The 5 Worst HIPAA Business Associate Agreement Mistakes


Many healthcare providers treat a HIPAA business associate agreement like a mere formality. They draft a HIPAA compliance checklist to carefully verify access control, training and other factors, then leave it to legal to send off BAAs to partners as part of the contract paperwork.
But you’re responsible for safeguarding Protected Health Information (PHI), even when it’s off-site, and the HIPAA business associate agreement is the only tool that can do this. Your organization needs to carefully examine BAAs for HIPAA violations, just like you would with any other security and compliance control. Here are some mistakes to look for:
1. Failing to take HIPAA Business Associate Agreements Seriously
Although HIPAA business associate agreements have always been a requirement, enforcement actions used to be quite rare. Until recently, the OCR focused almost exclusively on breaches by covered entities. That all changed in 2016.
The OCR brought 6 enforcement actions from February 3rd to April 21st, the largest of which imposed a $3.9 million penalty. Two of those enforcements imposed large penalties for lack of HIPAA business associate agreements, including a $1.55 million penalty imposed on North Memorial Health Care.
These announcements were timed to occur as the Office of Civil Rights (OCR) Phase 2 HIPAA Audits were beginning. While phase 1 was a small, pilot program focusing on covered entities exclusively, phase 2 is a multi-stage audit that looks at business associates as well as providers, and includes site audits.
The OCR has made it clear that they’re willing to subject organizations to additional scrutiny or take enforcement actions if they see evidence of serious violations. And HIPAA business associate agreement auditing is likely to get even more aggressive in the future, as the OCR establishes protocols for regular HIPAA compliance audits. Organizations have two choices: prioritizing HIPAA business associate agreements or waiting to become OCR case studies.
2. Not Covering All of Your HIPAA Business Associates
Most healthcare providers understand that a healthcare clearinghouse is a business associate, but not all of them get how broad the term is. Originally, covered entities — such as labs providing testing — weren’t subject to BAAs, since they’re responsible for their own HIPAA compliance standards, but the Omnibus rule changed that. Now, pretty much anyone who processes, stores, transmits or accesses your PHI and is not part of your organization is a business associate, including other covered entities. If a healthcare provider isn’t employed by you but does work for you, they’re subject to the HIPAA business associate agreement.
Since the rule change, IT providers who furnish infrastructure used for ePHI are also considered associates, even if their employees don’t usually read, store or process it. That can include companies providing:
- Cloud hosting
- Backup storage
- Apps to process PHI
- Tech support
- Data destruction
- Electronic security tools
Organizations that are considered “mere conduits” are an exception, since they pass PHI but don’t have access to it. This exception is pretty narrow, however — it covers postal couriers, ISPs and not much else. HIPAA also provides exceptions for maintenance staff if their exposure to PHI is incidental. In other words, a janitor wouldn’t normally require a BAA, but your sysadmin probably would. When in doubt, sign a HIPAA business associate agreement.
3. Leaving Important information Out of HIPAA Business Associate Agreements
In a BAA, the partner organization pledges to uphold a range of HIPAA compliance requirements, including Technical, Administrative and Physical Safeguards.
However, it’s not enough just to define your partner’s responsibility to protect PHI; you also need to spell out how they’re expected to do it. A HIPAA business associate agreement should address how the partner is authorized to use PHI, who can access it and under what circumstances, and what protections the associate will use with subcontractors.
The agreement should also specify how the partner will enforce compliance. Training workers, supervision, internal auditing and other appropriate measures need to be included. Write the breach notification clause with details, such as how and under what circumstances the associate should contact you, and how quickly they’re expected to do it.
4. Failing to Verify Business Associate Compliance
A HIPAA business associate agreement doesn’t exempt you from due diligence. Your organization should conduct a risk assessment and either review a potential partner’s internal audit, or conduct one yourself before signing a contract. You should also request a copy of their internal HIPAA policies and regularly review logs of their employee training, security incidents and periodic audits.
Your goal should be to go above and beyond minimum HIPAA business associate agreement requirements. Not only will this minimize risks by holding your partner(s) accountable for maintaining excellent security — it will also ensure you’re not subject to an enforcement action, should your associate suffer a breach.
5. Failing to Back Your Business Associate Agreement with Good Technology
The HITECH ACT requires healthcare providers to use Electronic Health Records for a range of tasks, including supporting clinical decisions, recording and transmitting prescriptions and lab orders, and giving patients access to their records. Even independent of HITECH, doctors routinely use electronic means to communicate with business associates and other clinics, process electronic billing and exchange PHI.
Healthcare organizations need to use tools to encrypt PHI in order to securely send it to partners, and mandate the use of those tools in their HIPAA business associate agreements. But the safety of your data isn’t just dependent on good encryption technology and training — it also depends on convenience. If a tool is too, difficult, slow or unreliable to use, workers will take shortcuts to get the job done, using insecure alternatives such as unencrypted email.
Unfortunately, most healthcare organizations fail by adopting the wrong tech: healthcare portals. Portals require users to learn a new interface, create a login ID and often, install software. Healthcare providers must configure the portal, and update it regularly to prevent new security vulnerabilities from compromising PHI.
Perhaps most importantly, they aren’t mutually compatible. The lab that tests your blood work, the specialist clinic you refer patients to, and your medical billing provider could each have a different portal, requiring your staff to retain multiple accounts. This can lead to multiple, incomplete or inaccurate copies of patient records. It also makes it more difficult to compile and effectively utilize all of a patient’s healthcare data, potentially harming quality of care.
Portals can also undermine HIPAA business associate agreements by leading your associates or your own staff to take shortcuts — sending unsecured emails, keeping unencrypted copies of files on the desktop for easy access, or taking other unacceptable HIPAA cloud compliance risks.
Strengthen HIPAA Business Associate Agreement Requirements with Virtru
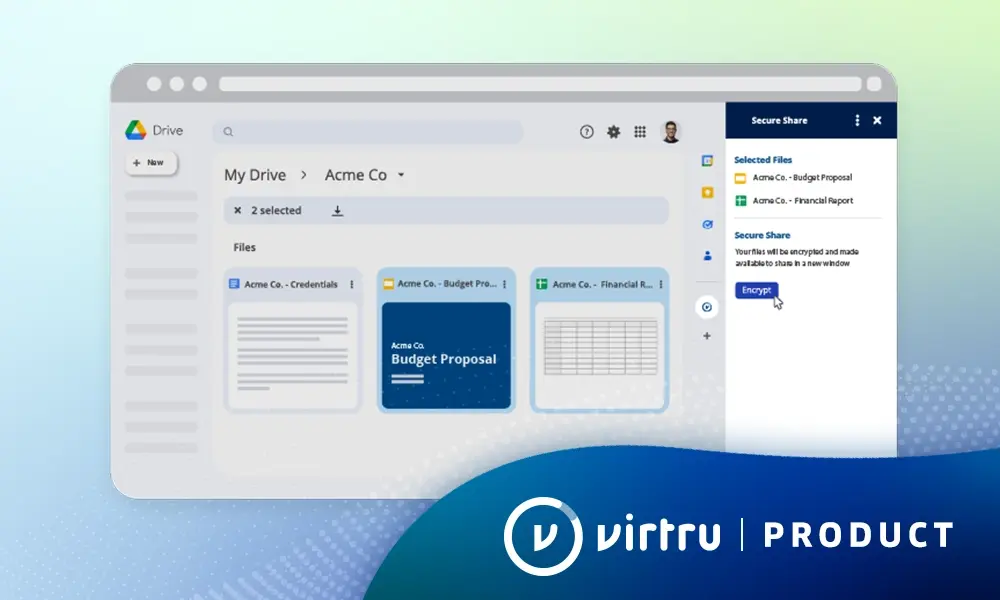
Virtru provides a better solution. The Virtru browser plugin adds email encryption to your existing account, allowing workers and associates to securely email PHI with one click. That means no patching, complex interfaces or additional logins. Even recipients who haven’t installed Virtru can receive encrypted email and respond securely.
Virtru also facilitates HIPAA business associate agreement requirements like breach notification and mitigation. If a user accidentally sends PHI to the wrong address, they can revoke it, then check Virtru read receipts to see if it has been read. If they revoke it in time, they’re immune from the breach notification requirements.
Virtru’s HIPAA Compliance Rule Pack provides even more protection, preventing workers from accidentally violating the HIPAA business associate agreement in the first place. It automatically detects sensitive data such as Social Security numbers and ICD-9/ICD-10 codes before the email is sent. It can then take a range of actions, including warning the user, encrypting the email, removing attachments or cc’ing a supervisor. See Virtru’s HIPAA Compliance Rule Pack in action here:
HIPAA compliance requires the right partners under the right agreements. As a HIPAA compliant email and file encryption provider, we have one goal: making secure communication easy. Virtru layers military-grade encryption on top of the email and file solutions you already use, creating a seamless end-user experience. That convenience ensures your staff and your HIPAA business associates will never have to take unnecessary risks sending and receiving PHI.
Ready to learn more? Schedule a personal demo.

Rob McDonald
As Virtru's SVP of Strategy and Field CPO, Rob advocates safeguarding data across emerging applications and sharing workflows. With deep expertise as a healthcare CIO and security consultant, he helps organizations mitigate technical and human risk. Rob has a Computer Science degree and is a lifelong technology and security student.
View more posts by Rob McDonaldSee Virtru In Action
Sign Up for the Virtru Newsletter