Take Back Control: Digital Workplace Data Management Best Practices

It’s predicted that 83% of enterprise workloads will be in the cloud by 2020. 41% of these workloads are predicted to run on public cloud platforms like Amazon Web Services, Google Cloud Platform and Microsoft Azure. An additional 20% are predicted to be private-cloud-based, followed by another 22% running on hybrid cloud platforms.
More small-and mid-sized organizations are taking a cloud-first approach to their business operations, leveraging productivity tools like Google G Suite, Amazon Web Services and Microsoft Office 365. After all, the cloud comes with benefits such as scalability and increased innovation and effectiveness. Plus, it can help organizations reduce costs, increase collaboration, and give employees the ability to share and be more productive anywhere they work.
However, there is too often a divide between keeping data secure and making sure employees can access and share data efficiently. Full-scale cloud adoption presents significant challenges for many organizations, especially those bound by the constraints of legacy infrastructure, those in highly-regulated industries, or those that are simply risk-averse. But it’s not impossible.
Best Practices for Data Control in the Cloud
Here are five best practices that will give you control over your data—and ensure it stays private and secure—at every stage of your cloud journey.
Classify Your Data.
Data discovery is an important first step because one, it helps you identify all the places your data is located in your environment, and two, it helps you determine what’s too sensitive to migrate based on classification rules. Breaking down your data into four categories of sensitivity—Classified Data, Restricted Data, Private Data, and Public Data—will make your cloud migration easier to execute.
Assign Data Policies.
Once your data is classified, determine what kind of control and protection each tier should receive. For example, consider policies like access control, watermarking and expiration dates, based on the set level of sensitivity. And only share these controls with authorized users.
Establish Attribute-Based Authentication and Control.
This will give you the ability to track everything that happens to your data in the cloud and immediately mitigate risk. Security-focused tools like auditability and automatic notifications will allow you to identify anomalies in your environment so you can take action fast, like identifying outliers and cutting off access.
Conduct Third-Party Audits.
All it takes is one weak link in your supply chain to expose your data. Some industries, like healthcare—which accounts for one-third of all potentially compromised records—are particularly susceptible to value-chain attacks. You can reduce this risk by regularly conducting penetration testing and SOC audits. And don’t forget to review and audit your vendors’ access and control policies.
Pick the Right Cloud Platform.
Working with the right cloud partner is a critical part of your digital transformation. The key is to find a partner that makes it easy to get started, and more importantly, one that is transparent about their data policies. You should have a clear understanding of what they do with their data, who they share it with and who has access. Avoid “black box” vendors at all costs.
What to Look For in Data-Centric Security Software
Being skeptical of managing your data in the cloud is okay. Locking yourself into working with a single vendor or, worse, blindly trusting one, will put your data at risk. And when it comes to really protecting your data, securing the communication layer in your environment isn’t enough. You have to protect the data itself to ensure persistent and perpetual control. Seek out a data protection solution that provides:
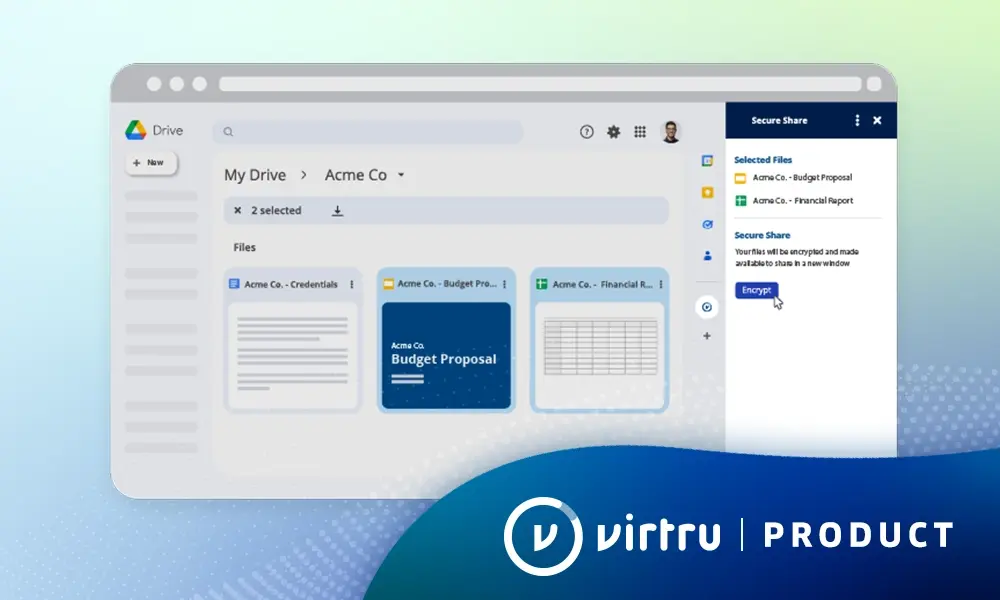
- Data-Centric Encryption: Protects the data itself, wherever it is created or shared. This also gives you the power to add or remove access to your encryption keys (versus the data itself).
- Control of Encryption Keys: ensures that your cloud service provider never has access to the encryption keys used to protect your most sensitive data.
- Granular Audit: Gives you visibility into everything that is happening with your data in the cloud—who is accessing it, how often, and from where. It also allows you to monitor and adapt access controls and privileges throughout the data lifecycle.
- Access Controls: Provide the ability to perform advanced actions like scheduled email revocation, watermarking, and the prevention of email forwarding. In addition, you can do things like revoke email attachments but not the email content.
Whether you’ve already begun your digital transformation or are just beginning to think about it, the cloud is loaded with benefits that are aimed to increase business performance, scalability, and innovation. We'd love to discuss how you can confidently and securely move your data to the cloud. Contact our team for a demo of Virtru's data-centric encryption software today.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter