State and Local Government Email and Data Protection
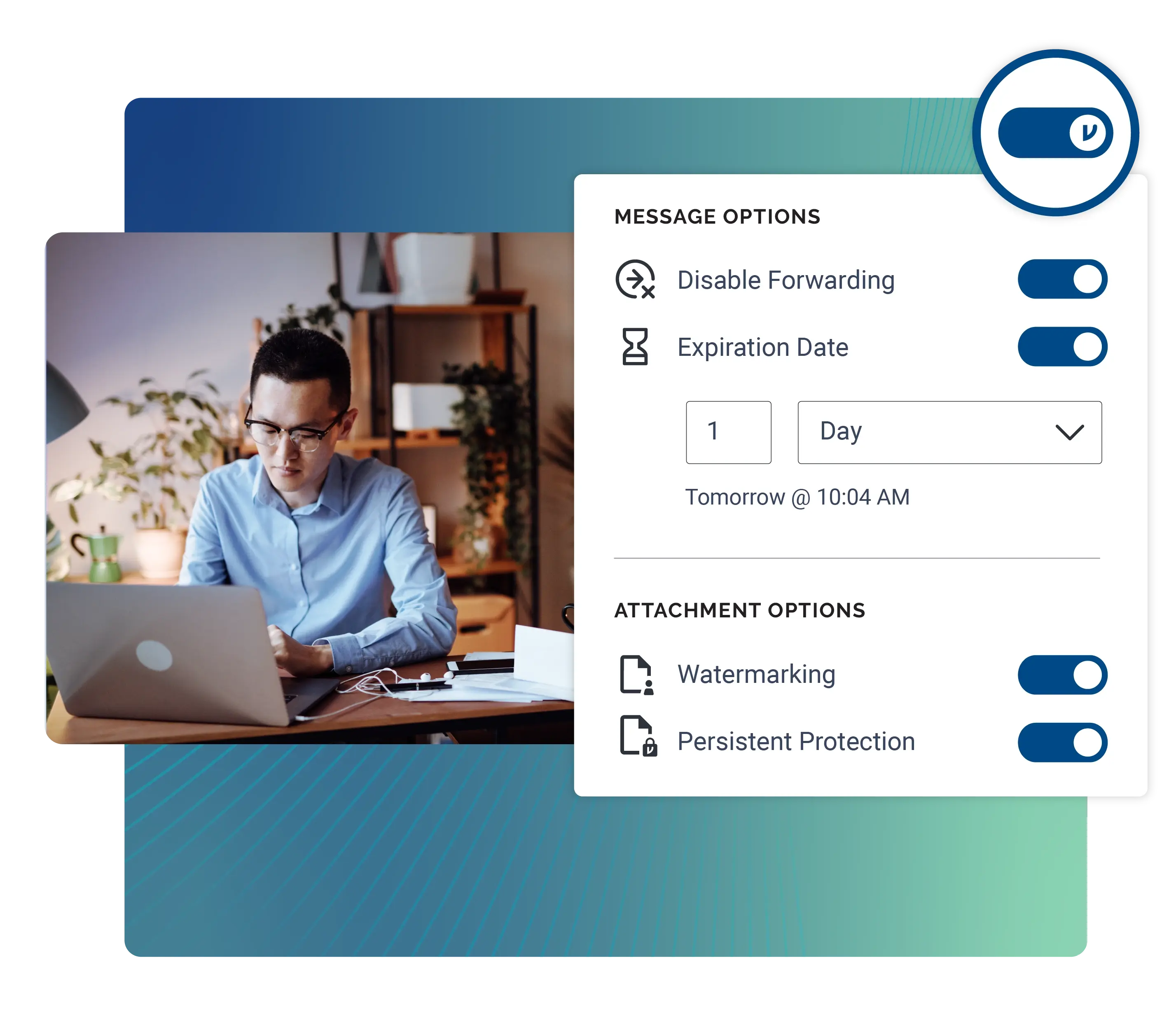
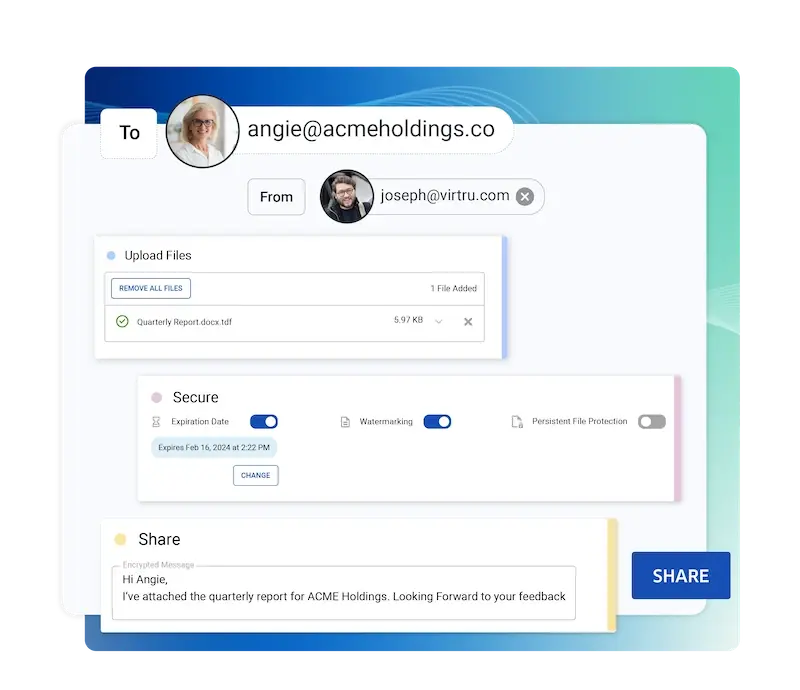
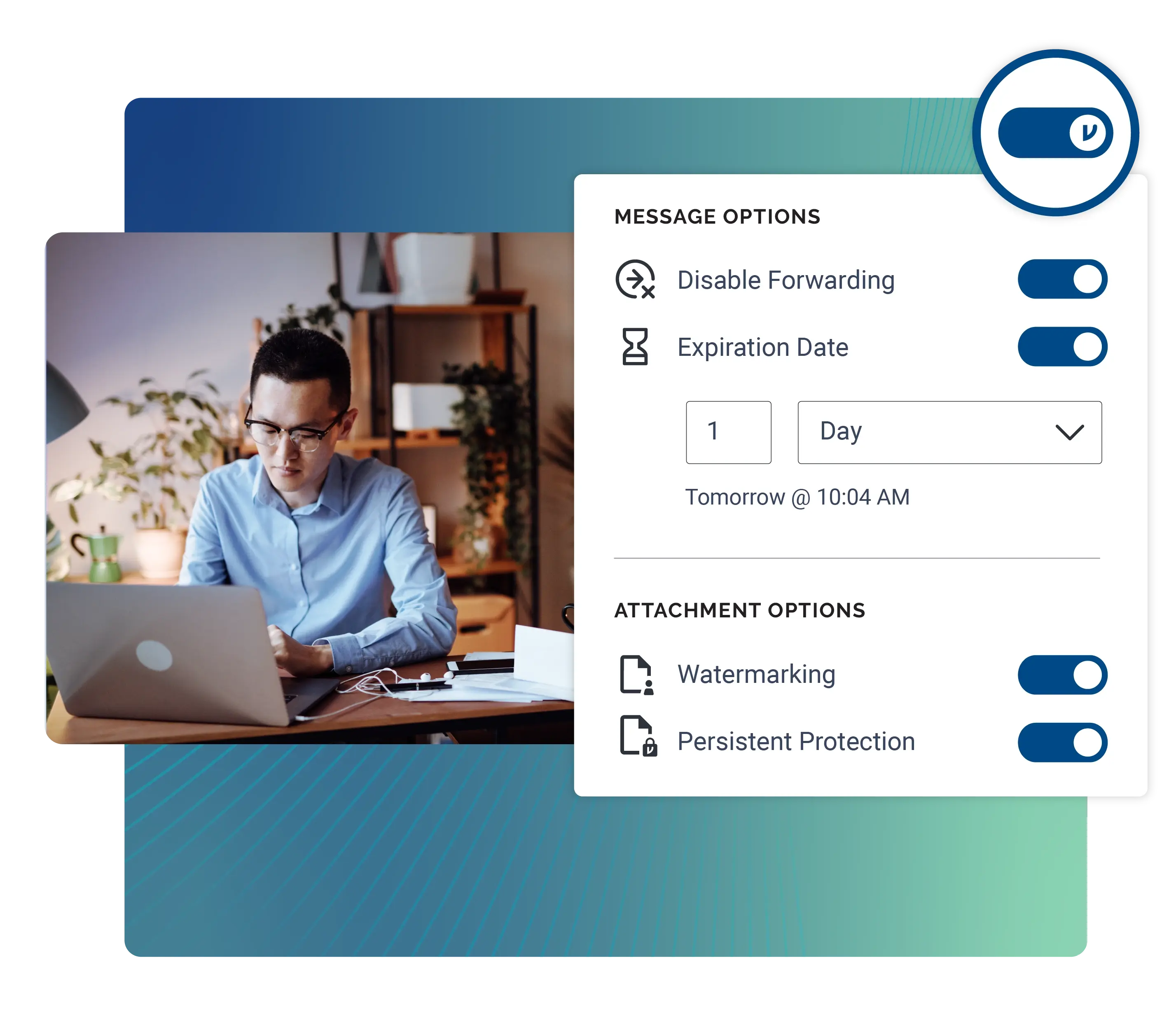
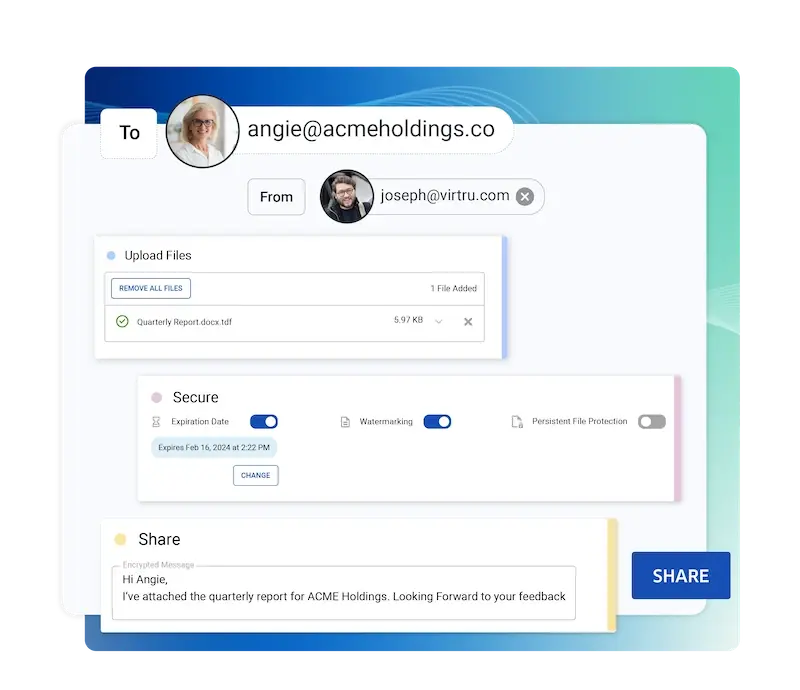
Virtru enables secure, compliant digital government services to facilitate aid to constituents and power cloud migration.
Protect and Control State and Local Government Data
From school districts to police departments, state and local government agencies are entrusted with vast amounts of constituent data that they are responsible for protecting. Virtru can help keep that information secure.
/Secure%20Email%20Encryption%20Widget.webp)
/Secure%20Email%20Encryption%20Widget.webp)


“By enabling full compliance for our law enforcement agency, Virtru gave us a path toward a complete cloud migration.”
Susan Lyon
Google Cloud Team Manager, State of Maryland
Authorized by FedRAMP and GovRAMP for Trusted Data Security
Virtru makes it easy for any organization to protect and share sensitive data — from small municipalities to the federal government, across the defense industrial base, and beyond.



Every SLG Agency Needs Secure Data Sharing

Health and Human Services
Protect health reports, communications with clinics, and personal health information (PHI) protected by HIPAA.
/Updated%20Solutions%20Pages/law-enforcement-office-01.webp)
Law Enforcement and Fire Departments
Encrypt case reports, communications, investigation details, and protected criminal justice information in accordance with Criminal Justice Information Services (CJIS) requirements.

Children and Family Services
Protect personal and financial data for children and families in your jurisdiction, while ensuring regulatory compliance. Secure communications with citizens while ensuring they can easily access vital, time-sensitive information.

Social Security
Ensure data can be efficiently shared with citizens, the Social Security Administration, and the Internal Revenue Service in accordance with HIPAA and other regulations.

Court Systems
Secure sensitive and confidential legal communications, logistics and scheduling, as well as physical security data.

Human Resources
Collect onboarding paperwork and employee benefit selections, as well as recruiting and compensation information, with the confidence that it’s protected with powerful encryption.
Virtru State & Local Government Procurement Contracts
Virtru's state and local government contracting vehicles are managed in partnership with Carahsoft. You can view the full list on Carahsoft.com.
Google Products and Services - OMNIA Partners, Public Sector
4400006642
May 01, 2016- Oct 31, 2023
Local Government Email and Data Protection Resources
Get expert insights on how to address your data protection challenges.
Ready to take the next step?
Book a Demo
Become a Partner
Contact us to learn more about our partnership opportunities.
Become a Compliance Champion
Contact us to learn more about our partnership opportunities.