Strengthen CMMC Compliance with Virtru Data-Centric Security
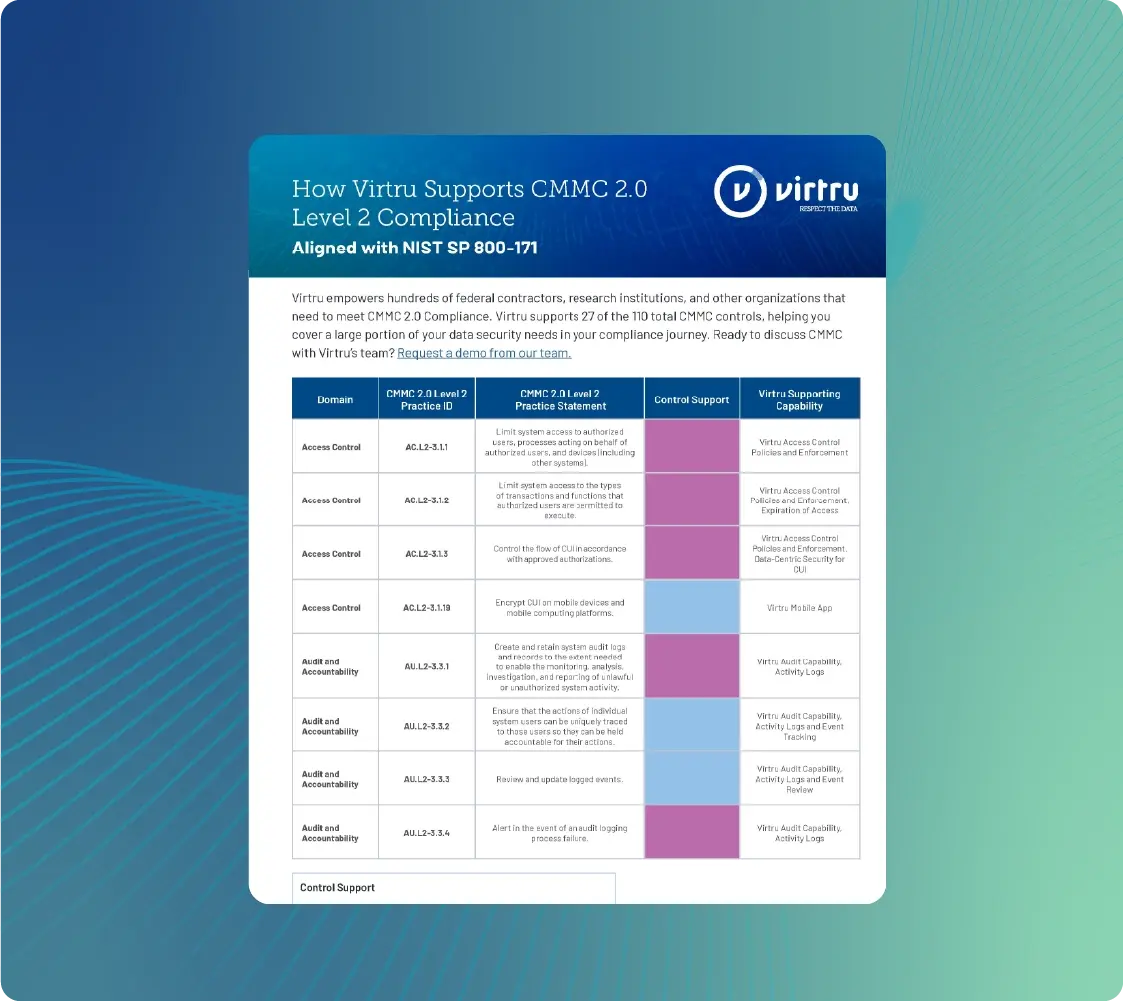
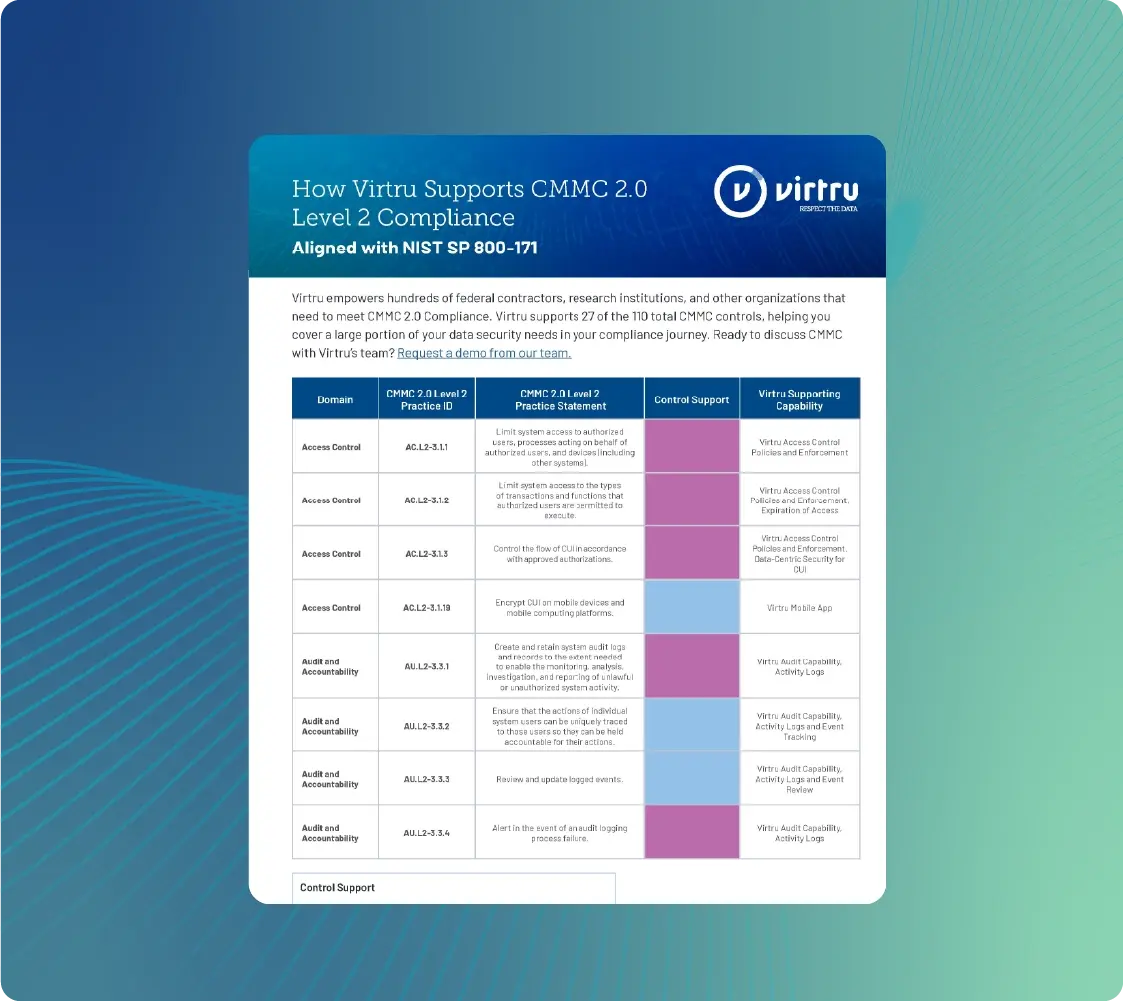
Protect Controlled Unclassified Information (CUI) everywhere it’s shared with Virtru's FedRAMP Authorized Data Security Platform. Virtru supports NIST and DFARS requirements and CMMC Level 2 Compliance.
Protect CUI with Virtru's FedRAMP Authorized Platform
As CMMC 2.0 enforcement rolls out, defense contractors that handle CUI need fast, affordable, and effective data encryption and access control to protect CUI. Virtru addresses 27 of 110 Level 2 controls.
Virtru Collaborate gives your teams a FedRAMP authorized workspace for storing and sharing sensitive files, including CUI, for CMMC Level 2 compliance. No new accounts or passwords needed, and security follows the data wherever it moves.
Compared to other solutions like PreVeil, Proofpoint, and Kiteworks, Virtru is:
- Easier to use — no new usernames or passwords for senders or recipients.
- More affordable, and right-sized to your organization's needs.
- Faster to deploy, with limited deployment required
- More flexible for growing teams
- FIPS 140-2 Validated and FedRAMP Authorized
/Virtru%20DSP%20FedRamp.webp)
Virtru’s easy end-to-end encryption and granular, attribute-based access controls (ABAC) can be deployed quickly, across your organization's most commonly used apps and systems. Protect CUI stored and shared via Gmail and Outlook email with Virtru's client-side email encryption plugins, plus support secure file exchange for large files up to 15 GB with Virtru Secure Share.
Virtru supports all Google Workspace SKUs, Google CSE, Microsoft Commercial Cloud, Microsoft Government Cloud, and GCC High.
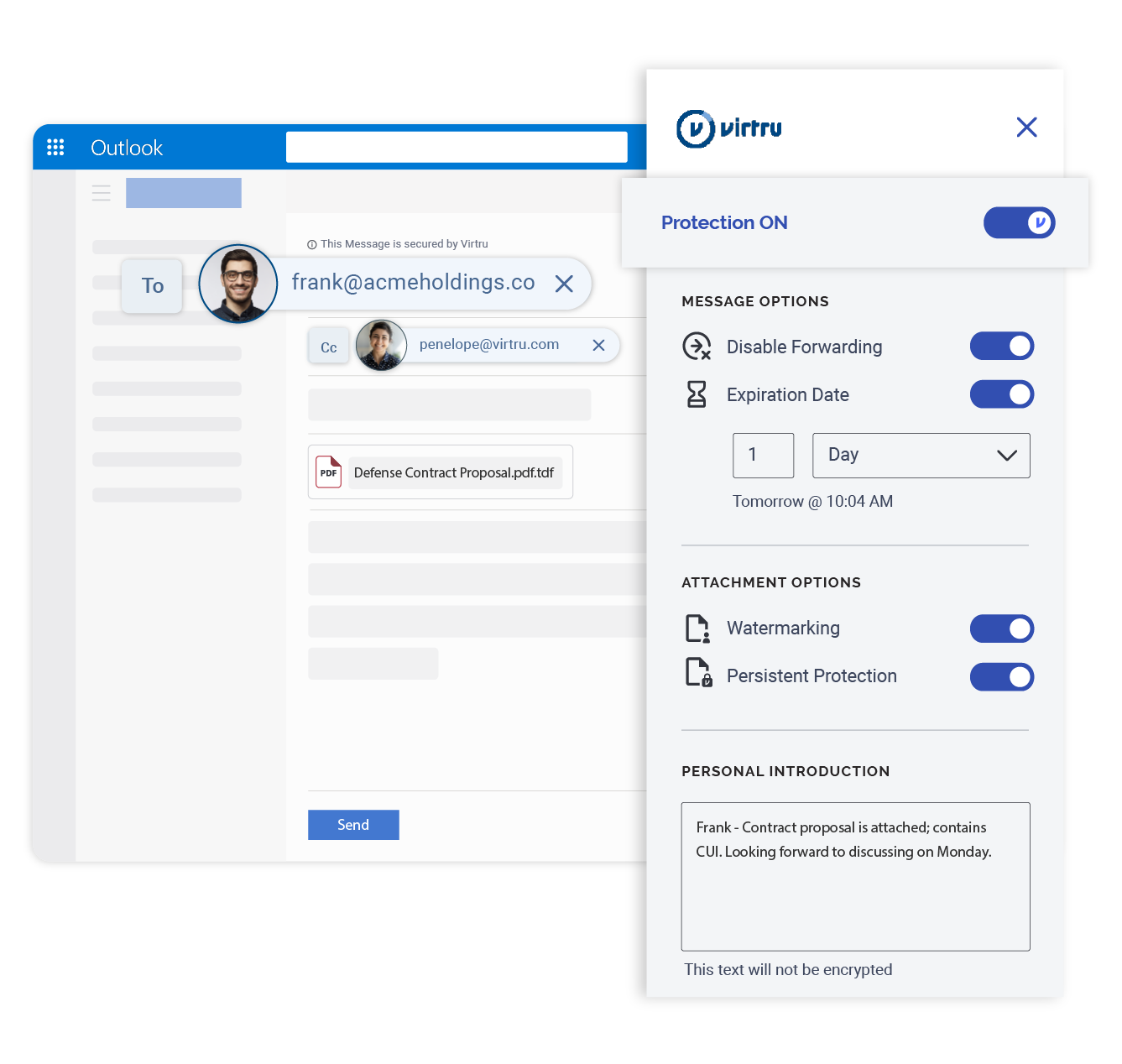
Deploy Virtru in minutes, without needing to set up complicated mail routing or gateways. Easily roll out end-to-end encrypted email and protect shared files containing CUI so that you can seamlessly work with external primes, subcontractors, agencies, and other mission partners.
Virtru supports safeguards outlined in DFARS 252.204-7012 and access controls for CUI within NIST SP 800-171 and NIST SP 800-172.

/Virtru%20DSP%20FedRamp.webp)

Collaboration without Compromise
Why Choose Virtru for CMMC?
Unlike other CMMC vendors, Virtru does not overpromise: We are precise about which CMMC controls we address, and our FedRAMP authorized platform provides peace of mind for CUI at rest and in transit.
Protect CUI with FedRAMP Authorized Security
There's a big difference between "FedRAMP Authorized" and "FedRAMP Equivalent."
Don't settle for "FedRAMP Equivalent," which increases your risk and responsibility. Virtru is FedRAMP Authorized at the Moderate level and boasts FIPS 140-2 Validated encryption for trusted, vetted data security.
Why FedRAMP Authorization Makes a Big Difference
Seamlessly Share CUI Externally, Across Environments
Support your contracting and supply chain collaboration workflows with easy, platform-agnostic sharing.
Virtru provides granular access control and detailed audit trails, helping you maintain persistent control and visibility over shared data. Virtru lets you keep your CUI in a FedRAMP Authorized environment at all times, even when you share it outside your perimeter.
Control and Audit CUI
A Secure, Cost-Effective Alternative to Microsoft Gov Cloud
Small and midsize contractors use Virtru for right-sized encryption for as few as 5 users, scaling with them as they grow.
Microsoft GCC High isn't required for CMMC compliance. With Virtru, you can manage CUI securely, in a FedRAMP authorized environment, even if you use Microsoft Commercial Cloud for your business workflows.
Discover Virtru for CMMC in Microsoft
Maya HTT Gets CMMC L2 Certified with Virtru

FedRAMP Authorized Platform for Seamless Data Security
Virtru blends easy-to-use software with military-grade security for powerful collaboration and data control.
Learn about our Solutions

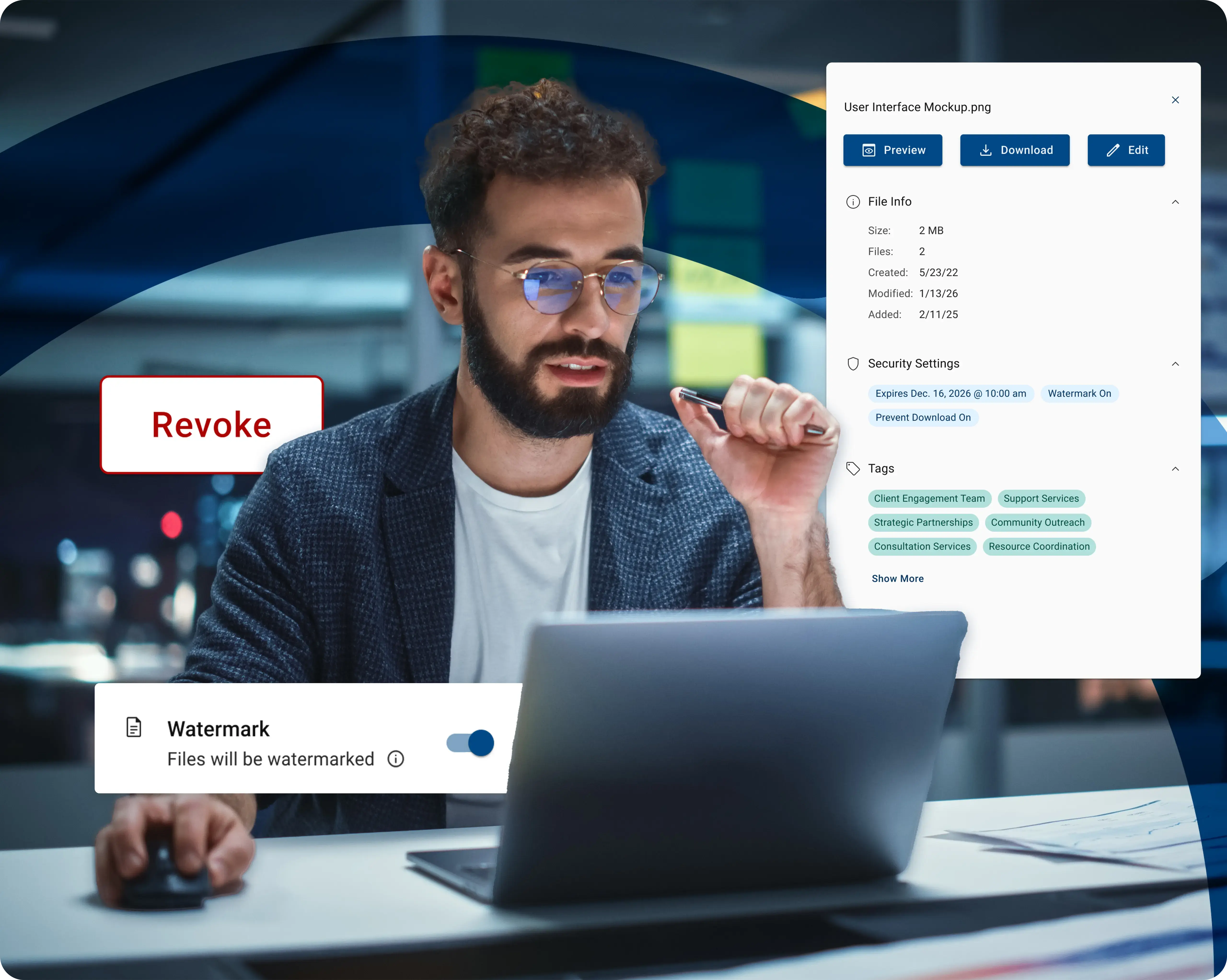
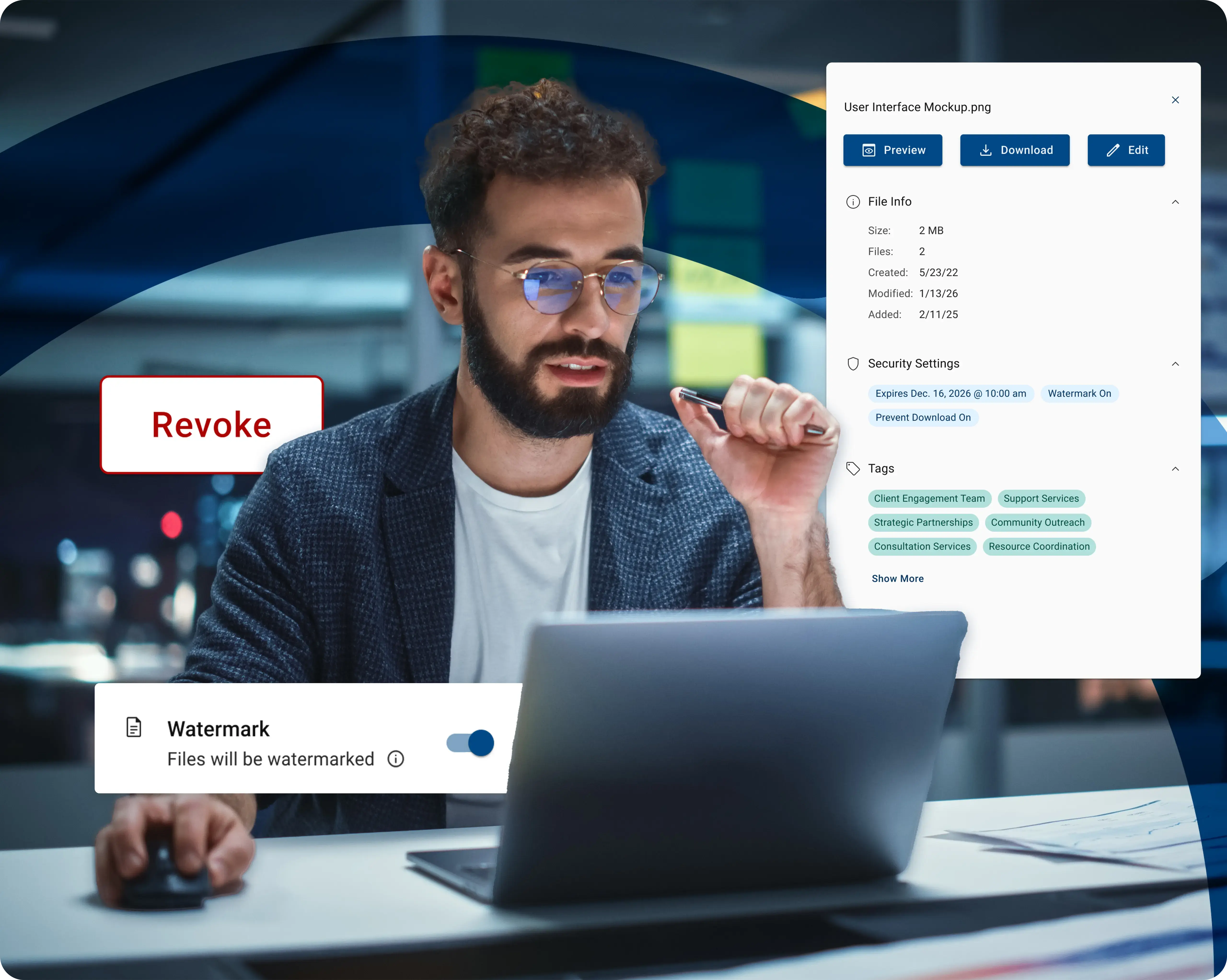
"Another reason we chose Virtru is because if someone accidentally exposes CUI, you can just kill the link and revoke access—unlike with competitors, where you can't retract the data after sharing."
Cybersecurity Specialist
Virtru Customer, International Certification and Registration Company
Zero Trust Data Sharing for DoD Contractors
With Virtru, defense contractors can strengthen their Zero Trust postures aligned with the DoD Zero Trust architecture. The DoD highlights the data pillar as the central element of Zero Trust, and Virtru protects data in motion and at rest.
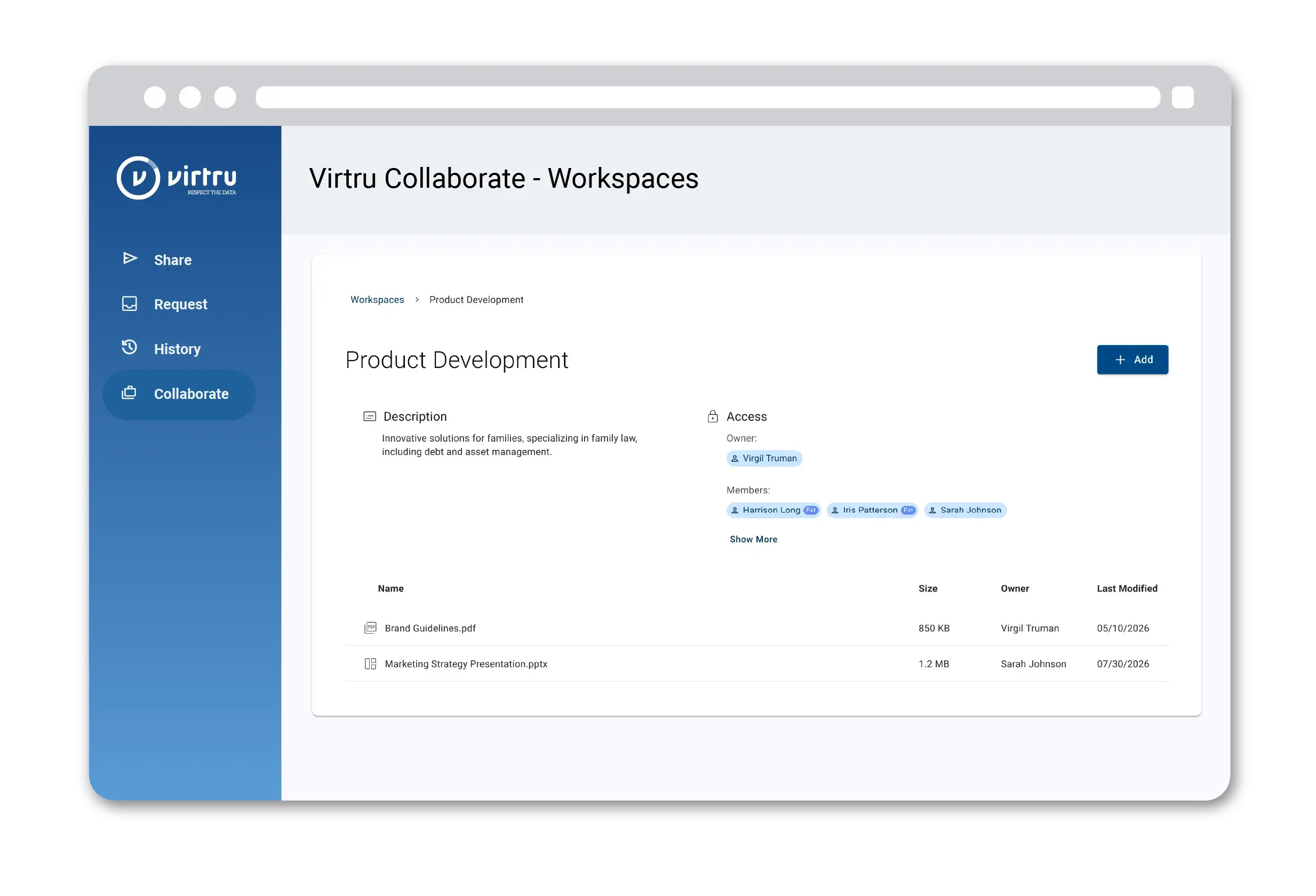
Store, Organize, Share, and Control CUI Files
When your enclave is too restrictive and you need a secure workspace for sharing CUI with internal and external partners, Virtru Collaborate provides a secure, FedRAMP authorized environment for teams to work together — while maintaining strict security and granular access control.
Virtru Collaborate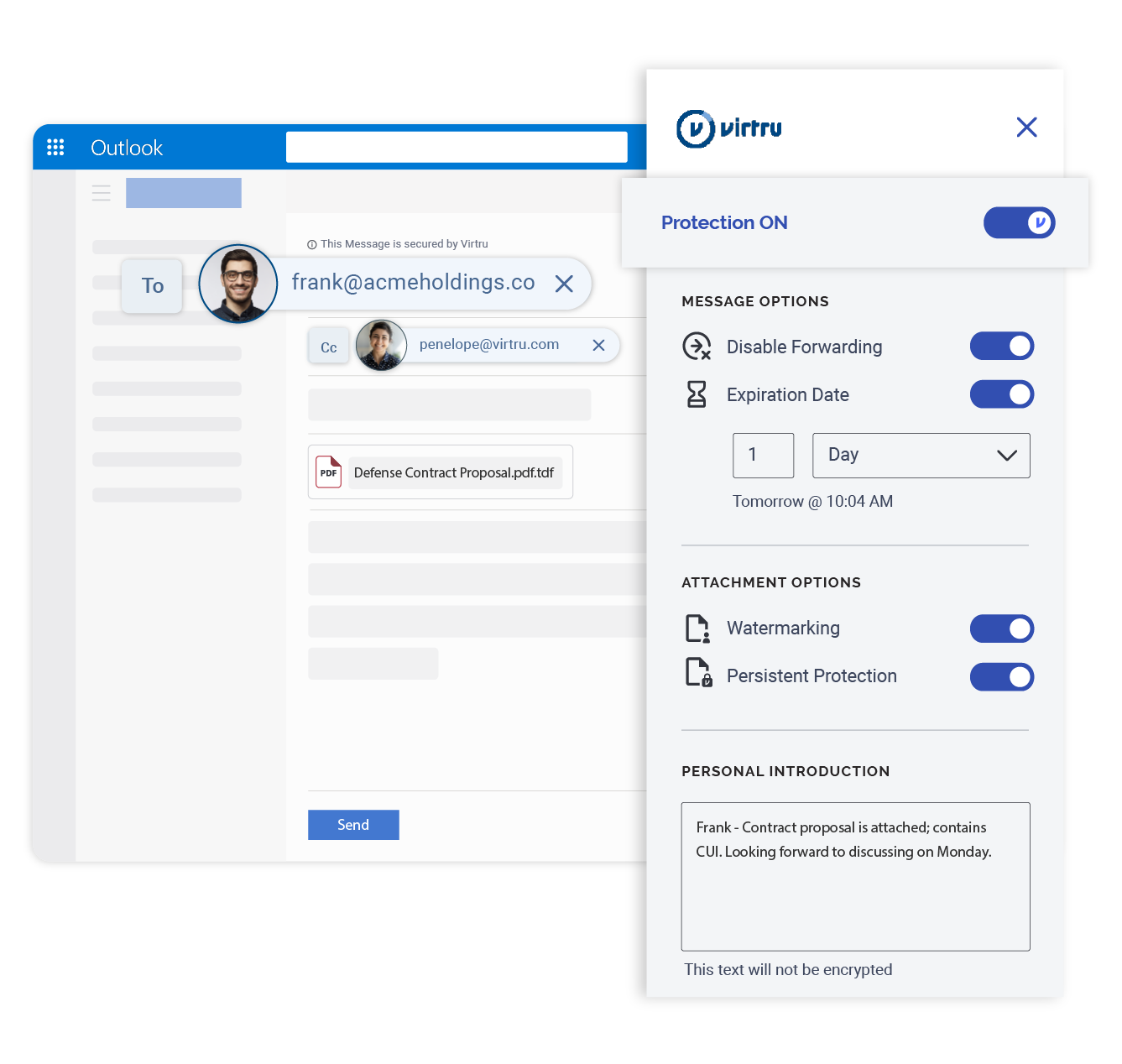
Avoid the High Cost of Living on GCC High
For many defense contractors, the high cost of living on GCC High can be prohibitive. Virtru offers an alternative to GCC High to support CMMC compliant, FedRAMP Authorized CUI sharing in Microsoft 365, without breaking the bank.
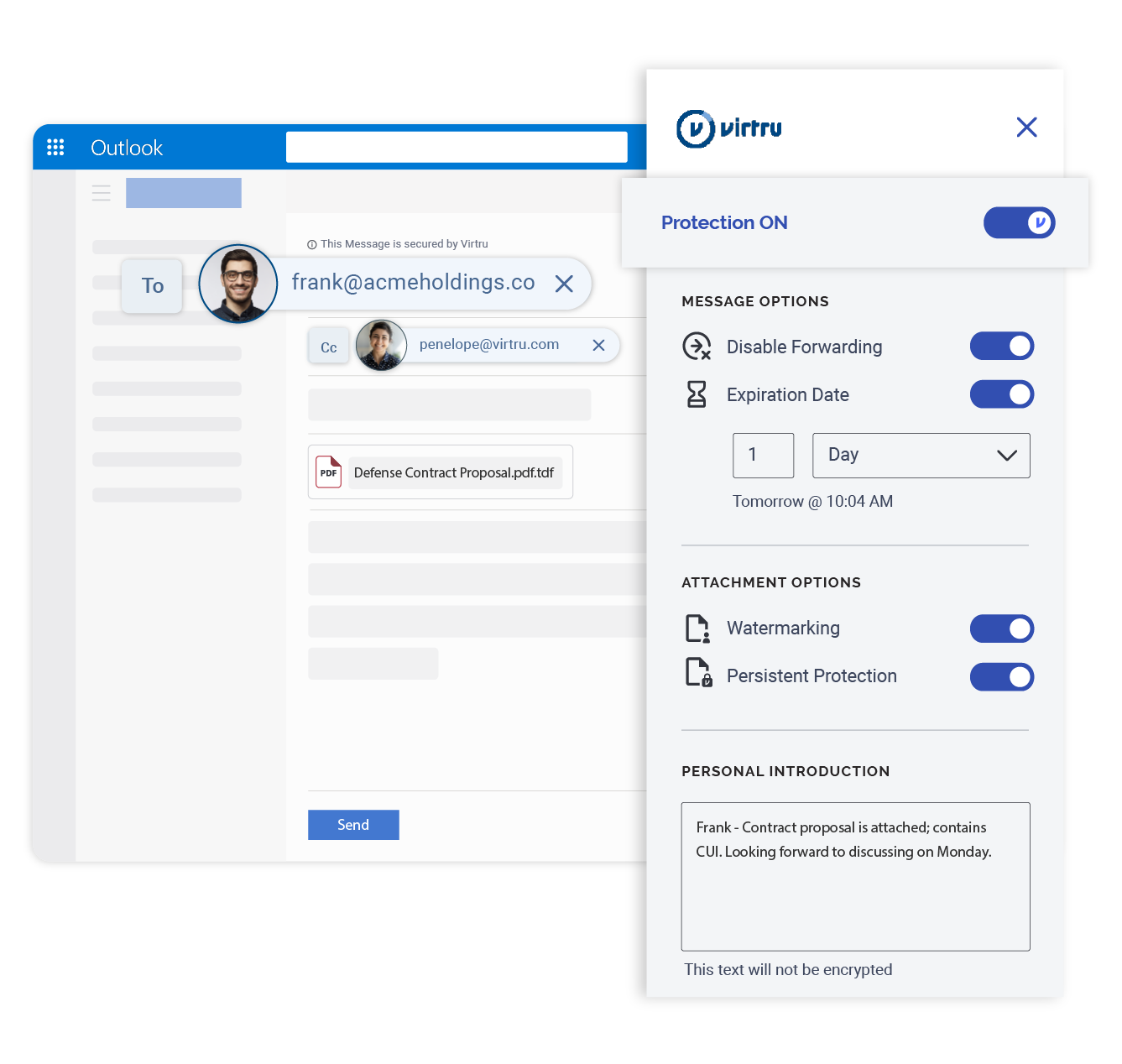
End-to-End Email Encryption for CUI in Transit and at Rest
Virtru won't disrupt your workflow: Our end-to-end email encryption solutions integrate seamlessly with Gmail and Outlook and are FedRAMP-authorized and FIPS 140-2 validated, supporting NIST security requirements.
Email Encryption/blog%20-%20versatile%20TDF/Versatile%20TDF%20Blog.webp)
Complete Data Control for CUI
Powered by the Trusted Data Format, Virtru lets you revoke access immediately, set expiration, disable forwarding, and watermark documents to maintain control of CUI.
Audit who has accessed CUI, when, where, and for how long. Export event logs for analysis or integrate with your SIEM for advanced threat intelligence.
Protect CUI with the Trusted Data Format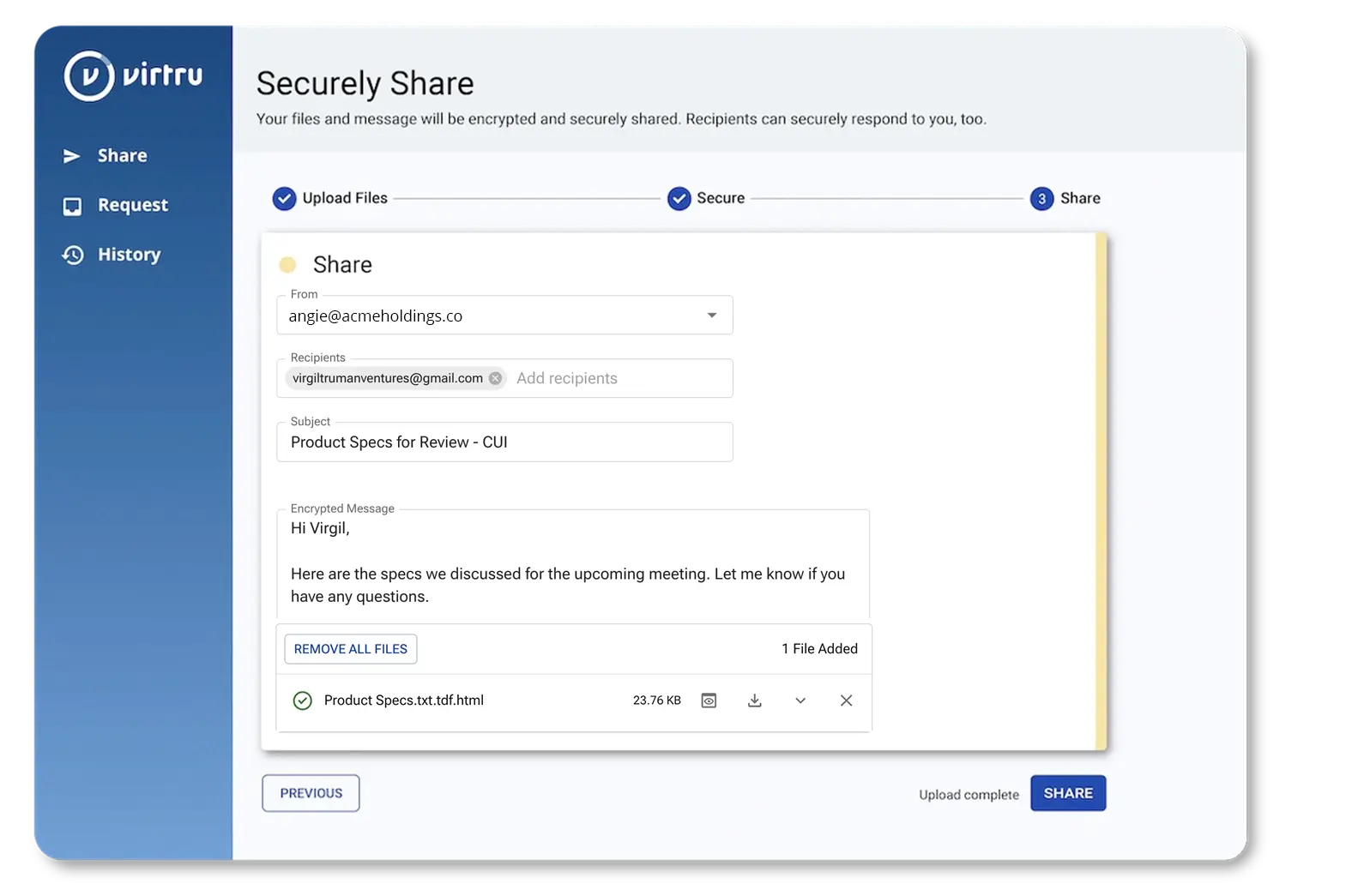
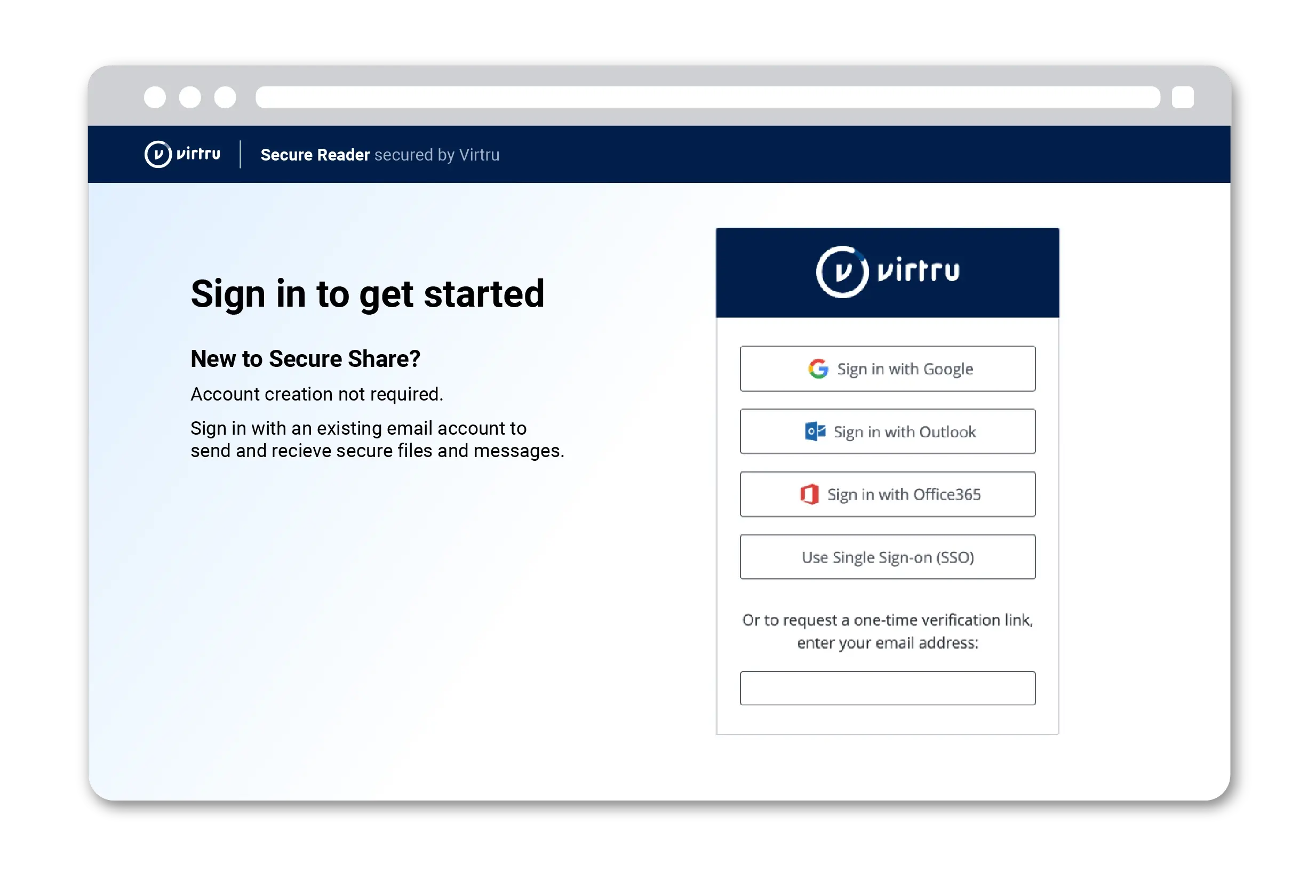
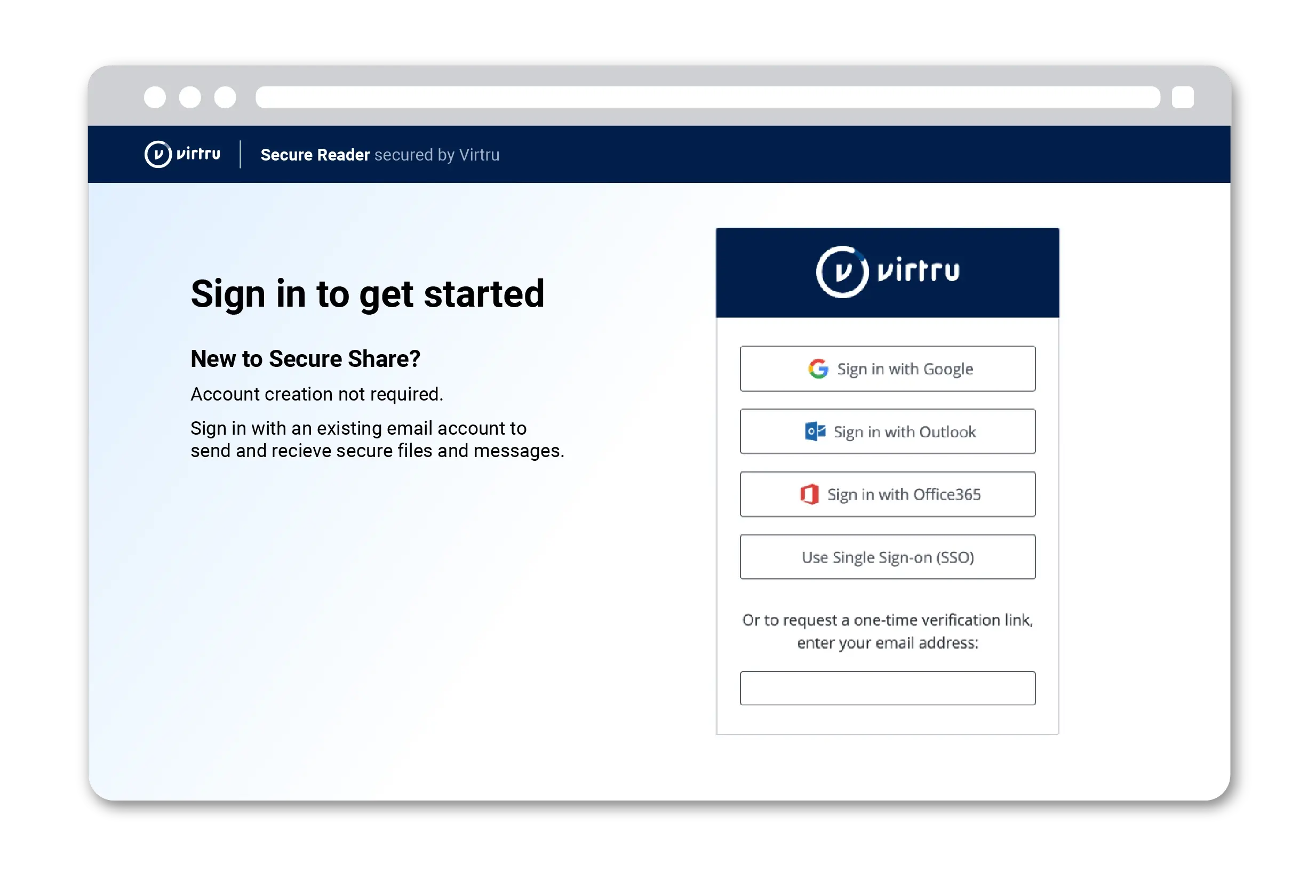
Seamless File Sharing Across Partners
Virtru alleviates the friction of external CUI sharing. Send and receive encrypted files containing CUI, with the confidence that it remains in a FedRAMP authorized environment. Revoke access, change permissions, and request files from external contacts, regardless of whether they use Microsoft or Google.
Virtru Secure ShareMaintain Control of Your Encryption Keys
You have the option to control your organization's private encryption keys with Virtru Private Keystore, which allows you to manage your keys separately in the location of your choice: on premises, or in a public or private cloud. Watch the video to see how defense contractor SHE BASH uses Virtru Private Keystore for CMMC compliance in Google CSE.
Virtru Private Keystore/blog-cmmc-august-2024/cmmc-2-august-update_FINAL.webp)
“It's very rare that we get a vendor with this type of acumen and reputation… It was different. It was refreshing. You made my job easy.”
Chief Security Officer
Fortune 500 engineering firm using Virtru and Microsoft Commercial Cloud for CMMC compliance
Customer Reviews
CMMC Success Stories

What It's Like to Work with Virtru for CMMC
"Virtru Private Keystore and CSE saved us from migrating to an expensive Microsoft GCC setup. I was extremely surprised when I asked for a quote for the CMMC package for Virtru and was given something as reasonable as I was given."
Cameron Banowsky
CTO
SHE BASH
Read the Case Study
/resource%20-%20forge%20institute/forge%20logo.png)
"Forge works with a lot of small businesses in the defense industrial base, and they don't always have their own IT or cybersecurity folks. They need plug-and-play options, and Virtru is a great solution for small businesses that need to quickly turn on this type of capability."
Lee Watson
Chairman and CEO
Forge Institute
Read the Case Study
/office-windows-1.webp)
Exposure Management Company Uses Virtru to Encrypt Sensitive Communications
"It has become the de facto standard because more people than what I would consider to be in ‘sensitive’ roles are using the capability. There are definitely groups of people who tend to handle sensitive data more frequently that have established muscle memory around the use of Virtru."
Chief Security Officer
Exposure Management Company
Read the Case Study

What It's Like to Work with Virtru for CMMC
"Virtru Private Keystore and CSE saved us from migrating to an expensive Microsoft GCC setup. I was extremely surprised when I asked for a quote for the CMMC package for Virtru and was given something as reasonable as I was given."
Cameron Banowsky
CTO
SHE BASH
Read the Case Study
/resource%20-%20forge%20institute/forge%20logo.png)
"Forge works with a lot of small businesses in the defense industrial base, and they don't always have their own IT or cybersecurity folks. They need plug-and-play options, and Virtru is a great solution for small businesses that need to quickly turn on this type of capability."
Lee Watson
Chairman and CEO
Forge Institute
Read the Case Study
/office-windows-1.webp)
Exposure Management Company Uses Virtru to Encrypt Sensitive Communications
"It has become the de facto standard because more people than what I would consider to be in ‘sensitive’ roles are using the capability. There are definitely groups of people who tend to handle sensitive data more frequently that have established muscle memory around the use of Virtru."
Chief Security Officer
Exposure Management Company
Read the Case Study
Ready to take the next step?
6,100 CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.




Book a Demo
Become a Partner
Contact us to learn more about our partnership opportunities.
Become a Compliance Champion
Contact us to learn more about our partnership opportunities.