TABLE OF CONTENTS
See Virtru In Action

Sign Up for the Virtru Newsletter

Late last week it was reported that multiple European governments and media agencies who use Zimbra collaboration suite (including Zimbra Webmail) were targeted by a zero-day vulnerability, first identified in December by Volexity. Whilst the actual attack surface is unknown, up to 33,000 servers could have been affected, and Zimbra is yet to issue a patch for its product.
It’s an all-too-common occurrence – echoing the 2021 Microsoft attacks – and with the great cloud migration and the evaporation of traditional network perimeters, organizations need to re-examine their tech stack to better protect their most sensitive information from cyber threats.
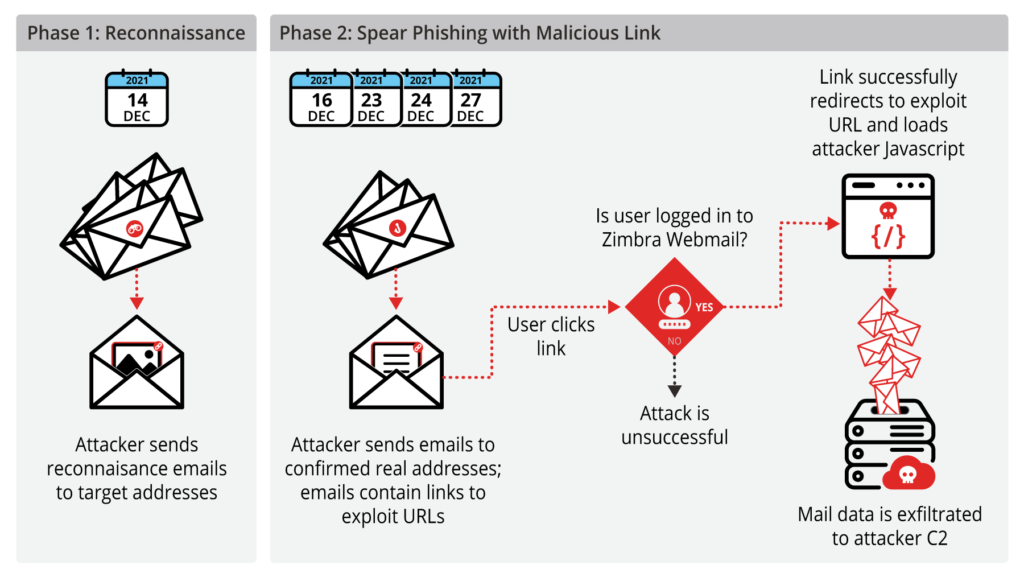 Zimbra Attack Phases via Volexity
Zimbra Attack Phases via Volexity
Cyber attacks have, unfortunately, become part of our everyday reality. These attacks continue to escalate in sophistication and volume, and it just takes one vulnerability or one employee’s careless action to put sensitive data at risk. For organizations in highly regulated industries, this is especially risky — as data breaches can also be accompanied by hefty fines and legal repercussions.
So, what happens when a vulnerability becomes known and it takes too long for a patch to be delivered? Organizations can still take meaningful action to safeguard their data from these kinds of vulnerabilities and subsequent exploitations.
Data: It’s what every attacker is after, and most businesses aren’t taking the necessary steps to secure it. Data is the foundation of business intelligence, so protecting your sensitive information from the ground up will help fortify your organization against vulnerabilities and potential breaches.
The problem is that far too many organizations prioritize the network perimeter, rather than the data itself. However, the perimeter is becoming increasingly hard to define — especially in multi-cloud environments. As the number of endpoints and systems increase, you suddenly have a far greater risk of your data being accessed by a malicious person or entity.
By adopting a Zero Trust, data-centric cybersecurity posture, you can safeguard data everywhere it is stored and shared, so that, even in the face of a breach, the data itself remains secure and under your control at all times. Zero Trust operates under the principle of “Never trust, always verify.” When you stop granting complete access to users and entities within your network, and instead validate their identity and credentials not only to access the network, but the data itself, you have a much stronger posture that will safeguard your data from bad actors.
Virtu’s portfolio of Zero Trust data access products gives people and organizations a remarkably simple way to protect and control sensitive data wherever and however it is stored and shared. To learn more about how you can protect your organization’s most important data and prepare yourself to manage future cyber threats, contact Virtru today.

The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter










Contact us to learn more about our partnership opportunities.