How to Adapt your Email Security Model for the Cloud

Organizations today face a handful of challenges—message interception and manipulation, lack of identity verification, phishing and malware—in dealing with current email security structures. Finding a solution to these challenges is important, but finding the right solution is critical. In our recent article, we discussed end-to-end encryption as the way forward in email security, as well as the four pillars of a secure email strategy: confidentiality and integrity, identity verification, usability and having a data-centric approach.
Protect, Control and Audit
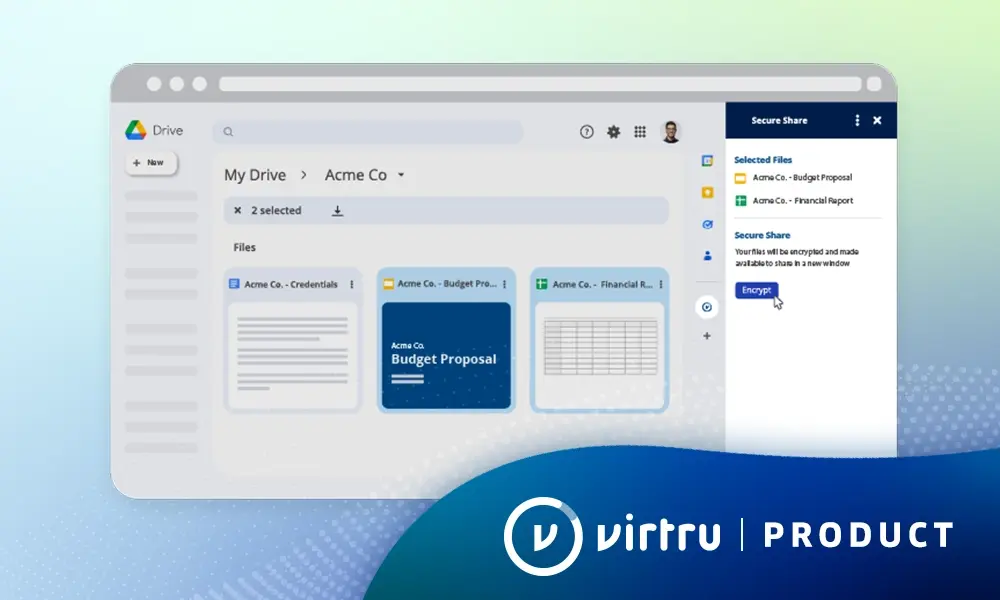
Understanding what a data-centric approach looks like is critical in developing an email security model that extends to the cloud. Traditional approaches are tech-focused in that if an attacker attacks, the technology responds. Virtru, however, takes a data-centric approach allowing you to protect what is actually valuable—the data.
A data-centric approach to email security should:
- Protect: Ensure that data is safe at all times with end-to-end encryption.
- Control: Further protect data with features such as access revocation, controlled forwarding, and watermarking.
- Audit: Give you a clear view of all interactions with the data in order to maintain compliance.
When you think about what a data-centric approach to email security might mean to your organization and how you are set up—whether its on-prem, hybrid, or on the cloud—consider the lifecycle of your data. Where is it created? By whom? Where is it going? Who’s going to be interacting with it?
The answers to these questions have different implications for your organization depending on how you’re deploying your solution. So if there’s user-generated or client-side generated sensitive data that needs protection and control, having a seamless, integrated solution on that side is critical. Usability—one of the pillars of a secure email strategy—requires extending the user-experience into what the user knows, ultimately resulting in a higher adoption rate, critical to deployment success.
But, there are other workloads that generate sensitive data requiring protection, control, and ability to audit. If you’re in the cloud or hybrid model, you have different systems generating this type of content. Regardless of whether it’s an application or a script, it’s a non-human storage of that data so taking a client-side integrated approach is not enough. Instead, think more holistically—be sure you have surface area for inspection and enforcement where that data is created, ensuring that you are aware of what that data is and the certain sensitivities of it so you can apply the appropriate controls and have a comprehensive implementation of that data-centric solution.
Key Considerations for Email Security in the Cloud Era
Email is often the primary means of communication for organizations, but cloud-based messaging platforms are gaining traction in the modern workplace. Therefore your email security strategy should also provide protection, control and audit for cloud-generated data. Consider this:
- Adopt a Zero Trust model—essentially “never trust, always verify”—for data that is of the highest risk. Moving to the cloud, or a hybrid model, requires an extension of your trust model. So by limiting third party access to unencrypted content, you can defer some of the liability and maintain a lower risk profile.
- Ensure you can fully embrace the benefits of collaboration, afforded by being on the cloud, by maintaining full control of your sensitive data. Taking advantage of a cloud collaboration platform opens up your organization to the promise of increased productivity and allows you to remain competitive in a fast-moving marketplace. But, it also fosters an increase in data mobility and virality. Mitigate this risk with a solution that gives you clear visibility as to where your sensitive data is and who is accessing it.
- Reduce the administrative burden with appropriate key management. Make sure you have an appropriate cost of ownership that does not nullify the benefits of being in a cloud environment. E-management technologies available today help to address this concern.
- Seek out a solution that provides extensibility beyond just email. While email may be your primary means of communication, as the workplace evolves to meet the needs of the digital age, your security solution must be able to keep up to provide persistent protection across email and other applications.
Email security is quickly becoming a vital requirement and expectation for normal business activities. Traditional models are useful but can be challenging to implement and maintain in today’s digital workplace. The key metric of success here is that everything is “business as usual”, with little to no extra thought or work required. Instead, a security solution should enhance the experience and enable users. So, bearing in mind these four key considerations, seek out a security solution that gives you mobility and agility now just now, but into the future.
Speak to a Virtru security expert and learn how you can incorporate data-centric protection into your email security model.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter