Supply Chain Attacks and the Need for Access Controls

With the ever-growing reliance on a digitized economy and business processes, enterprises must assume their data will be exposed to untrusted environments. Whether it is third-party software or hardware or throughout the enterprise supply chain ecosystem, even ‘trusted’ networks quickly become a risk in the absence of data access controls. These risks are only accentuated with the growth of distributed workforces as well as the geopolitical tensions that reflect the clash between free and secure data and the diffusion of surveillance states with an insatiable thirst for data.
To truly protect your data—wherever it goes—data protection strategies must start at the data-object itself. Data flows through untrusted environments, yet most data protection strategies focus on self-assessment of enterprise systems and fail to account for the range of third-party data risks across an extended physical and digital supply chain. In a recent survey, Virtru found most organizations have hundreds of cloud-based applications, with disparate data controls across each. At the same time, complex supply chains consist of upwards of thousands of partners, while most companies lack visibility of their data across these relationships, including who can access personal or proprietary information.
The Expansion of Untrusted Environments
An enterprise’s expanded supply chain ecosystem— not just its first-tier suppliers but their suppliers’ suppliers and so on—is seldom considered in data protection frameworks. But as professors Daniel Pellathy and Ted Stank contend, data protection safeguards must extend into the supply chain as well. As they note, “A substantial investment in securing customer data at one company can easily be undermined by a supplier with weak financial incentives for safeguards.”
Unfortunately, as ongoing disruptions have made abundantly clear, most organizations lack full visibility across their extended supply chain. As organizations rethink their supply chain strategies, gaining visibility across the entire ecosystem is essential to better grasp and prepare for a full-range of risks. Part of this reset must also account for the myriad ways data gets shared and accessed throughout their extended supply chain ecosystem.
Data sharing and digitization have introduced significant efficiencies for collaboration and specialization across supply chains, but they also introduce new risks and expand the attack surface. While the Target breach is arguably the most prominent example of supply chain attacks, as attackers gained access through an HVAC partner, they are far from alone. Supply chain attacks increased 78% in 2019, while 60% of data breaches were linked to third-party vendors.
A recent FDIC report summarizes the findings of the Office of the Inspector General’s assessment regarding supply chain risks. The majority of these risks refer to untrusted software or hardware, including:
- Installation of malicious hardware or software providing backdoor access and system control.
- Installation of counterfeit hardware or software that impacts trust.
- Reliance on a malicious or unqualified service provider with access to systems and data.
- Unintentional hardware or software vulnerabilities.
As the FDIC report notes, often the vulnerabilities are unintentional. Misconfigured cloud services introduce a range of vulnerabilities, resulting in hundreds of breaches and exposing tens of billions of records. Considering the number of cloud-based applications on which companies are reliant, these unintentional data exposures are likely to persist.
In some cases, however, targeted attacks intentionally leverage the digital supply chain to access sensitive data. For instance, in the CCleaner attack, legitimate software updates were injected with malware to allow attackers to gain a foothold. The malicious software was downloaded over two million times, with a second stage of the attack installed 40 times to target 11 separate companies.
Untrusted technologies are yet another growing concern, with emerging regulations limiting the installation of some hardware and software, especially when contracting with the U.S. government. Section 889, part B, of the Federal Acquisition Regulation (FAR) rule in the National Defense Authorization Act (NDAA) went into effect on August 13th, 2020. This amended rule prohibits certain surveillance and technology equipment or services from being part of any system in a Federal contract. Put simply, under Section 889, the technologies of five companies and their affiliates cannot be present for companies seeking Federal contracts.
Section 889 is part of a broader global trend, where democracies from the United Kingdom to Japan and Australia are increasingly prohibiting certain surveillance and communications technology. This risk of exposure through untrusted technologies will only grow as malicious actors innovate in their methods to gain access to personal and proprietary data.
Data-Level Access Controls
While it’s a common adage in cybersecurity that the perimeter is dead, rarely does supply chain risk factor into enterprise data protection strategies. This must change. As the number of cloud-based applications within enterprise networks grows into the hundreds, and the digital and physical supply chains of global companies reach into the thousands, they remain a prime target by malicious actors seeking unauthorized data access.
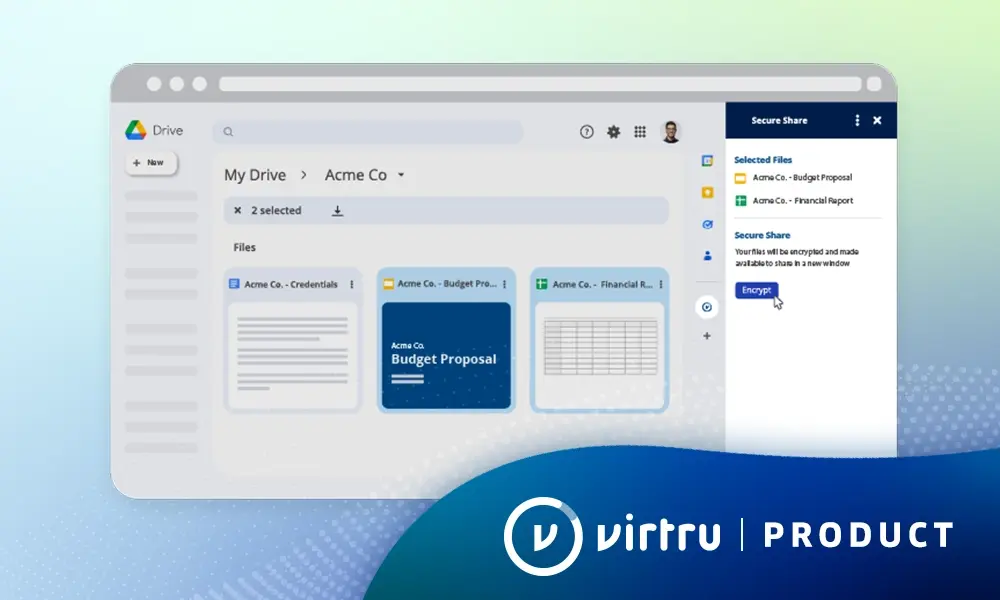
Maintaining access controls and visibility of enterprise data at the object-level can help enterprises thrive in a digital economy while protecting their sensitive data, even in untrusted environments. Importantly, as concerns grow over untrusted environments, new regulatory requirements are emerging to impact compliance risk. The upcoming Cybersecurity Maturity Model Certification (CMMC) goes into effect this fall and requires a range of best practices, including data access controls across remote and internal systems. While many of these regulations are aimed at federal contractors, ensuring object-level data protection is imperative across a range of industries as untrusted environments and unintentional data exposure continue to have significant business impact.
To learn how Virtru can help you protect sensitive data shared via email and files throughout your supply chain and prepare for CMMC, download a free copy of our latest whitepaper or get in touch with us today.
See Virtru In Action
Sign Up for the Virtru Newsletter