Cloud-Native, Data-Centric Security for Telecom and Software Companies
As your business grows, the amount of data you must protect grows with it. Virtru provides data protection solutions that keep up with your rapid pace of innovation.


"We were instantly more assured of the security and safety of our practices once we implemented Virtru, and are able to communicate securely without second thought."
Katie M.
Virtru Customer in IT Services Industry
Enterprise Data Security for Zero Trust
From global telecom companies to software startups, Virtru provides data-centric security that scales as your organization grows.




Protect Intellectual Property and Strengthen Compliance
Your data is your competitive advantage: That includes intellectual property, strategic plans, and sensitive information like customer data. Virtru helps you safeguard that valuable information.

Shield Data from Cloud Providers
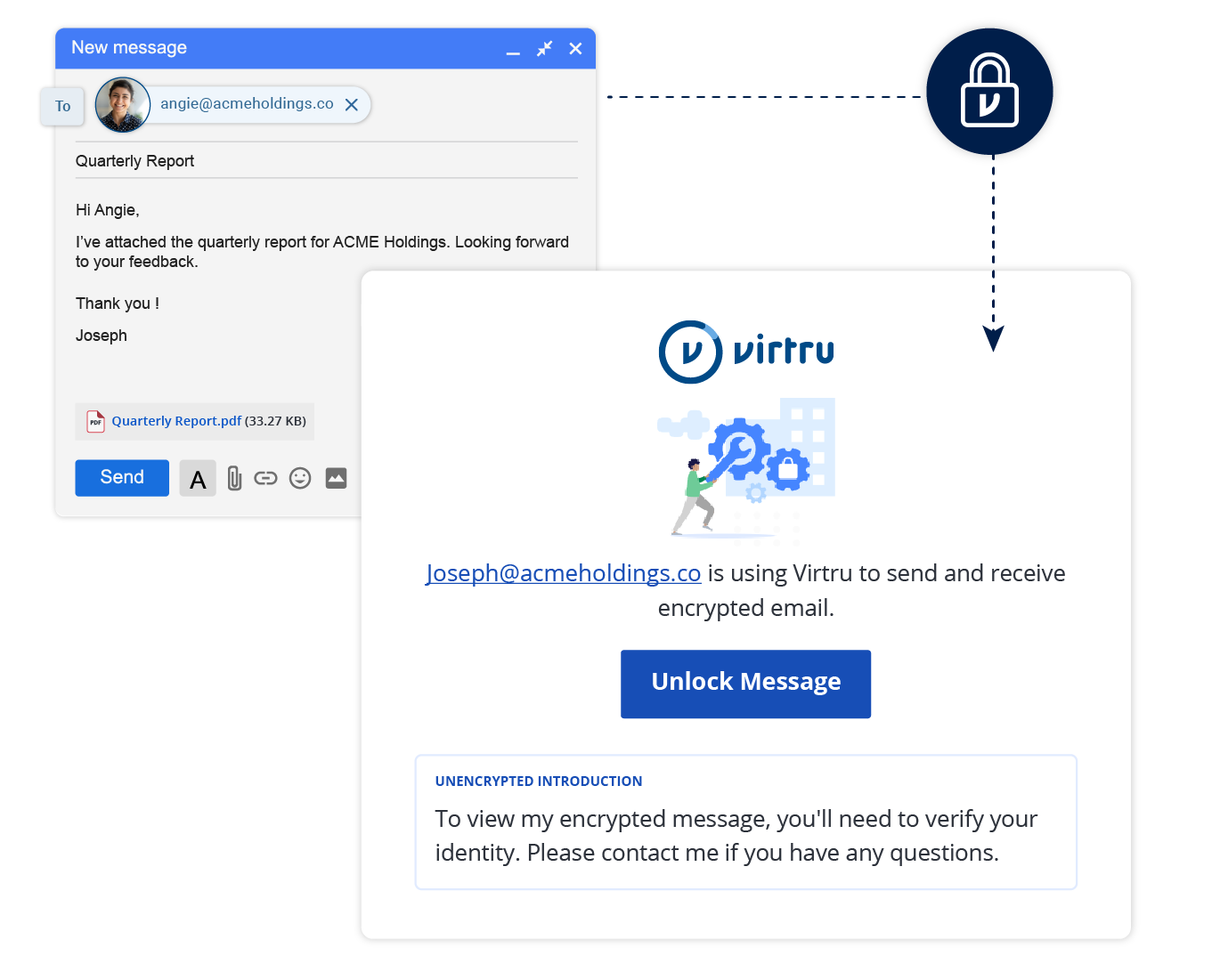
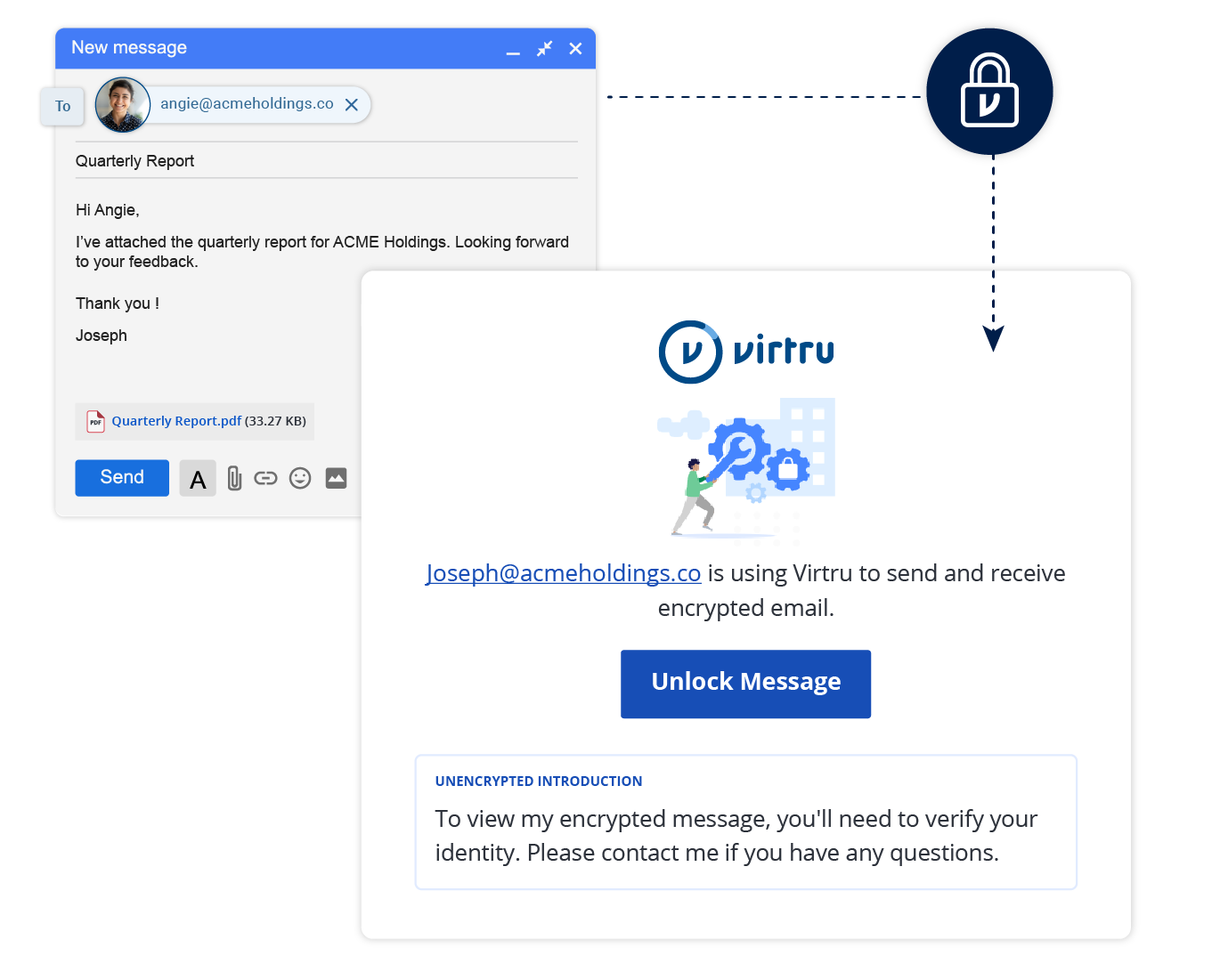
Encrypt emails and files containing sensitive, private data including PHI, PII, CUI, or intellectual property. With the Virtru Private Keystore, you can also host your own encryption keys to keep data private (even from your cloud provider) and prevent government surveillance.

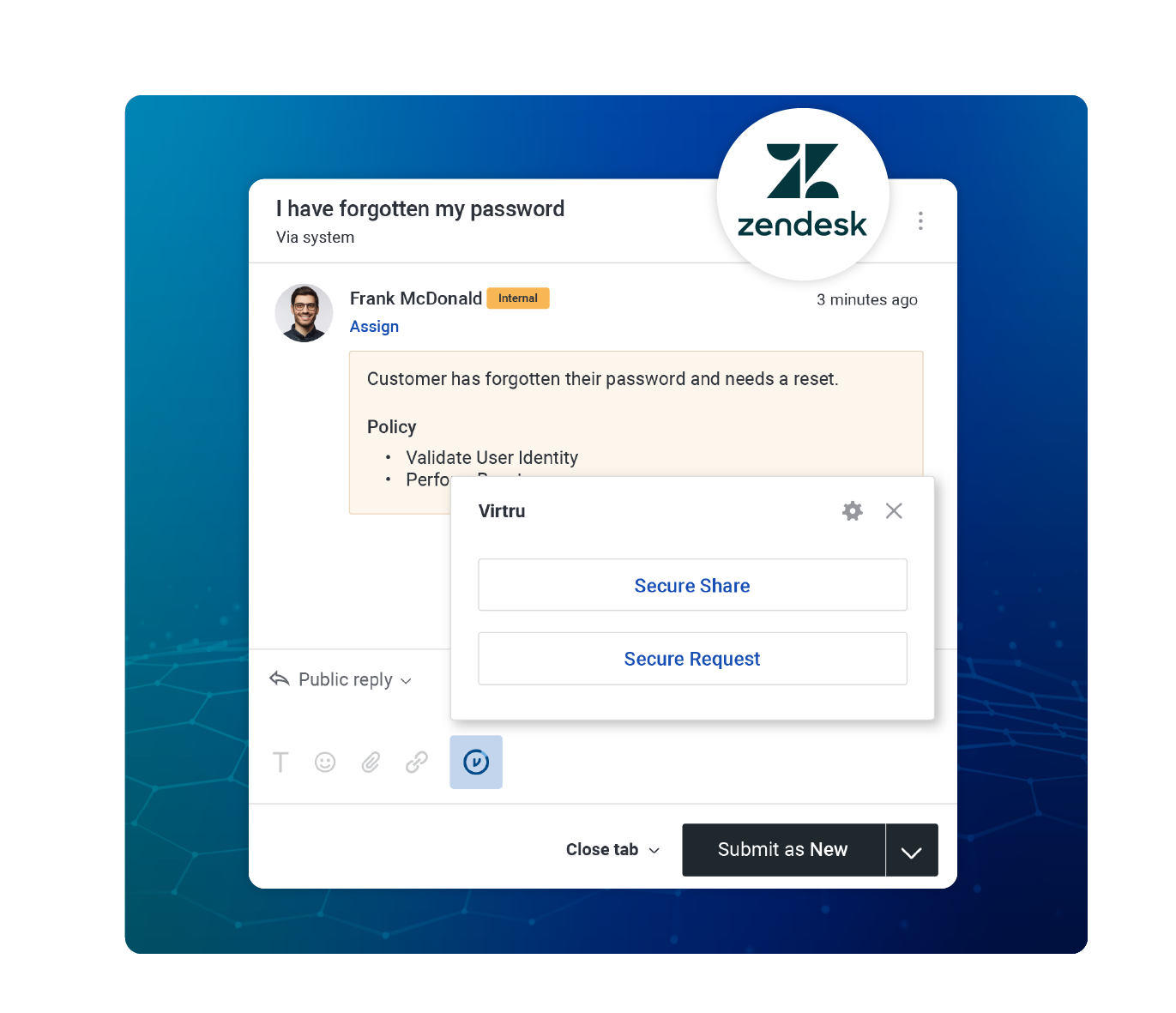
Power Innovation with Secure Data Sharing
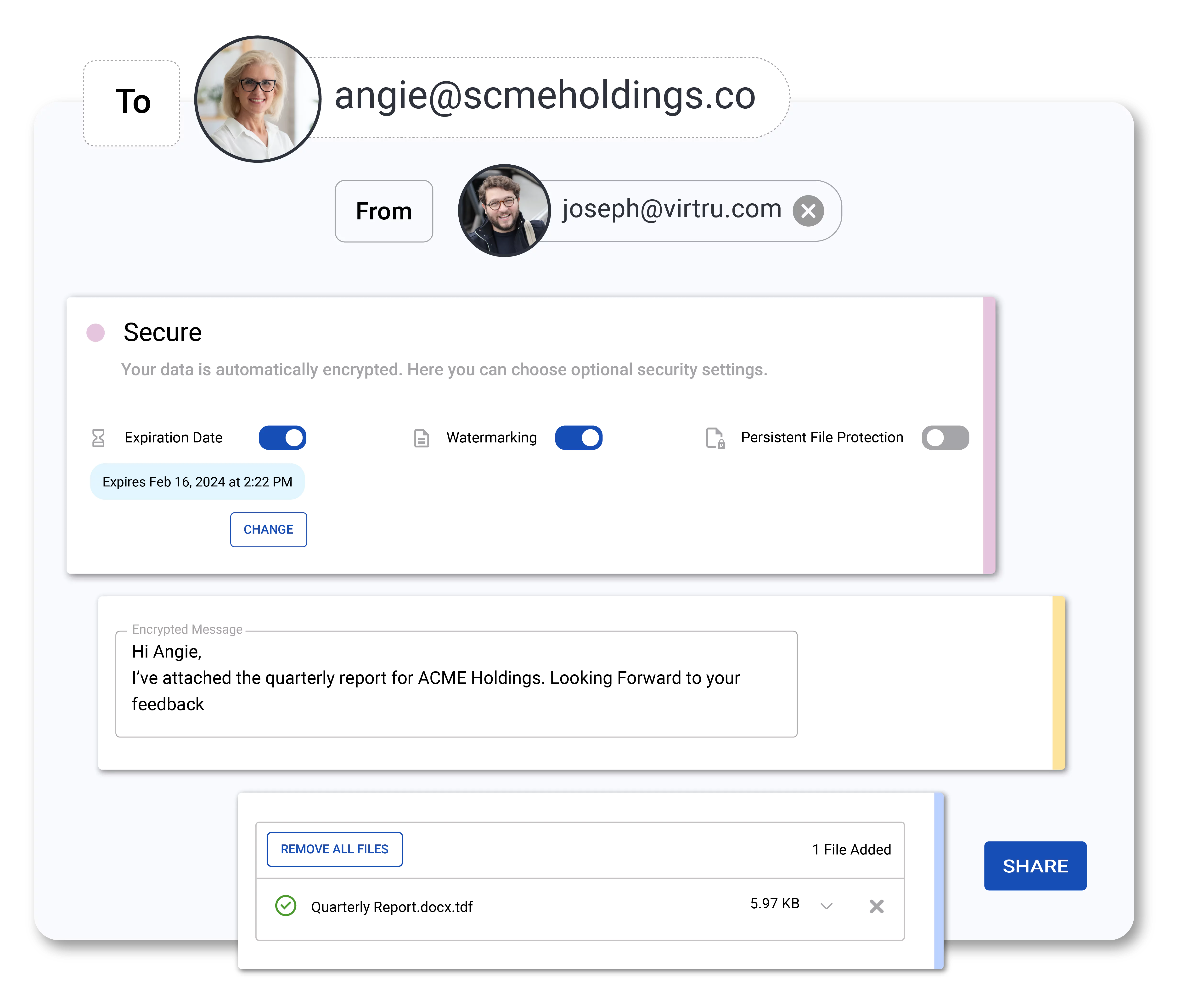
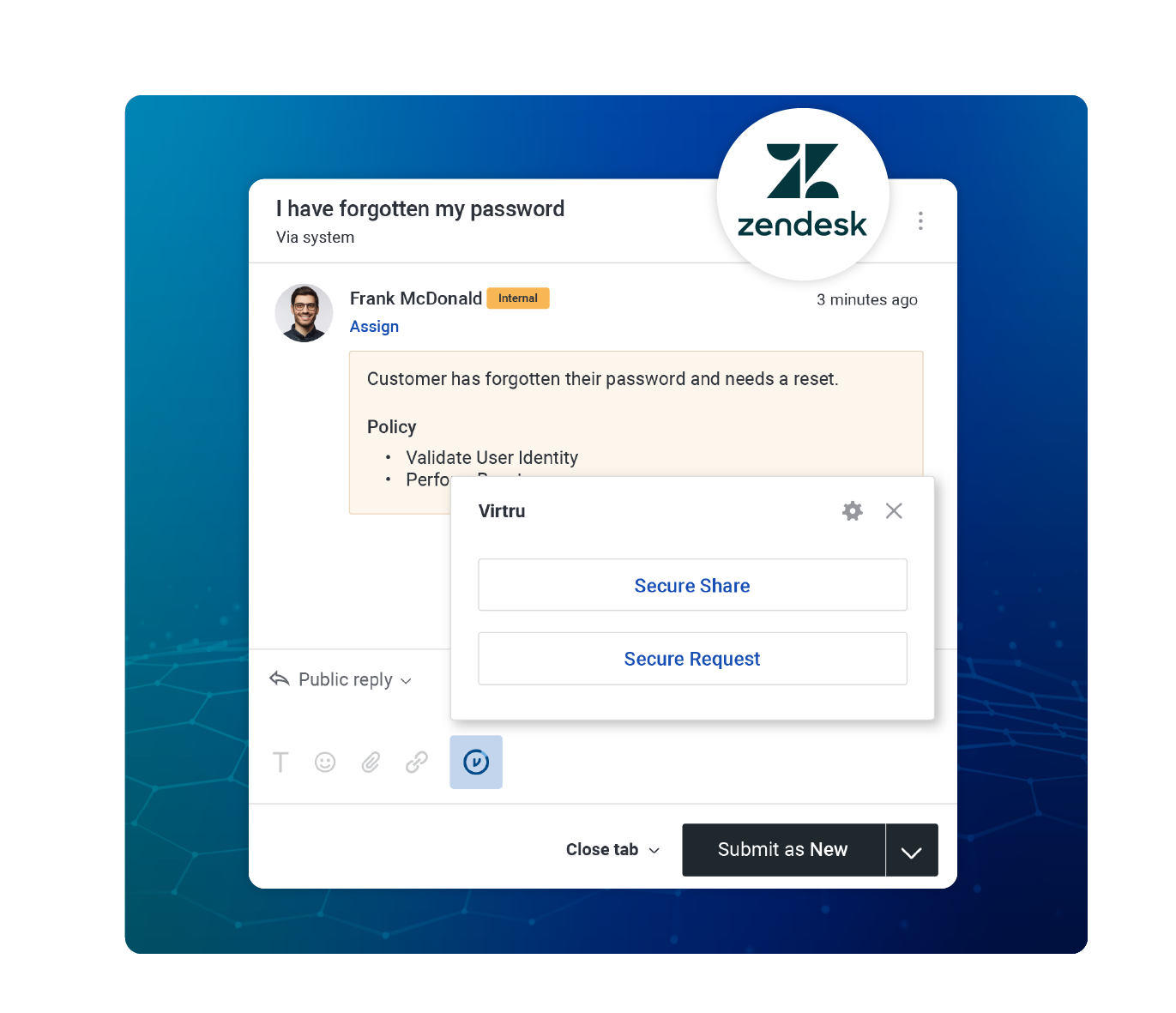
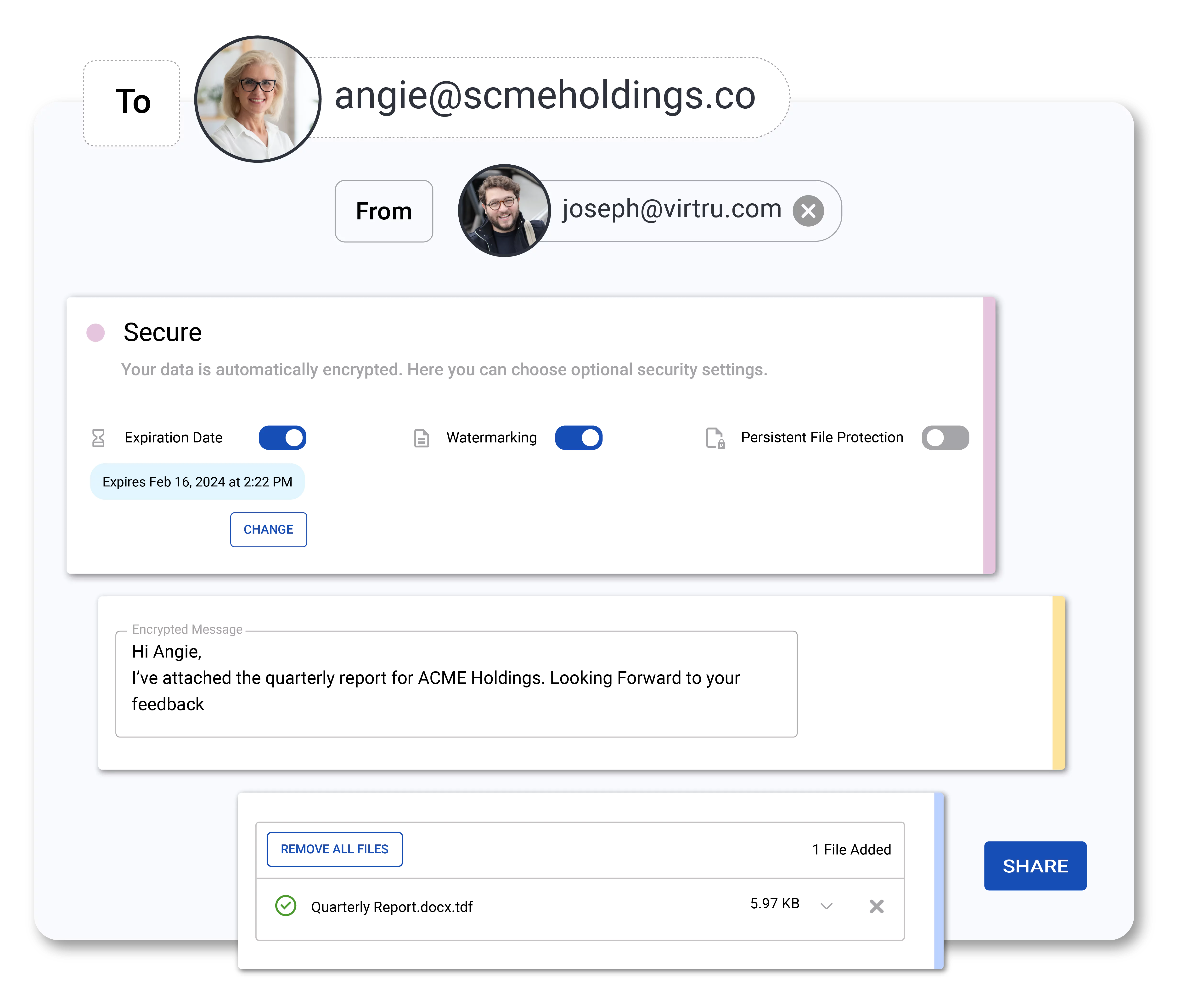
Virtru makes it easy to collaborate securely with external partners, applying attribute-based access controls to ensure data is only accessed by the right people, at the right time.

Centrally Manage and Monitor Data Access
Control proprietary data wherever it’s shared with instant access revocation, expiration, disable forwarding, and document watermarking.
Audit who has accessed your data, when, where, and for how long. Integrate with your SIEM to flag unusual activity.
Resources
See how Virtru can empower your organization to take control of your cloud data.
Ready to take the next step?
6,100 CUSTOMERS TRUST VIRTRU FOR DATA SECURITY AND PRIVACY PROTECTION.


Book a Demo
Become a Partner
Contact us to learn more about our partnership opportunities.
Become a Compliance Champion
Contact us to learn more about our partnership opportunities.

.jpg)
