How to Develop a Secure Email Strategy: End-to-End Encryption

In the 2016 email hack heard ‘round the world, almost 20,000 emails were stolen from the Democratic National Committee (DNC) in the middle of the United States election cycle. The hacker was able to get into the DNC’s unencrypted inbox, find emails that revealed the DNC’s supposed bias towards one candidate in particular and then release them. Had these emails been secured with end-to-end encryption, they would have been inaccessible—and many argue that the election would have had a different outcome.
While not every email breach has implications of the 2016 incident’s magnitude, it goes without saying that organizations in today’s world have a critical need for a secure email strategy— so how do you develop the right secure email strategy? First, consider the following:
- Compliance drivers.
- Privacy requirements for your organization.
- Ease-of-use and adoption.
- Security—including message interception in transit, message manipulation and lack of identity verification.
When you think about historical approaches to email security, it starts with S/MIME, which has been an open Internet Engineering Task Force (IETF) standard since the 90s. Then came PGP and, in the early 2000s, we saw the SSL/TLS Pickup method gain momentum. While all three methods utilize public key cryptography and open standards, that is not enough to ensure your organization’s emails remain truly secure.
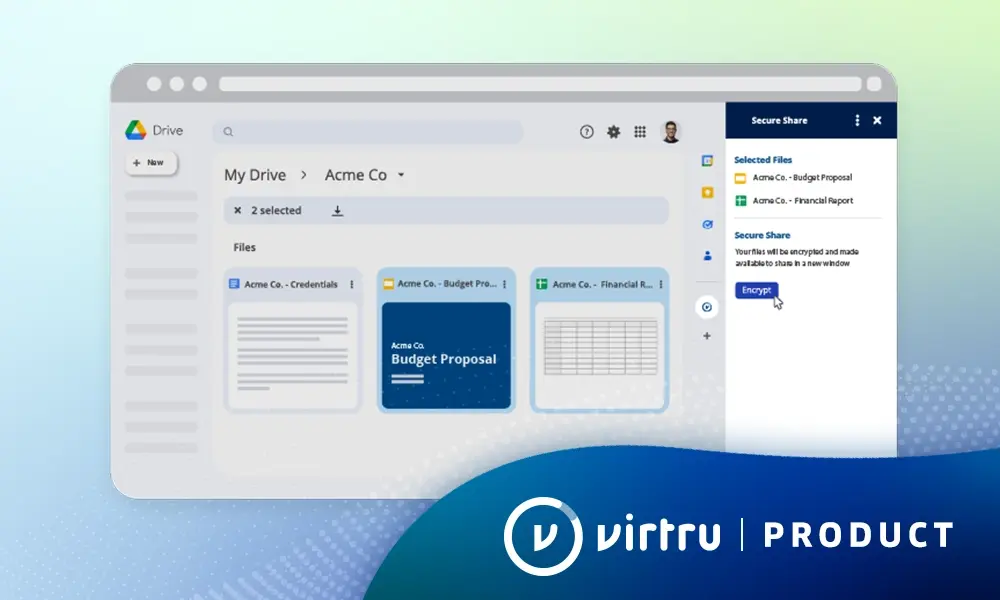
In today’s world, end-to-end encryption is leading the charge against email hacks and breaches—among both Gmail and Microsoft users—with organizations across industry lines choosing Virtru as their end-to-end encryption solution. With Virtru, organizations can use existing identities, host keys anywhere, share with anyone and search encrypted content, all without the need to install any software. To better understand the important role that end-to-end encryption has in today’s email security landscape, let’s take a closer look at where we’ve been.
Historical Approaches to Secure Email
S/MIME
Based on asymmetric cryptography, this technology allows you to digitally sign your email with a private key. The recipient then verifies you as the legitimate sender of the message with your public key—making S/MIME an effective tool against phishing attempts. However, in order to send and receive encrypted emails, both the sender and recipient need to have each other’s S/MIME certificate.
Pretty Good Privacy (PGP)
This method also uses asymmetric cryptography but the sender encrypts the email with the recipient’s public key, and the recipient then decrypts the message with his/her own private key. Because of PGP’s popularity among whistleblowers and activists, many journalists even link their public key in their Twitter profile to allow would-be sources to securely contact them.
SSL/TLS Pickup
This protocol removes the need to manage certificates or identities and instead the recipient is directed to a web portal to pick up the secure email. While this allows from some degree of auditability, traceability and control, it means that both the sender and recipient must be using the properly configured networks and browsers.
S/MIME, PGP, and SSL/TLS all require the use of public key cryptography which means you have to set up key management capability, creating a need for additional internal resources. Further, encrypted messages under these protocols are not easily searchable within your inbox—presenting a challenge when you need to do a quick search for a recent email. You may find that your encrypted messages are not viewable by default since many email clients don’t automatically decipher the encrypted emails for you. In that case, it becomes a multi-step process to pick up the message, especially if you’re using SSL/TLS pickup.
What’s more, in some cases, you may have non-native requirements—either in the form of a third-party service provider or internal man-in-the-middle server infrastructure. Both of these can be disrupted by a native mail client provider’s application update. For instance, if Google decided that they no longer want to support the S/MIME as a native protocol because of a shift in business direction, that’s going to be a problem for S/MIME Gmail users. So, while each protocol can be considered an improvement upon the former, the significant implementation and usability challenges are what lead many organizations to find a new solution: end-to-end encryption.
A Better Way Forward
When you think about secure email, one of the first questions to ask yourself is “what problem are we trying to solve?” A secure email strategy should:
- Keep messages confidential, with their integrity intact.
- Confirm the sender’s identity.
- Encourage broad user adoption.
- Take a data-centric approach.
Only one email security protocol successfully checks off all four of these requirements—end-to-end encryption—and it’s easy to use. Virtru’s end-to-end encryption ensures that all data is encrypted at all times—not just in transit and at rest—and that only the sender and recipient can view the contents of an email, providing the highest level of confidentiality and protection to your organization’s emails.
If historic email security approaches are any indication, without a high degree of usability, broad user adoption is not possible. End-to-end encryption uses existing accounts and, simply put, on-demand encryption for senders and frictionless access for recipients ensures smooth deployments and boosts the strength of your email security program.
Finally, taking a data-centric approach to email security extends beyond just protecting the data with end-to-end encryption. This holistic approach also includes control and audit. Think about it: if you’re going to apply protection with encryption, the value and risk of that data is going to change depending on where it is, where it has gone and where it has ended up. It’s important to have the ability to apply certain controls based on the lifecycle of that data and off an audit of interactions with that data that helps educate your decision.
With those three pillars—protect, control, audit—of a data-centric approach in mind, you’ll set yourself up for success in developing the right strategy for secure email.
Boost the strength of your email security program and talk to a Virtru expert today about how end-to-end encryption can work for your organization.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter