Configure data loss prevention (DLP) policies to automatically enforce persistent protection and control to maintain data privacy and compliance.
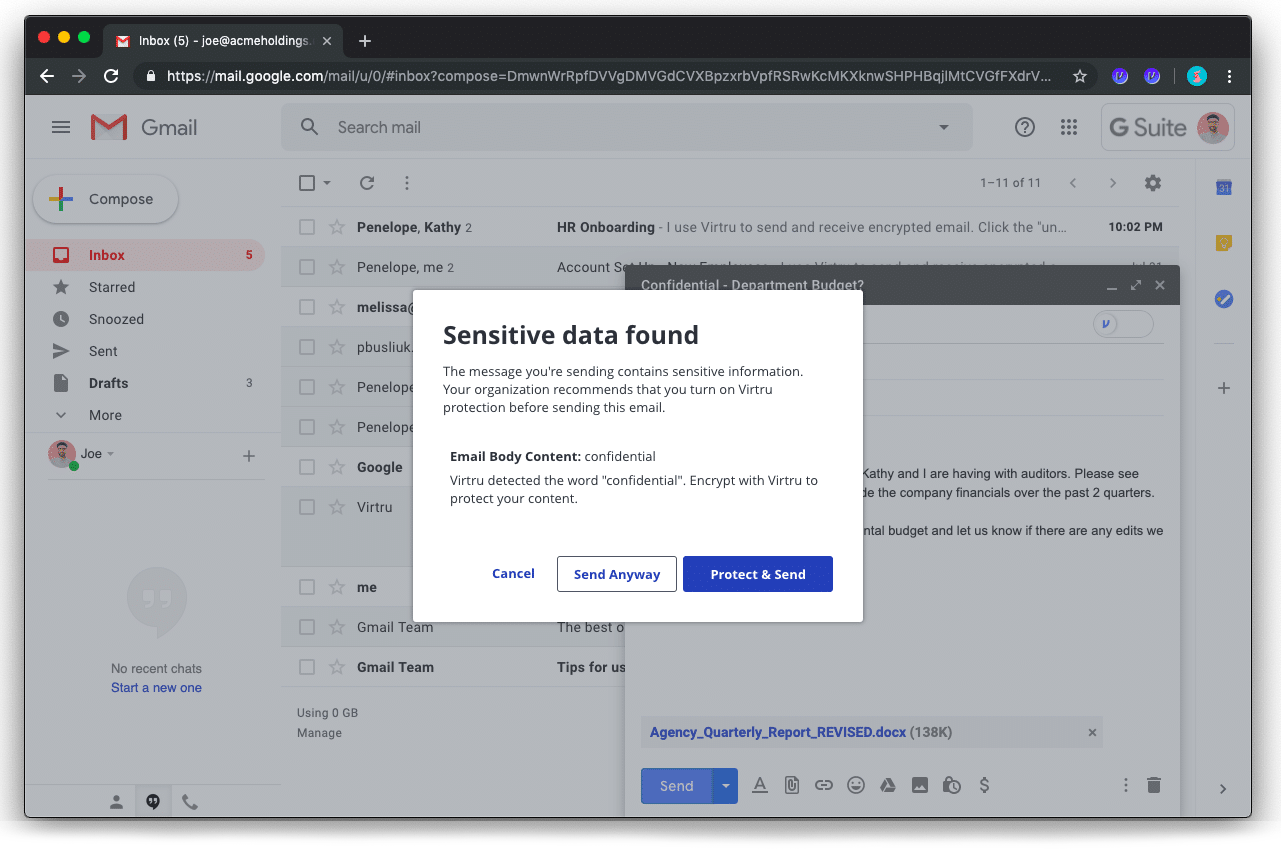
Enhance security awareness across the organization with DLP rules that warn users to protect sensitive data to complement on-demand protections. Choose from preconfigured DLP rules that scan emails for sensitive keywords, text patterns and other common indicators to protect your sensitive data before it even leaves your device.
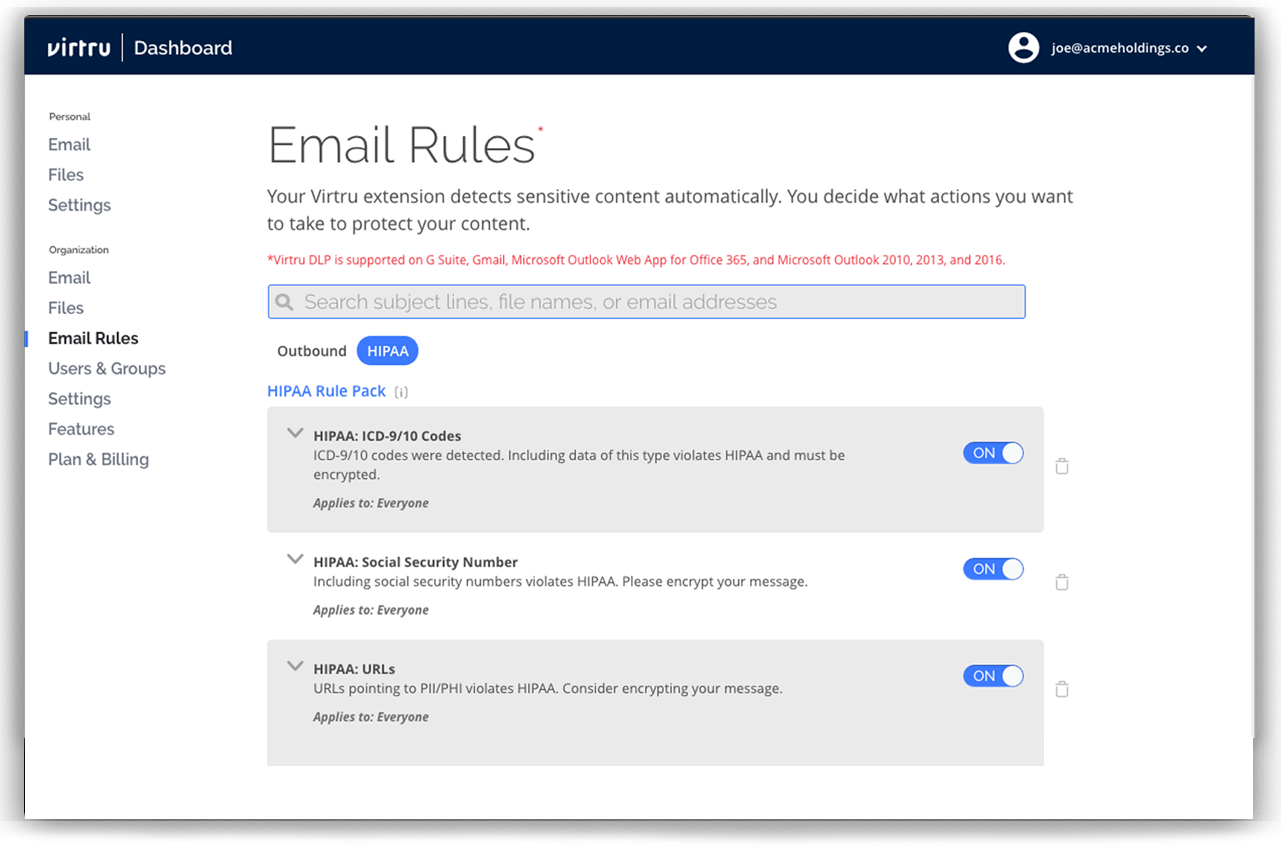
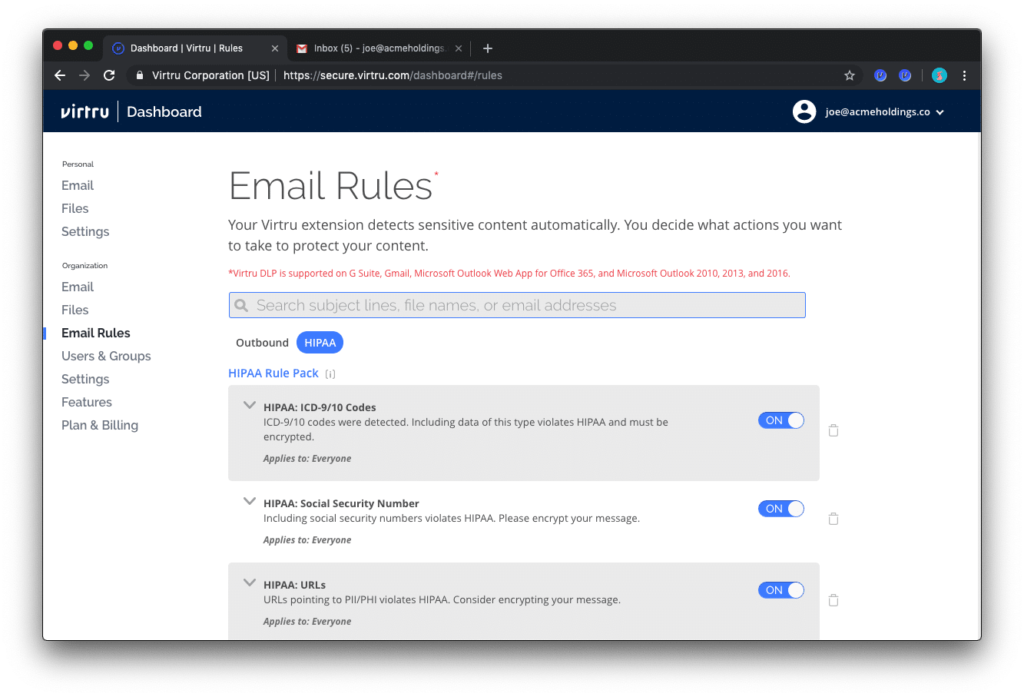
Easily configure DLP policies to scan for PHI, then apply encryption and access control policies before they leave your domain. Implement the Virtru HIPAA Compliance Rule Pack, or leverage Virtru's integration with Nightfall AI, to automatically detect and protect common types of PHI including SSNs, ICD-9/10 codes, National Provider Identifier (NPI) and more.
.png)
Configure powerful DLP policies to match your organization’s data security and compliance requirements. By scanning multiple email fields—subject line, body and attachments—Virtru can enforce automatic protection with custom logic. For OUs or individuals that frequently send sensitive data, custom DLP policies can further reduce the risk of a data loss or breach.
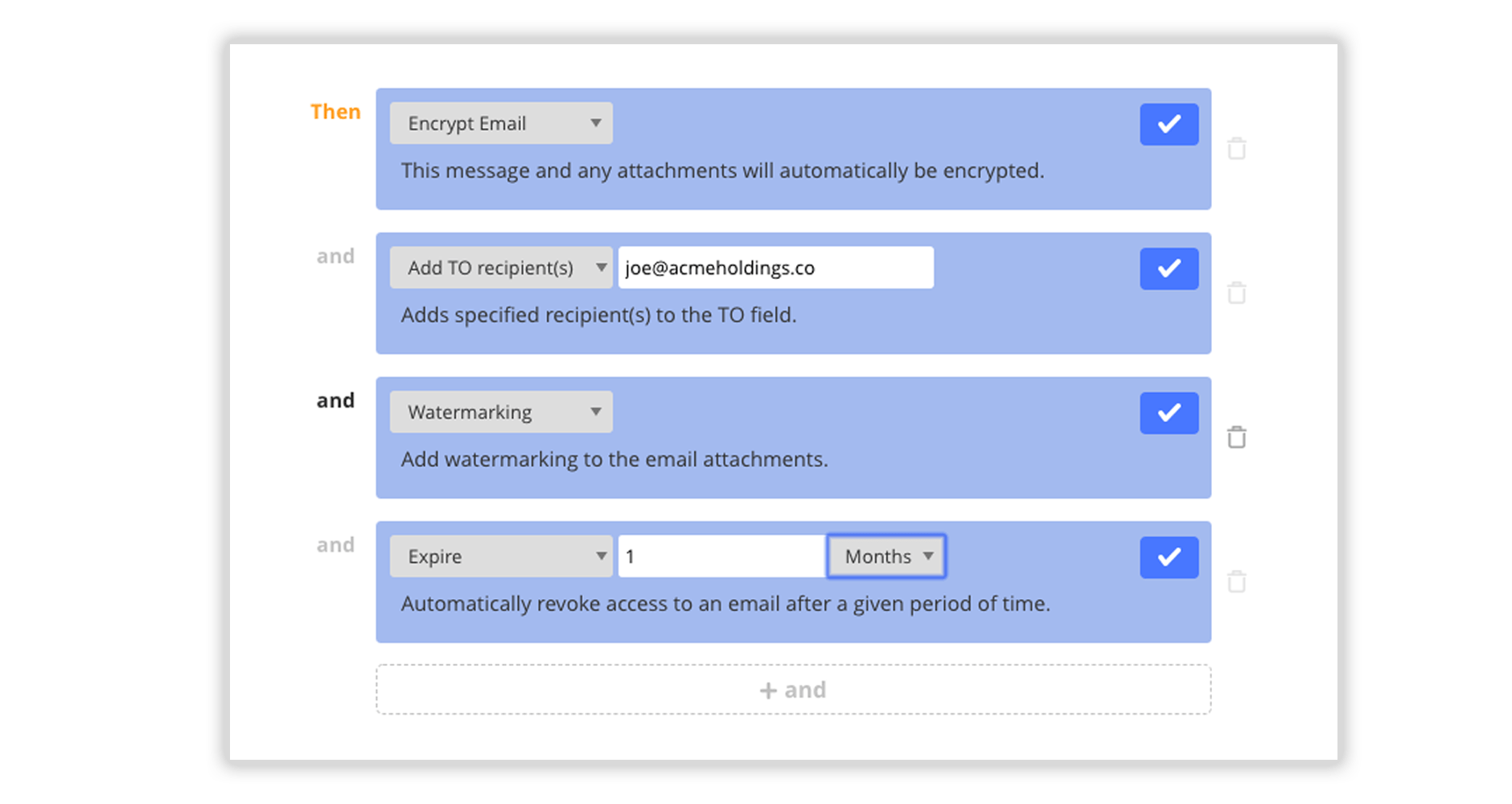
After sensitive content is detected, configure rules to enforce protection—such as object-level encryption, access expiration, disable forwarding, attachment watermarking or even stripping attachments to mitigate data leak risks. Granular control gives admins the ability to monitor user activity and add additional recipients for total visibility into sensitive sharing workflows.
“We like the control features. For example, being able to revoke a message,
and have an audit trail, really sets Virtru apart.”
— Dave Steck, VP of IT Infrastructure, Schnucks Market

Get expert insights on how to address your data protection challenges.
Contact us to learn more about our partnership opportunities.