The World's Biggest Cyber Vulnerability Isn't What You Think: It's Voluntary


Damages from cybercrime are expected to cost the global economy $7 trillion this year, and $10.5 trillion annually by 2025. Thus, it's no surprise that the entire cybersecurity industry is obsessed with finding and fixing vulnerabilities.
But what exactly is a vulnerability? According to NIST 800-16, a vulnerability is a flaw or weakness that may allow harm to occur to an IT system or activity.
Digging a bit deeper, it is important to understand the difference between known, unknown, and voluntary vulnerabilities.
Known Vulnerabilities
Known vulnerabilities are software or system defects that have been identified by security researchers and publicly disclosed in the Common Vulnerabilities and Exposures (CVE) list. Vulns listed in the CVE are then subsequently published in the National Vulnerability Database (NVD) which is operated by NIST and sponsored by the Department of Homeland Security. The NVD does three main things:
- Assigns a score to each vuln indicating the relative severity on a scale of 0 to 10.
- Indicates the type of vuln, for example software, hardware, other.
- Provides additional information relevant to the vuln's functionality and exploitability, for example how exactly an attack might be carried out by cyber criminals.
In aggregate, information in the NVD is used by organizations around the world to see and understand the inventory of known vulns and to prioritize which ones should be patched first to keep data and IT systems safe.
Unknown Vulnerabilities
Unknown vulnerabilities exist in every part of the digital landscape and simply have not been discovered yet by security researchers. Therefore, they have not been assigned a CVE, and not been reported to the NVD. Simply stated, they exist in the wild and pose great risk, but no one knows about them, possibly not even malicious actors.
When unknown vulnerabilities are first discovered, it's what the cyber industry calls a zero-day event. A zero-day is a vulnerability in a system or device that has been recently discovered and publicly disclosed for the very first time. When zero-days are publicly disclosed, as Log4j was in December 2021, it literally becomes a frantic race between good guys trying to patch the newly discovered vulnerability, and bad guys trying to exploit it. As a result, zero-day vulns pose higher risk for one simple reason: Bad guys often win the race, moving faster to exploit than good guys move to patch.
Given the stakes, white hat and black hat interests both invest huge amounts of time and money meticulously hunting and pecking across the digital landscape to become the first to discover cyber defects never before known to the world. When black hats are first to discover a vuln, they keep it to themselves and begin to exploit it for profit. When white hats researchers are first to find a zero-day, they quietly engage in a confidential process to inform the appropriate vendor about the vulnerability—which is precisely what happened recently when researchers from WithSecure reported an Office 365 encryption vulnerability to Microsoft. Once vendors are made aware of a zero-day vulnerability, they will typically work to develop a patch or remediation plan. And, once a patch is available, the vendor will then file a CVE and issue a press release so that customers can move to remediate the vuln, hopefully faster than criminals move to exploit it.
Voluntary Vulnerabilities
Over the past 50-plus years, the world’s attack surface has evolved from servers and desktop computers to a vast collection of connected systems and workflows where massive amounts of sensitive data is constantly flowing in and out of every business on the planet.
In this context let's stop for a moment and think about just how much data is leaving our possession every single day, and why?
While a significant amount of data is exfiltrated, against our wishes, by bad actors exploiting known and unknown vulnerabilities—the vast majority is departing our possession intentionally. Simply stated, huge amounts of sensitive data leave our control on a daily basis when we voluntarily share it with third parties via a wide variety of collaboration workflows like email, file sharing, and SaaS applications.
In this case, the exploit path is voluntary collaboration. While it doesn't have a CVE and it's not in the NVD, it's the meanest fox living in our cyber henhouses. Indeed, with 330 billion emails sent worldwide per day, it's easily the single greatest reason businesses lose possession of sensitive data.
Keeping Things Real
Data is the world's most valuable resource, and sharing it with others via collaboration workflows is how companies deliver service, exchange ideas, and create shareholder value. Simply stated, nothing will stand in the way of our insatiable appetite to share data and get business done.
As information systems become more dispersed, mobile, and dynamic; it's critical that IT leaders and risk managers think beyond conventional network-centric security measures. Going forward, the most innovative organizations will automatically classify and tag data so they can enforce downstream policies and embrace data-centric security at scale. Through data centric security management, IT teams will be able to protect sensitive data regardless of where it resides, or who it has been shared with. Furthermore, business end users will be able to share data easily while simultaneously satisfying security and regulatory requirements, including CMMC, ITAR, HIPAA, and FTC Safeguards.
Sound impossible? It's not.
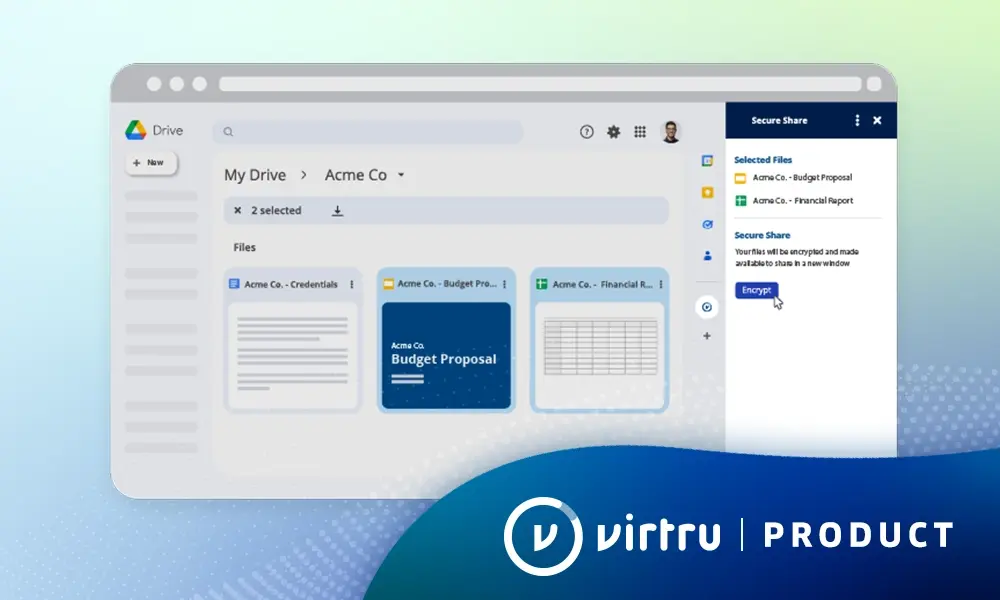
With Virtru and Trusted Data Format (TDF), it's surprisingly easy, and more affordable than you might think, to embrace data centric security controls for collaboration workflows including email, files, and SaaS service clouds like Zendesk and Salesforce. Want to see how easy it can be? Get in touch with the Virtru team to see a demo.

Matt Howard
A proven executive and entrepreneur with over 25 years experience developing high-growth software companies, Matt serves as Virtu’s CMO and leads all aspects of the company’s go-to-market motion within the data protection and Zero Trust security ecosystems.
View more posts by Matt HowardSee Virtru In Action
Sign Up for the Virtru Newsletter