The Hidden Limitations of Native Encryption and TLS

When you buy a bike lock, you expect it to work every time. But what if it only worked 8 out of 10 times? Would you still feel good about leaving your bike on a crowded city street?
The same logic applies to the data of your customers protected by the Federal Trade Commission’s Safeguards Rule. When it comes to achieving compliance with the Gramm-Leach-Bliley Act’s amendment to the FTC Safeguards Rule, small businesses may think they're covered by the native encryption solutions offered by their email service providers — but is that level of encryption sufficient to protect highly sensitive financial data?
While native encryption is certainly a step in the right direction, more is needed for meeting 100% of the encryption provision. In this blog post, we'll uncover the hidden limitations of native encryption solutions and highlight why an additional layer of security makes good sense for financial institutions — and gives CISOs greater peace of mind.
Why Shouldn’t You Rely on TLS Encryption Found in Native Solutions?
When we talk about encryption, one of the most prominent limitations that many organizations face relates to the dependency on both sender and recipient ends of communication. This is particularly true with Transport Layer Security (TLS), the standard encryption protocol used by both Google and Microsoft.
In an ideal world, TLS acts as a secure tunnel through which your emails can safely travel from sender to recipient, safeguarding the contents from any potential prying eyes. However, the actual implementation of TLS is not quite as seamless.
Transport Layer Security (TLS) Is a 2-Way Street
In the case of Google's Gmail and Microsoft's Outlook, the usage of TLS encryption is dependent on both the sender's and the recipient's email service providers. If either of these service providers does not support TLS, the email communication will not be encrypted. This dependency significantly limits the effectiveness of TLS, as it means the security of your communications is partly out of your control.
Google is transparent about this limitation - and displays the rate at which emails are encrypted natively with TLS: outbound, in the 80th percentile, and inbound in the 90th.
According to Google: “By default, Gmail always tries to connect with TLS when sending email. Secure TLS connections require that both the sender and recipient use TLS. If the receiving server doesn't use TLS, Gmail will deliver email, but the connection isn't encrypted with TLS.”
Microsoft, on the other hand, employs an 'opportunistic TLS' approach in Outlook. This means it will attempt to use TLS if the recipient's server supports it, but if it doesn't, the email will be sent without encryption. Like with Google, this means that there's a chance your sensitive data could be sent without the appropriate safeguards for encryption, presenting a security risk.
This dependence on both ends of communication not only introduces potential vulnerabilities but also raises challenges for achieving full compliance with the FTC's Final Rule. The rule specifically mandates encryption of customer information both in transit over external networks and at rest.
Native Encryption Doesn't Get You to 100%
While native security features provide a strong first line of defense for email security, they're not comprehensive. Using native encryption as the sole method of securing sensitive data might lead to organizations only being partially compliant with the FTC Safeguards Rule.
The FTC Safeguards Rule doesn't settle for near-enough solutions, it requires full commitment. This means selecting tools that can go the distance in their specific domains, delivering a comprehensive 100% encryption rate to support compliance, rather than stretching a single tool thin across diverse rule requirements, which will likely fall short.
Don't Settle for 80%. Virtru's Commitment to Securing Data Across its Full Lifecycle
While the FTC Safeguards rule doesn't require "end-to-end encryption," you can rest assured that you'll be covered as this goes above and beyond what's needed. That's where Virtru comes into the picture. We've designed our technology to simplify the complex world of data security for you. Here's a sneak peek into our core features.
Encryption at Rest and In Transit - A Guarantee
With Virtru, each email message and file attachment is encrypted at the data object level, with granular access controls. This data-centric method ensures that only the designated recipients can access the content. Virtru serves as an added layer of protection that ensures your data remains secure, whether in transit or at rest.
A Safety Net for Human Error
Pairing Virtru's client-side encryption tools with server-side encryption ensures you have a multi-layered approach to protecting data leaks or breaches. If an employee forgets to encrypt a message containing sensitive information, you can use Virtru's Data Protection Gateway to ensure that message is encrypted before it leaves your organization.
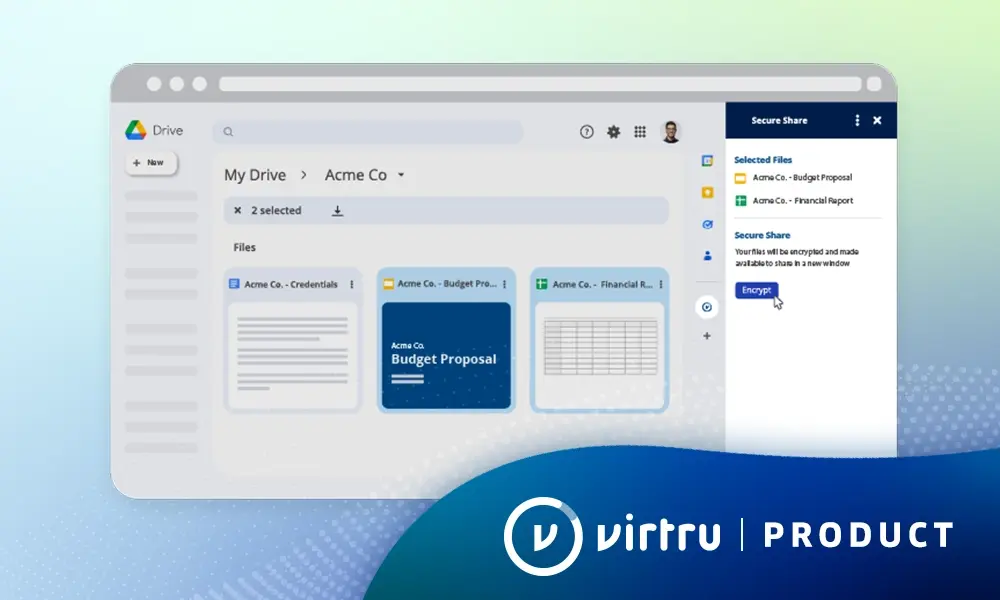
Full Data Control at Your Fingertips
Maintain control of your data even after it’s left your perimeter. Revoke access, limit sharing, and more, no matter where your data is located. With features like granular visibility and watermarking, you can always keep track of your data.
Make Encryption Easy with Virtru
Virtru makes encryption and decryption easy for you. That's why we ensure easy integration directly into your email clients, whether it's Google Workspace or Microsoft Outlook. And the best part? No portals, no new logins, no new password: A quick self-verification with your existing credentials grants you access to your secure data, which means you won't be jumping through hoops to protect your information. It's seamlessly connected with the apps and workflows you already use every day.
Read: Kunes Auto Group Uses Virtru to Encrypt Data For FTC Safeguards
Come for the compliance, stay for the elevated cybersecurity posture. Dealerships, educational institutions, and more choose Virtru to meet the encryption provision of the FTC Safeguards Rule.
Talk to our team today to find out what guaranteed encryption at rest and in transit looks like in your organization.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter