CJIS Compliance for Emails and Files
Encrypt and control criminal justice information (CJI) stored and shared via Google Workspace and Microsoft 365 for CJIS compliance (Criminal Justice Information Services).
CJIS Compliance: What Security Leaders Need to Know

What is CJIS compliance? Criminal Justice Information Services (CJIS) analyzes criminal justice information (CJI) from law enforcement centers around the country and provides a centralized database to store and access CJI. To use CJIS databases, organizations must comply with government regulations:
- Section 5.10.1.2.1: When CJI is transmitted outside the boundary of the physically secure location, the data shall be immediately protected via encryption that is FIPS 140-2 certified.
- Section 5.10.1.2.2: When CJI is at rest (i.e. stored digitally) outside the boundary of the physically secure location, the data shall be protected via encryption with the same standard mentioned above or use a symmetric cipher that is FIPS 197 certified (AES) and at least 256-bit strength.
Authorized by FedRAMP and GovRAMP for Trusted Data Security
Virtru makes it easy for any organization to protect and share sensitive data — from small municipalities to the federal government, across the defense industrial base, and beyond.



Enable CJIS Compliance in the Cloud with End-to-End Encryption

Support your need to collaborate internally and with external agencies, and unlock digital workflows to support remote government workers and distributed agency teams.
Virtru’s data-centric, end-to-end encryption and granular access controls help protect CJI stored in or shared via email and file systems like Gmail, Google Drive, and Outlook from access by unauthorized users with AES-256 bit encryption, FIPS 140-2 compliant modules, and two-factor authentication.





Customer Reviews for CJIS Compliant Email and File Sharing
Unlock CJIS Compliance for Digital Workflows
Privacy and Compliance
End-to-end encryption prevents unauthorized access to email and files containing CJI and maintains the privacy of citizens’ PII, supporting CJIS compliance.
Secure External Data Sharing
Persistent protection to govern access throughout the data lifecycle, with the option to host your own encryption keys.
Ease of Use
Boost user adoption and deliver simple recipient access that naturally fit into workflows between users, admins, and agency partners.
Data Stays in the U.S.
Virtru hosts everything in the U.S., uses encryption algorithms that comply with FIPS 140-2, is FedRAMP authorized at the moderate impact level, and adheres to the security controls defined by NIST SP 800-53. Virtru cannot access your protected data at any time.


“By enabling full compliance for our law enforcement agency, Virtru gave us a path toward a complete cloud migration.”
Susan Lyon
Google Cloud Team Manager, State of Maryland
CJIS Compliant Data Workflows
With Virtru, you can keep CJI protected and controlled, without sacrificing the ability to collaborate.
/Updated%20Solutions%20Pages/law-enforcement-office-01.webp)
Easy End-to-End Encryption for CJIS-Compliant Cloud Workflows
Without end-to-end encryption, use of cloud services requires CJIS-specific background screening and training for cloud vendor personnel and specialized SLAs and/or contractual clauses that compound costs and delay deployments.
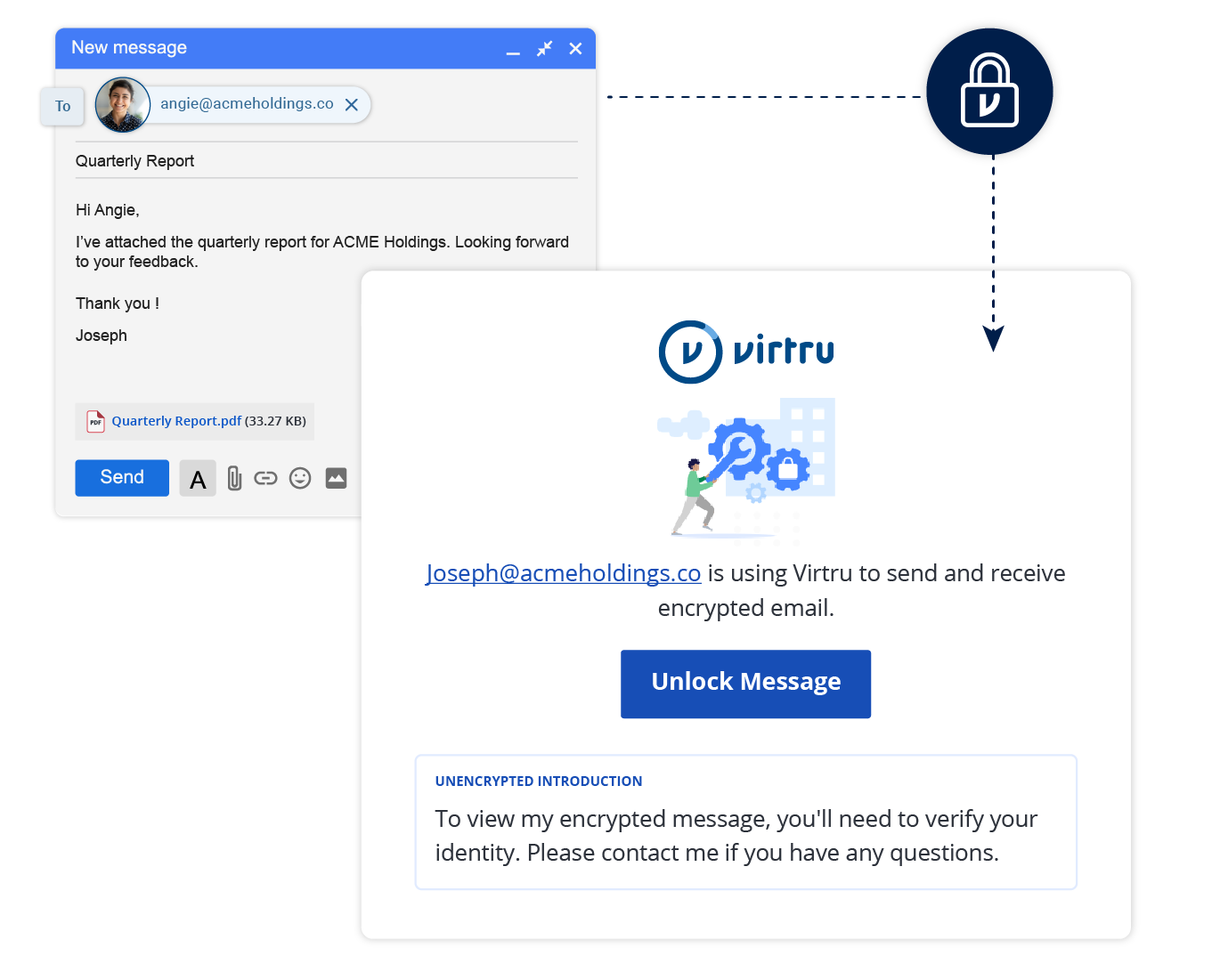
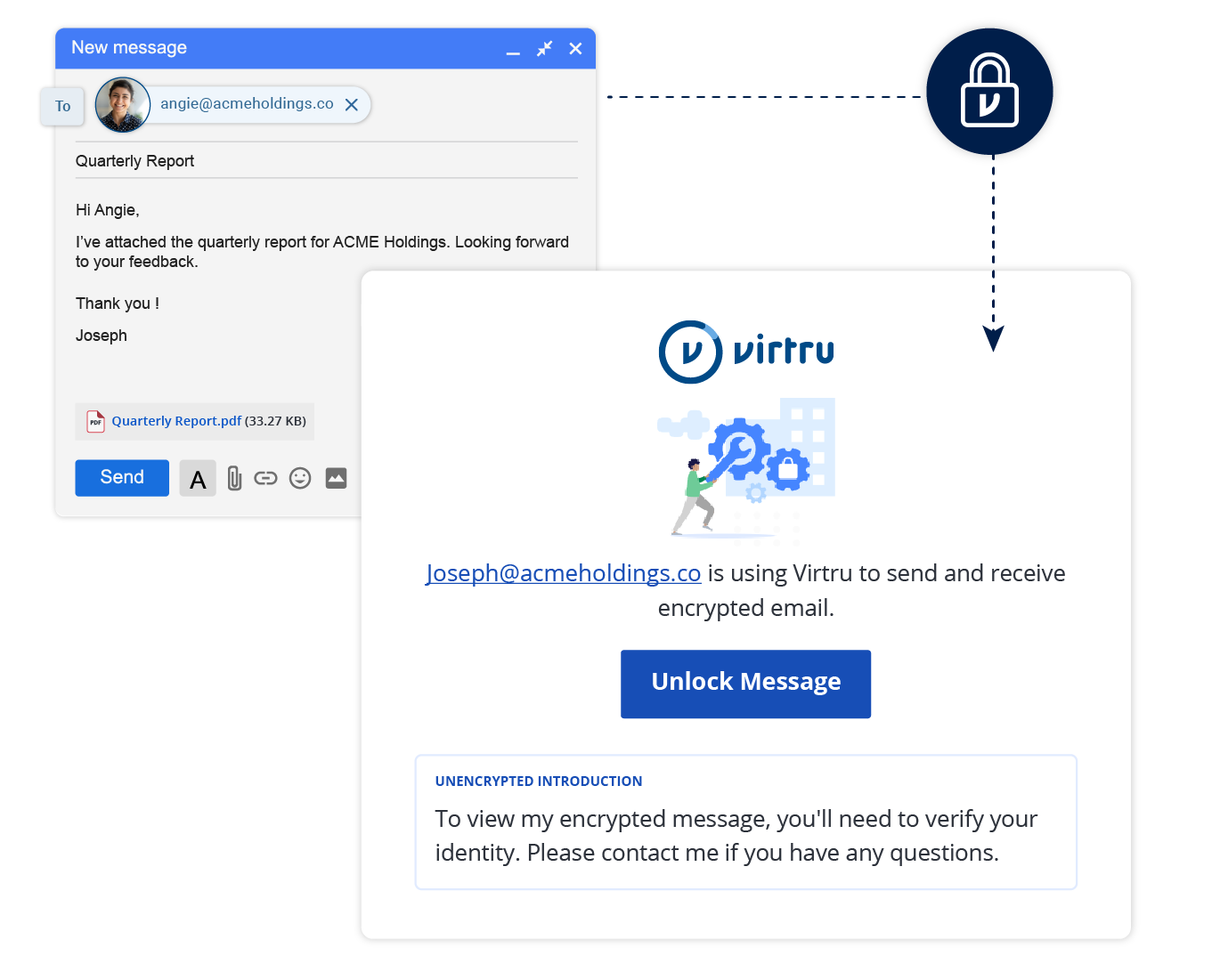
Virtru’s end-to-end encryption streamlines CJIS compliance in the cloud by preventing vendor personnel from accessing CJI. Transparent key exchanges avoid complexities of other end-to-end encryption approaches like PGP and S/MIME for enhanced adoption and usage

Easy, Secure Collaboration to Get the Job Done
Provide law enforcement agency employees and administrators easy-to-use data protection, embedded in existing applications. Complement user protections with DLP rules that automatically enforce encryption and control.
Enable seamless access for recipients and collaborators at external agencies and departments, without requiring new accounts, passwords, or software, for digital sharing workflows that support rapid delivery of services that support public safety.

Control and Visibility For CJI Data Sharing
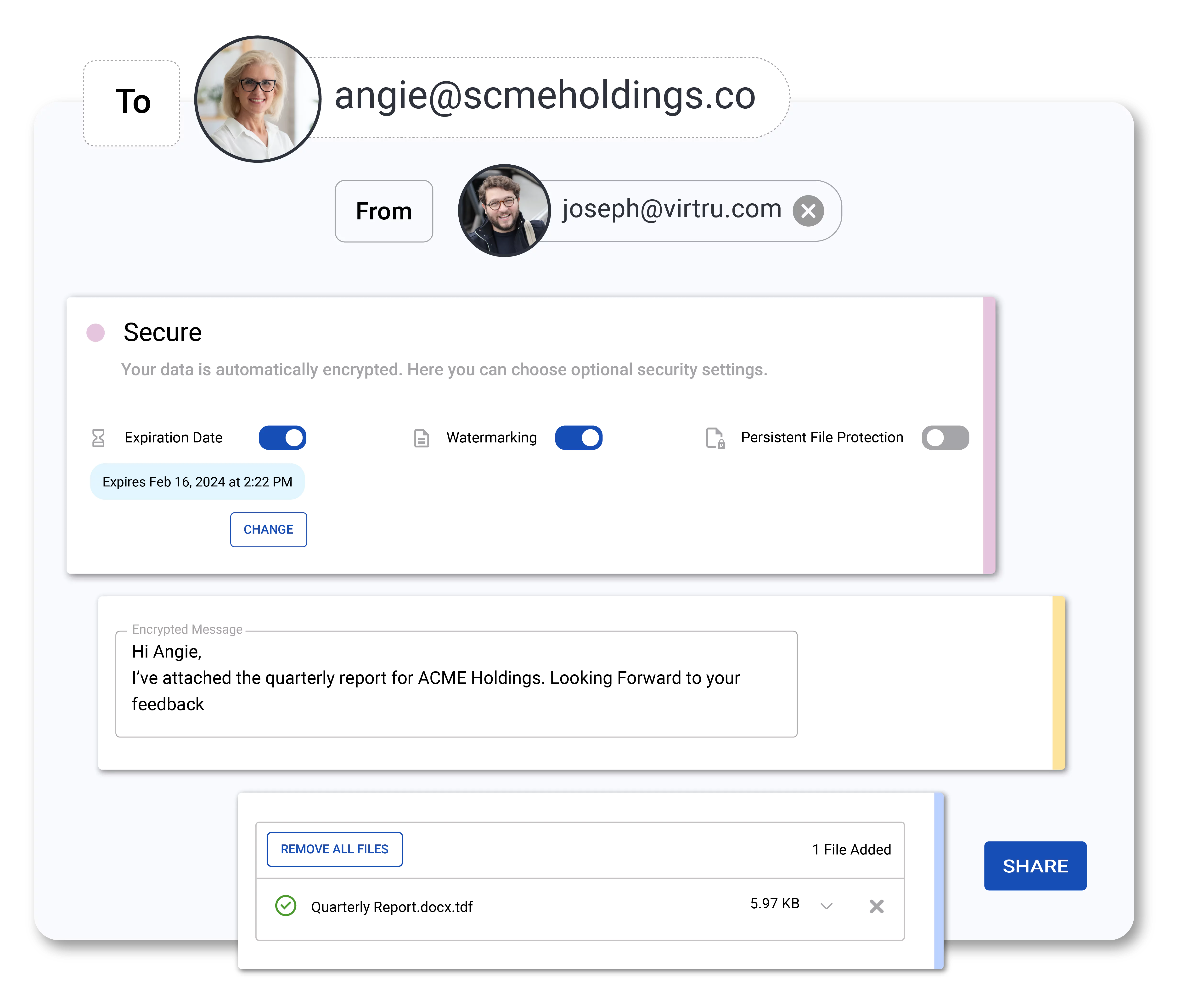
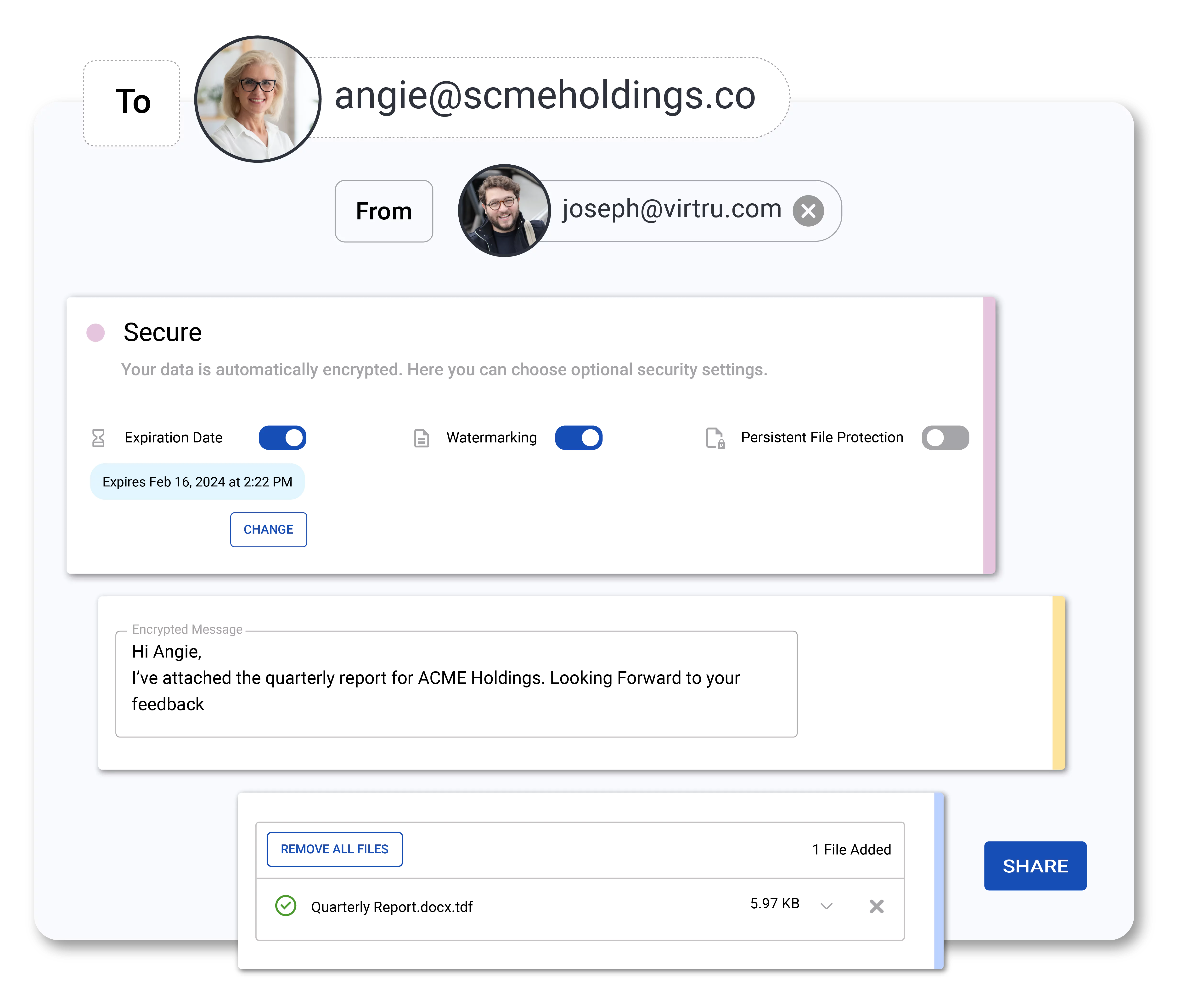
Enable secure data sharing, aligned with CJIS compliance, across agencies with attribute-based access controls (ABAC) for CJI that enable instant access revocation, expiration, disable forwarding, and document watermarking capabilities.
Audit who has accessed CJI, when, where, and for how long. Export event logs for analysis, or integrate with your SIEM for advanced threat analysis.
Maintain ultimate control of the encryption keys protecting all sensitive CJI stored and shared in the cloud with the Virtru Private Keystore.
Resources
Get expert insights on how to address your data protection challenges.
Ready to take the next step?
6,100 CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.

Book a Demo
Become a Partner
Contact us to learn more about our partnership opportunities.
Become a Compliance Champion
Contact us to learn more about our partnership opportunities.


