Closing the Cloud Compliance Gap

Cloud adoption is on the rise with 83% of enterprise workloads predicted to be in the cloud by 2020. Organizations across all industries are eager to take advantage of the promises of greater efficiency, flexibility and collaboration offered by the cloud. Even though all major cloud service providers (CSPs)—AWS, Google Cloud and Azure—invest heavily in security, it’s critical that companies understand where the cloud falls short. After all, the benefits of the cloud mean nothing if it puts your organization at risk, especially when it comes to compliance.
Due to the complexity of the regulatory landscape, it can be difficult to align your data security strategy and compliance program. But to put it simply, compliance in the cloud centers around the location of personal data and who has access to it. So, as more and more organizations move to the cloud, it could expose a compliance gap as regulations tighten, especially for organizations handling personal data. Here’s what you can do to take matters into your own hands and close the gap.
Understanding Your Role in Compliance
It’s easy to feel like you’re giving up control of your data when you effectively hand it over to your CSP. And the truth is, it is hard to control where data goes in the cloud since many cloud services are designed around a non-localized model to facilitate access from anywhere.
Fortunately, the reality is that data sharing and data privacy and security are not mutually exclusive. But, your CSP’s native security features are likely not up to par for maintaining compliance. Cloud providers are largely focused on protecting the infrastructure that keeps their services running. How your employees use and share data though, is up to the organization itself to monitor and enforce.
Not acknowledging the shared responsibility, or an over-reliance on your CSP’s security features, can place your organization at great risk of not meeting compliance standards. More often than not, that means enterprises must take advantage of the latest technology to further protect data. At a minimum, your data protection solution should protect sensitive data at rest and in transit, as well as prevent third-parties from accessing it.
Key Considerations for Compliance
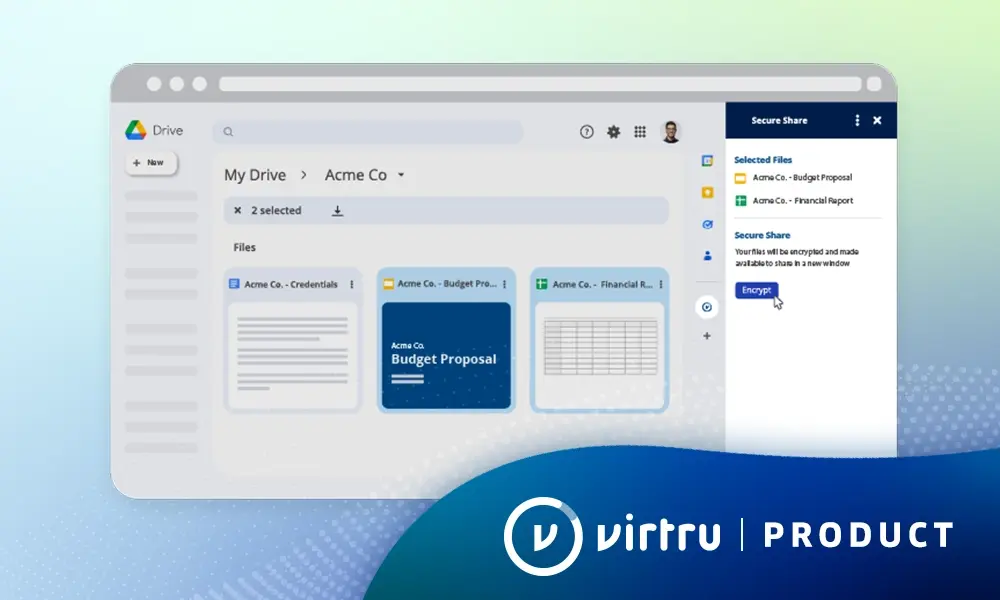
As we have discussed before, the data protection solution that your organization chooses must fit within an organization’s workflow or else you risk employees not adopting it. Virtru’s client-side encryption is extremely user-friendly, which can make widespread cloud adoption and compliance a reality, even for heavily regulated industries—such as manufacturing, healthcare or government.
If you’re faced with extensive governance mandates or certain regulatory needs that require more control and visibility features than your CSP offers, the right technology can complete your cloud data management solution. Virtru’s encryption and access management solutions facilitate compliance in four ways:
1. Strong, easy-to-use client-side encryption for email and files
This ensures that your sensitive data is protected before it even leaves your device, both at-rest and in-transit.
2. Effective key management solutions that offer complete control of customer encryption keys.
Virtru’s split knowledge architecture ensures that your CSP never has access to the encryption keys used to protect your most sensitive data.
3. Powerful access control tools that allow organizations to maintain control of their data.
Safeguard data, regardless of where the emails and files are created, stored or shared. By setting policies on encryption keys, data owners decide who can access content, and for how long.
4. Audit features to facilitate insight and reporting on when and where email and files have been accessed or shared
Administrators can audit access to protected content in real time and can easily search archived encrypted content to meet regulatory e-discovery requirements.
Compliance is a Responsibility
While organizations are able to rely on technology solutions, such as Virtru, for additional data protection to enable compliance, they cannot outsource responsibility for compliance. After all, penalties for non-compliance fall entirely on the organization, not the CSP.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter