5 Data Risk Management Tips for Businesses

Organizations are producing data at record speed: It’s estimated that by 2025, worldwide data will grow to 175 zettabytes. Maintaining the right level of visibility and control over this data should be a top priority for all organizations across the globe. But doing so is often a major challenge. Why?
Widespread cloud usage and fast-growing data volumes, combined with hundreds of scratch-built applications and the use of various consumer devices, leave IT and security decision-makers without a clear or accurate view of who inside their organization has access to their data. This is a major problem when it comes to ensuring the security and privacy of your data.
How is your data at risk?
In today’s digital age, organizations are continuously sharing data in order to collaborate and drive the business forward. Whether you’re working in an office environment or remotely, it’s easy to share files with a few mouse clicks. But, it’s just as easy for sensitive information to end up in the wrong hands without the proper precautions in place.
Sensitive data includes everything from customer personally identifiable information (PII), staff files, and emails to confidential R&D plans and proprietary information. Put simply, data is extremely valuable information that you should make every effort to protect because while sharing data can drive growth and innovation, it also comes with risks.
Internal and External Data Risks
- Internal risks stem from employees. Although it’s hard to imagine that an employee would willfully sabotage an organization, it does happen. More frequently though, internal risks are purely accidental. For example, losing a thumb drive with confidential product development plans stored on it, or forwarding an email to the wrong person by mistake.
- External risks include attacks from cybercriminals that are designed to gain access to your system. Malware, DDoS attacks, and phishing are all examples of external risks.
Types of Data Risks
Data risk is defined as exposure to loss of value or reputation caused by issues or limitations to an organization’s ability to acquire, store, transform, move, and use its data assets. So, what does data risk look like?
- Data Breaches: The type of data risk that makes headlines, data breaches involve the unintentional release of secure information.
- Unauthorized Third-Party Access: Managing who has access to data is critical. For this reason, many compliance programs are centered on preventing unauthorized access.
- Cloud-Based Applications: Organizations use, on average, 78 different cloud based apps. Each one of those apps can expose your organization to risk if, for example, they experience a breach.
- Human Error: Employees make mistakes—such as falling for a Phishing email—and without proper cybersecurity training, the risk of human error is intensified.
- Technology Challenges: Technology is constantly evolving. Once-popular hardware or software that’s not up to date or no longer useful can pose a risk to your organization.
- Lack of Data Processes: Not having a data management strategy can increase risks. Furthermore, inefficient processes can lead to bottlenecks, redundancies, silos, and improper system integration.
Your Best Protection Against Losing Your Data
Taking a proactive approach to cybersecurity is paramount to mitigating risks. Strong passwords and staff security training are steps in the right direction. But, you need higher levels of data security to protect sensitive business data. And, what if you operate in a highly-regulated industry? Extra layers of security are likely required for compliance with privacy regulations.
To improve your security posture, here are five tips and best practices:
1. Manage data effectively.
Data management is the practice of managing data as a valuable resource to unlock its potential for your organization. Managing data effectively requires having a data strategy and reliable methods to access, integrate, cleanse, govern, store and prepare data for use. As an example, a healthcare provider in another office will need access to patient records before treatment. Ensuring those files are available to the provider allows them to do their job effectively.
Another important aspect of data management is proper cleaning and disposal. Organizations should set protocols for managing data that is no longer in use or necessary to retain, both in physical and digital format. For example, be sure to remove data from old devices and outdated computers before you recycle them and always use reliable and reputable sources for recycling and destroying unwanted documents and devices.
2. Ensure data protection is compliant with current regulations.
The regulatory landscape is an alphabet soup of security and privacy compliance programs. These regulations vary by industry but all have the common goal of maintaining the security and privacy of sensitive data.
Some of the key compliance programs to know are:
- The Health Insurance Portability and Accountability Act (HIPAA)
- The Criminal Justice Information Services (CJIS)
- The General Data Protection Regulation (GDPR)
- The California Consumer Privacy Act (CCPA)
- The Family Educational Rights and Privacy Act (FERPA)
- The International Traffic in Arms Regulations (ITAR)
3. Hire someone to manage your organization’s data.
This looks different for every organization. For a large enterprise, it may be a Chief Data Officer, but for a small nonprofit it may be a Head of IT. No matter the title, this person should serve as an expert in protecting your organization’s most valuable data. Appointing an individual to be responsible for overseeing your organization’s data management will help identify vulnerabilities and reduce risk. This person should also be on the look-out for opportunities for and through data analytics, whether that’s predicting customer trends or finding new revenue-generating opportunities.
4. Invest in data-centric security.
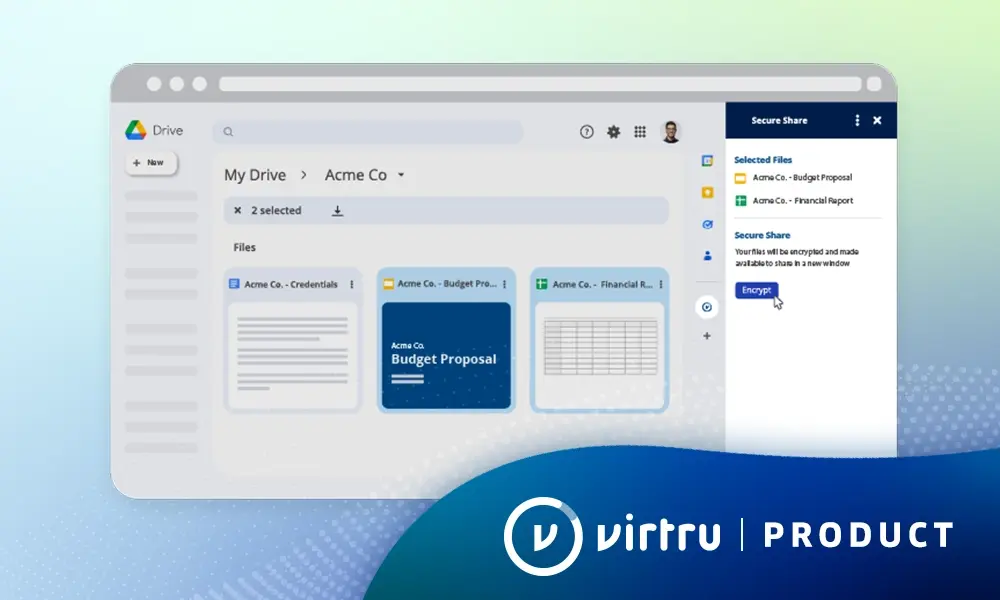
Maintaining the security of your organization’s data is a delicate balancing act. After all, your employees still need access to sensitive data in order to do their job. Gone are the days of having to choose between security and sharing of sensitive data. With a data-centric solution, you can reduce your risk while unlocking the benefits of digital workflows for your teams, partners, and other collaborators. Look for a solution that provides:
- End-to-End Encryption: Solutions that offer true end-to-end encryption ensure that only authorized users can access sensitive data to ensure privacy and regulatory compliance.
- Granular Audit: Gives you visibility into everything that is happening with your data in the cloud—who is accessing it, how often, and from where. It also allows you to monitor and adapt access controls and privileges throughout the data lifecycle.
- Access Controls: Provide the ability to perform advanced actions like scheduled email revocation, watermarking, and the prevention of email forwarding. In addition, you can do things like revoke email attachments but not the email content.
- Control of Encryption Keys: ensures that your cloud service provider never has access to the encryption keys used to protect your most sensitive data.
- Ease of Use: User awareness and adoption are core aspects of a successful security program, and when it comes to encryption, this is especially true. When introducing a new solution, employees still need to be productive and get their work done. If encryption doesn’t integrate with everyday business tools and workflows, employees will find workarounds that inhibit widespread adoption and weaken security.
5. Regularly train staff and scrutinize vendors and business partners.
By now you know that sharing data is critical for business growth. But, how can you share data securely and ensure that your vendors and partners take data security just as seriously as you do? Training employees and establishing trusted vendor relationships are key.
Provide security training to employees and promote a secure workplace
Today, more employees are working remotely than ever before, making employee security training even more important than before. To ensure business operations continue to run smoothly when teams are spread out geographically, ensure your employees care and are informed about cybersecurity. Every employee should understand his/her responsibility in protecting sensitive data.
When developing your employee security training program, a few considerations might include:
- New employees are vulnerable to phishing attempts. Help them learn how to recognize suspicious emails. These might come across as legitimate requests for information.
- Never use unsecured networks or give out confidential data.
- Avoid public wifi on work devices. Only use legitimate virtual private networks (VPNs) when traveling.
- Limit your employees’ scope to sites outside of their daily tasks to reduce risks. Restrict data permissions to keep data safe.
- Have strong passwords and encrypt all data. Confirm third-party emails before opening them.
- Ask employees to verify that a third-party asked for their information.
- Lock workstations after inactivity or incorrect password attempts to avoid unauthorized third-party access.
A strict security policy protects everyone, including those you work with outside of the organization. At the beginning of a new vendor or partner relationship, verify what security measures they have in place to protect your data when they access it. Always conduct necessary research before allowing third-party network access. You can also include non-disclosure agreements (NDAs).
A Proactive Approach to Data Risk Management
Data, in its many forms, can uncover insights to optimize your operations and power growth opportunities, but it is hard to manage. And without the right protection and controls in place, data can be a major vulnerability.
In today’s fast-paced business landscape, it’s important to take a proactive approach to mitigating risk and identify technology solutions that can keep up with business needs so as not to slow down collaboration and innovation.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter