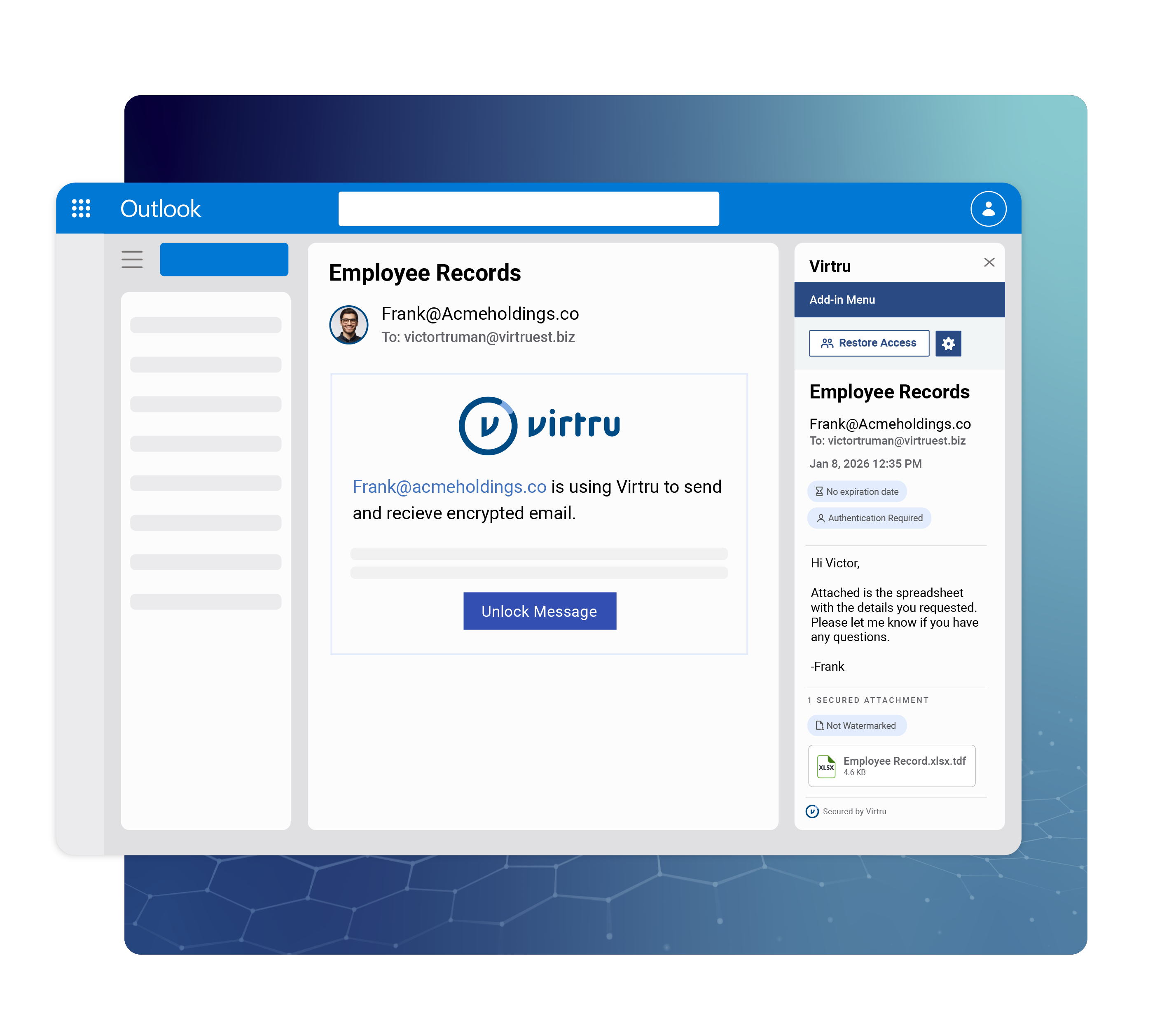
Virtru for Microsoft 365
Safeguard your messages and attachments in both Outlook for desktop and Microsoft 365. Virtru seamlessly integrates, offering an elegant blend of security within Microsoft Outlook.
Virtru for MSFT 365/Virtru%20for%20Drive%20Legal.webp)
Virtru for Google Workspace
Your organization holds a wealth of sensitive data in Google Workspace. With Virtru, ensure this critical information remains private and protected throughout your Google environment.
Virtru for Google Workspace
Virtru Private Keystore
It's your data. Let's keep it that way. Take complete ownership of your encrypted cloud data. Host your private keys wherever you like. Let Virtru do the rest, from high volume key exchanges to policy management.
Virtru Private KeystoreVirtru Collaborate Resources
Learn more about Virtru Collaborate for seamless, highly secure file collaboration.
Easy, Affordable Zero Trust Security
Deploy Virtru today, and equip your teams to share data confidently and securely.
6,100 CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.



Book a Demo
Become a Partner
Contact us to learn more about our partnership opportunities.
Become a Compliance Champion
Contact us to learn more about our partnership opportunities.