Advanced Data Security for Compliant Collaboration
Virtru's FedRAMP-authorized encryption solutions support the world's toughest compliance needs — and they make admins' lives easier.
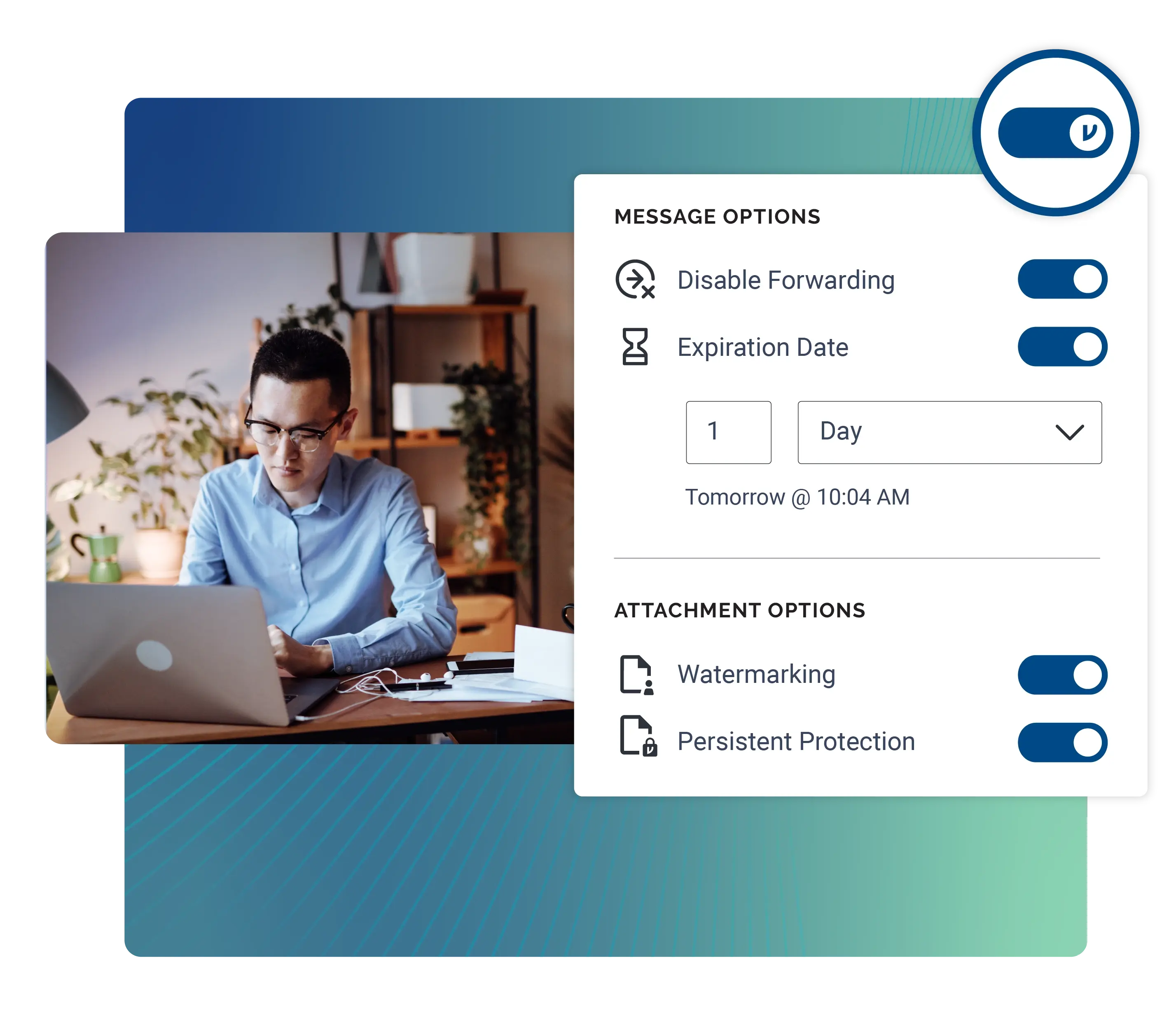
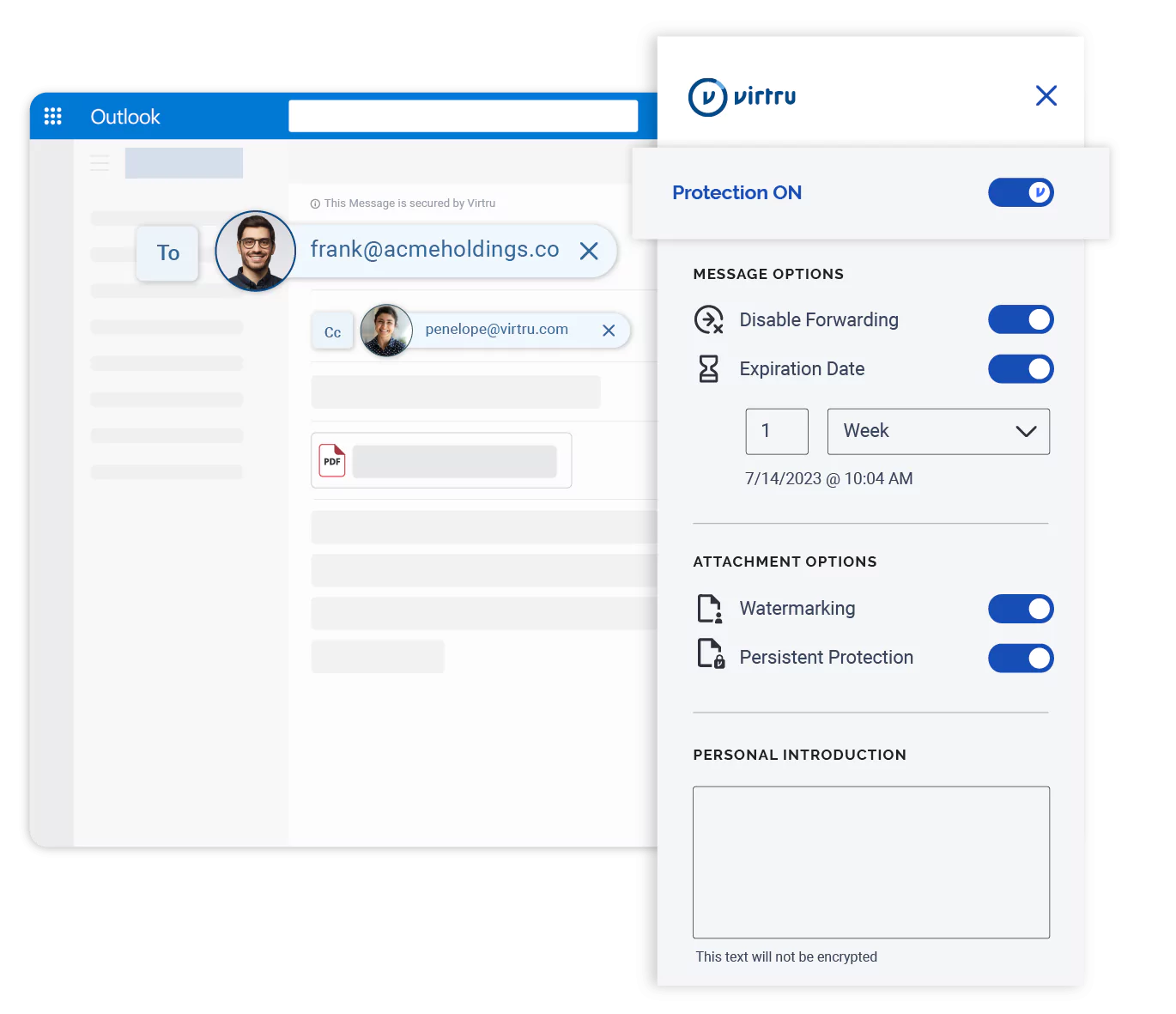
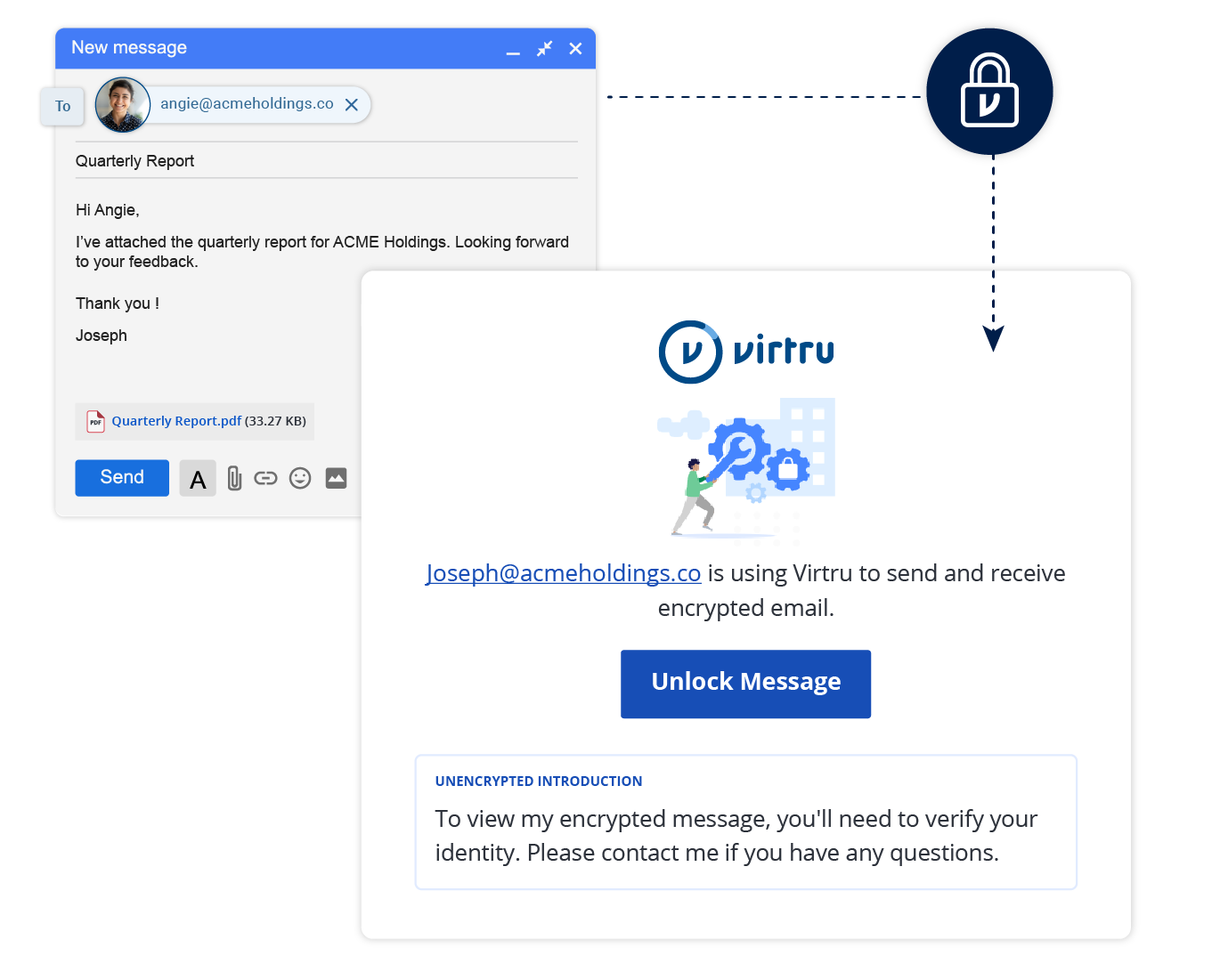
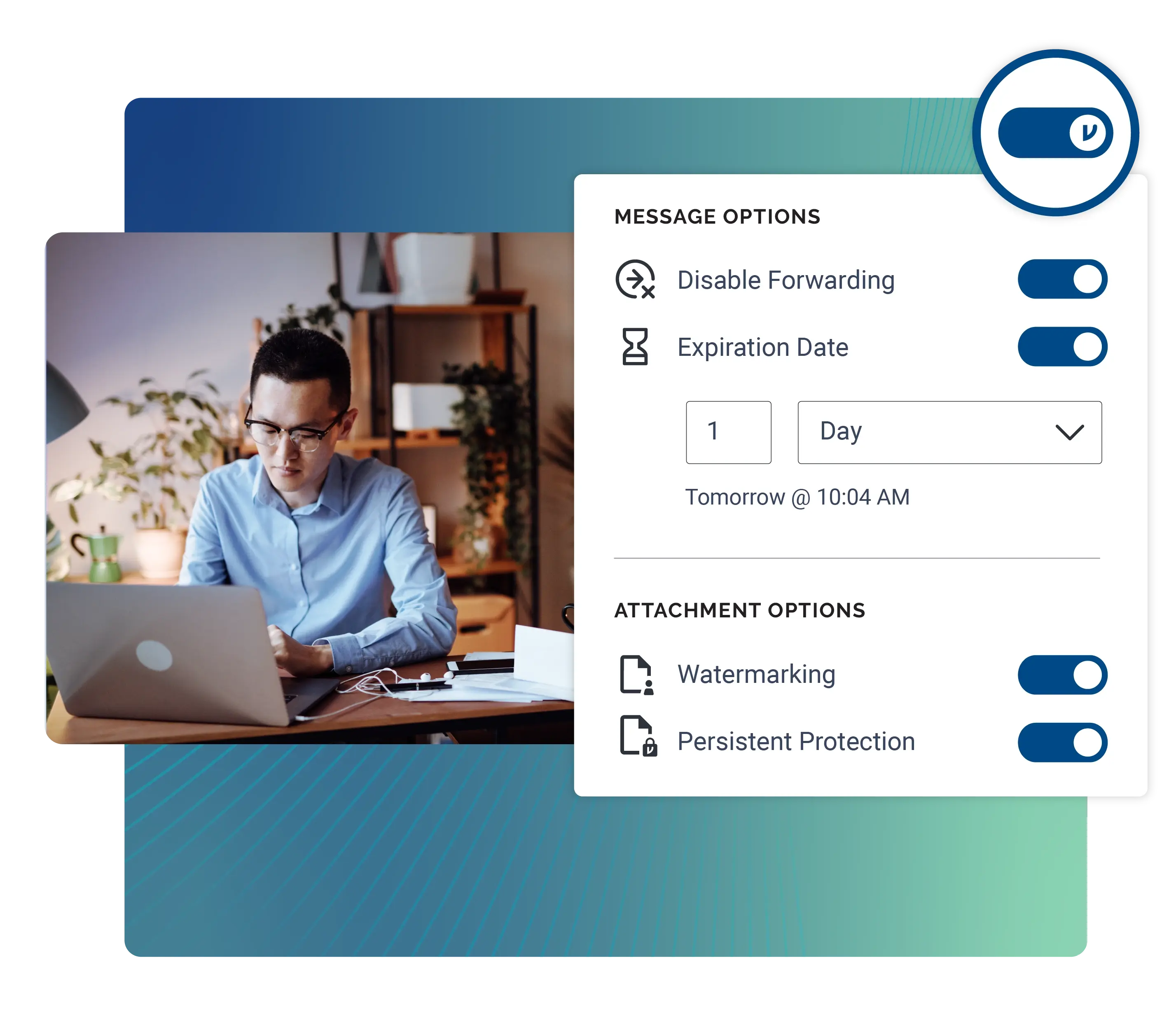
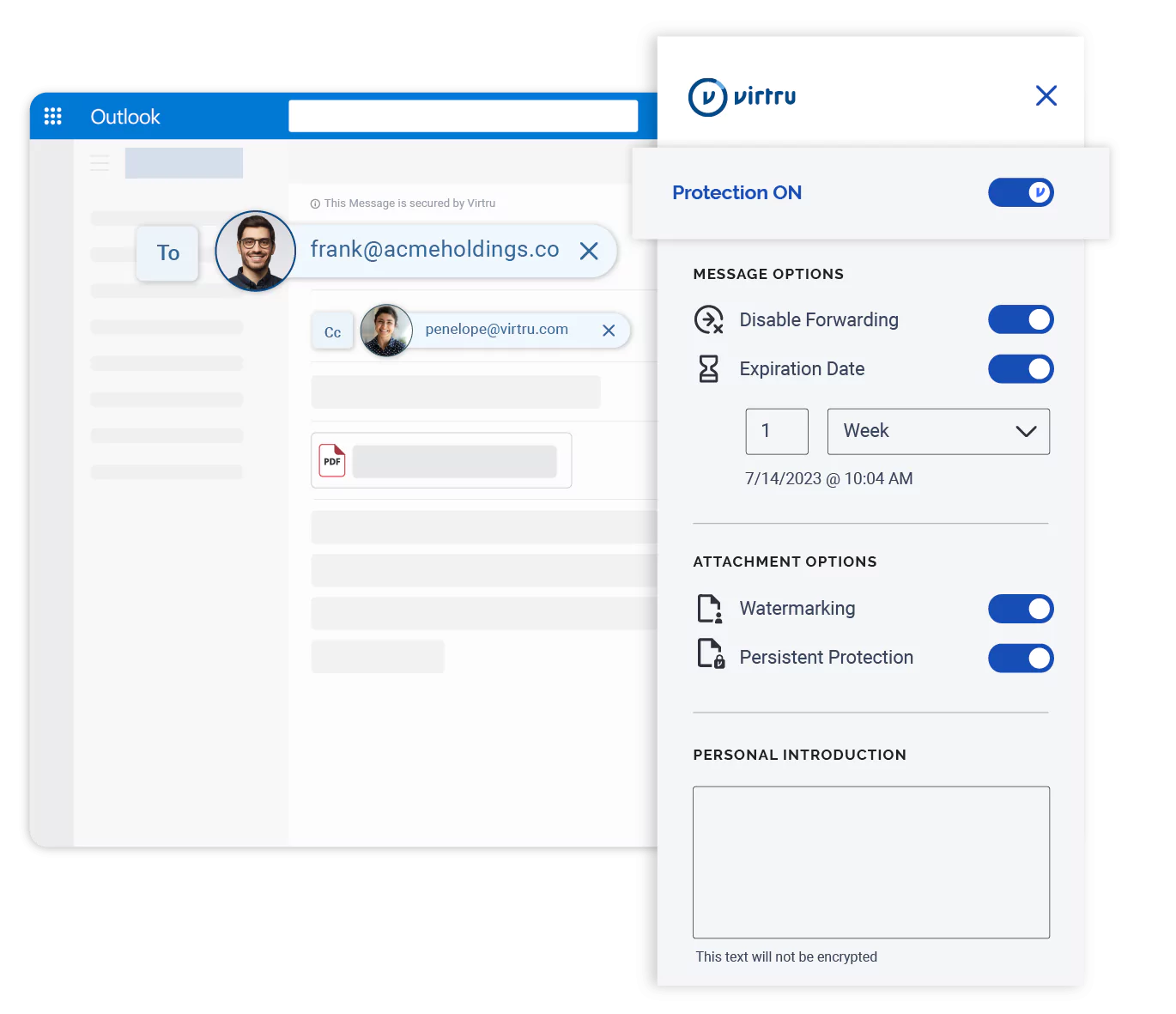
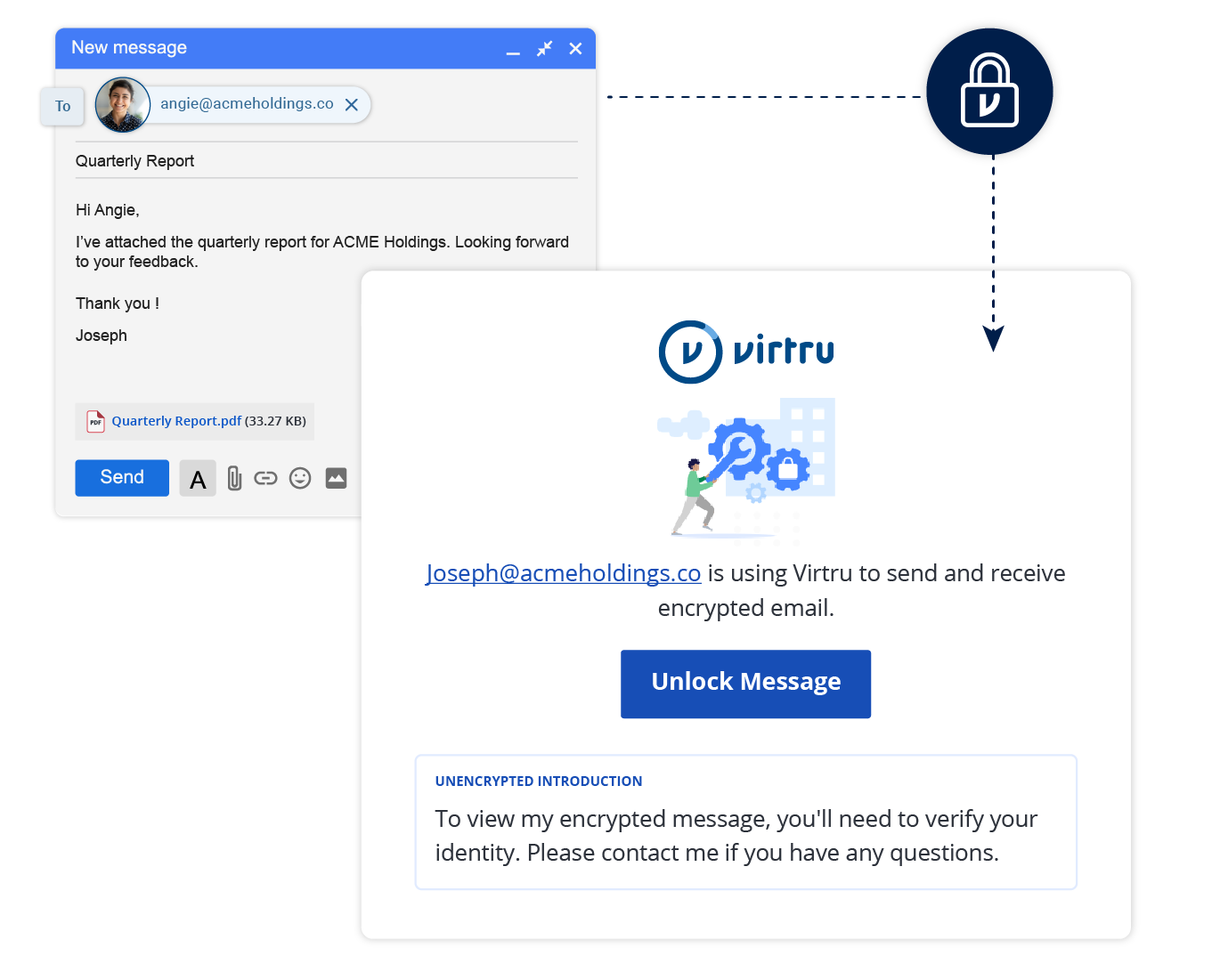
Protect emails and attachments with end-to-end encryption and fine-grained access controls. Virtru integrates directly within email clients like Gmail and Microsoft Outlook for encrypted messaging that’s easy for both senders and recipients to use.

Virtru integrates seamlessly with your email client for simplified data protection.



“We had experience with a traditional, portal-based email encryption product, but our users found this mechanism far too cumbersome for our users and their recipients. With Virtru, we found a solution that met our security and compliance requirements, was easy enough to ensure widespread adoption, and gave us the audit and control features we wanted.”
Mark Dieterich
Director of IT and Security, Brown University
Virtru's client-side encryption tools provide end-to-end encryption that follows data everywhere it moves, giving you control even after content leaves your organization.
Virtru supports compliance with the world's toughest compliance regulations: CMMC, NIST standards, ITAR, CJIS, GLBA, FTC Safeguards, and many more.
Granular audit trails let you see where sensitive content is shared, and revoke access at any point. Virtru provides full visibility into who has accessed or forwarded emails, with SIEM integrations for improved threat remediation.
Virtru's email and file security products are cloud-native and protect sensitive data everywhere it moves. Virtru provides application security for data traveling through SaaS apps like Zendesk, Salesforce, and more.


“We like the control features. For example, being able to revoke a message, and have an audit trail, really sets Virtru apart.”
Dave Steck
VP of IT Infrastructure
Virtru's FedRAMP-authorized encryption solutions support the world's toughest compliance needs — and they make admins' lives easier.

Configure DLP rules and policies to scan email messages and attachments for sensitive data — then apply encryption and granular access control policies before that information leaves your domain.

Detect and protect email and files sent from any connected device, even if users haven’t installed Virtru, with our Data Protection Gateway. Get rapid time-to-value with fully-hosted deployments that seamlessly integrate Virtru with your existing workflow.
Get expert insights on how to address your data protection challenges.
6,100 CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.


Contact us to learn more about our partnership opportunities.