Webinar Recap: Creating Secure File Sharing Frameworks


What is unstructured data to your organization? For many businesses across the globe, it’s the lifeblood of all operations. Email, for instance, can be considered unstructured data–along with video, log, and image files. Unstructured data can take many forms–all with one uniting factor: it demands movement.
Modern Zero Trust practices are stronger than ever, but can backfire by locking data inside a set of secure networks, devices, and endpoints. The data is secure but loses value as it stagnates. There lies the conundrum: Data must be shared, but it has to be done securely.
We sought to explore this central conflict in our latest webinar featuring a panel of IT leaders and Virtru Secure Share users. Speakers include:
- Eric Worthen, Google Super Admin, Utah Department of Government Operations
- Scott Ellis, IT Systems Administrator, Michigan Poverty Law Program
- Rob McDonald, EVP, Platform, Virtru
Virtru EVP of Platform Rob McDonald moderated the discussion, which highlighted real-life use cases for secure external file sharing, and the role that user experience plays in integration and continued protection. McDonald opens the panel by asking why exchanging data is so vital to each panelist’s mission, and why it must be done securely.
Panelist Backgrounds and The Real-Life Need For Secure External Sharing
Scott Ellis is a systems administrator at the Michigan Advocacy Program. Their mission is to provide legal aid to underserved populations like low-income communities, migrants, nursing home residents, domestic violence survivors, and are expanding to members in the LGBTQ+ community. For individuals in these groups, a breach in privacy can have significant, real-world consequences.
“All these agencies are collecting lots of information–lots of very private information–about them and all that's being collected and saved, stored somewhere … We could be looking at people who may be going through transitions in their life that they might not want exposed to the general public … another major group is the migrant community … The lack of information, the lack of data protection, I should say, can cause a great harm for them.”
Our second customer panelist, Eric Worthen is a Google Super Admin at the Utah Department of Government Operations, specifically tasked with protecting taxpayer data like social security numbers, health information, and even GPS and patrol accident images. Though Google Workspace is engineered for collaboration, Worthen highlights the limitations he faces overcoming a history of network-focused secure file sharing and a lack of storage.
“We have to secure the files that are stored, say, in a shared drive [or] My Drive. And we don't want people sharing those drives externally. However, for their workflow, they have to share files larger than, say, 25 megabytes … It's the battle between collaboration and security. So our security teams want everything shut down: ‘Don't share your Google Drive externally with anyone. Don't send that PDF attachment.’ However, Google's built as a collaboration tool.”
Though Ellis and Worthen work in different states and secure different data, they share a similar experience when it comes to external data sharing: very high stakes. Vulnerable individuals suffer the ultimate consequences of any breach, but in order to serve them, their data must be securely shared. This is the data conundrum in real life.
When Security Becomes A Threat To Collaboration
Tools like Sharepoint, Google Workspace, and secure networks all serve their purpose well, but when it comes to sharing sensitive information externally, they may not deliver the necessary combination of functionality, ease of use, and security. This invites the integration of even more security tools with the purpose of protecting data, but with an end result of slowing productivity. McDonald poses an audience question to the panelists, “With so many tools to use, we find it hard to convince our users to use them. Have you encountered that, and how have you overcome it?”
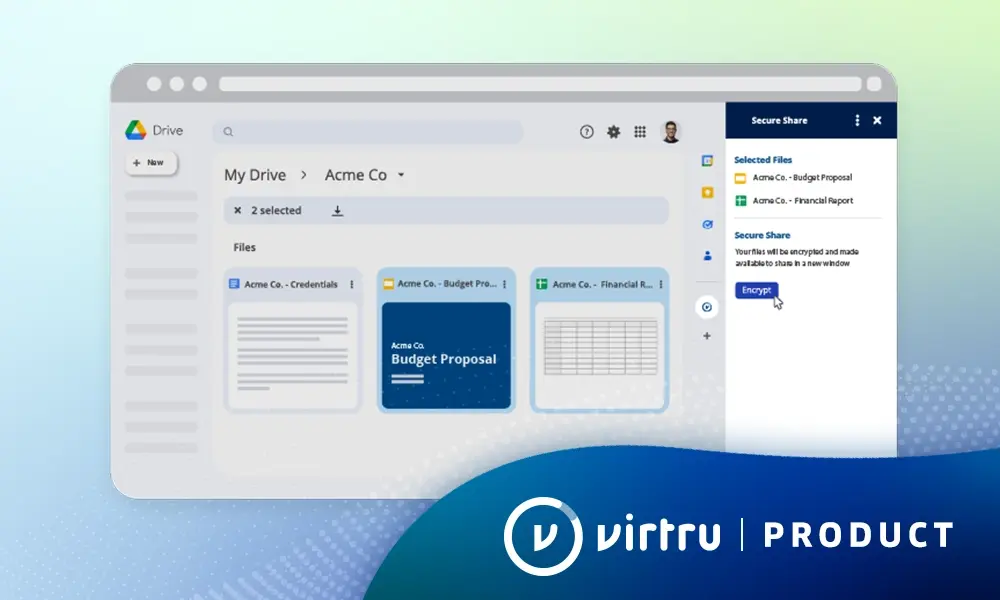
Worthen highlights the friction he’s faced with sharing files using Progress MOVEit managed file transfer, which requires users to remember two passwords in order to integrate and secure data within his network.. Additionally, the uniqueness of the software rings alarm bells, as some notifications from the software tend to read as phishing attempts. Virtru’s Secure Share equips Worthen’s teams to collaborate more seamlessly, as the brand name, ease of use, and seamless integration create trust and credibility users inside and out of the organization.
“So, our internal users are all familiar with Virtru. The external users tend to be familiar because they've exchanged emails securely with, say, a health clinic or tax organization. And so that would assist us just in that little piece that people are familiar with Virtru…the login has 'Sign in with Google, Sign in with Outlook, Sign in with Office 365.' So you're not maintaining those multiple accounts.”
Ellis invokes the idea of shadow IT, which is defined by Gartner as “IT devices, software and services outside the ownership or control of IT organizations.” It’s essentially the use of software without the explicit permission of IT departments, which could open up the floodgates for security risks.
“We've been dealing with that for decades in our organization,” says Ellis. “Someone wants to use Dropbox, and they will use their personal Dropbox, and then their own WhatsApp account…That's where I think Virtru comes in.”
Ellis mentions Secure Share’s ease of use, which allows for a smooth adoption for any user, providing an intuitive experience mirroring other daily-use applications. For Ellis, this ease of use and painless integration helps to build a trust factor between his organization and the software company protecting his external data sharing processes.
Final Takeaways
During the webinar, McDonald posed a poll to the audience: “Are you concerned about the quantity of unstructured data that is shared and consumed internally and externally?” By the end of the webinar, 96% of respondents said yes.
As high-stakes data protectors, our panelists touched on multiple ways to address this concern from a data-first perspective.
1. Security Teams Are Delivering, and External Data Sharing is Next to be Secured
Worthen and McDonald pointed out that security teams in many leading organizations have done excellent work to secure data internally. As for external data sharing, there is still exciting room for opportunity.
“They're doing a terrific job. They're securing, they’re macro segmenting. They're implementing internal Zero Trust and doing all these things, which they should,” says McDonald. “How do you extend those controls to all that work that the security team is doing, to all that [external] unstructured data that is flowing?”
2. Emails and Files Deserve a Contingency Plan, Too
Unstructured data within an organization is the most free-flowing type of data, and it can carry the most sensitive information. It’s a common and simple workflow, but it might be the least protected. In a changing world where external data sharing is becoming more of a business requirement, and data regulations tighten, all data objects need a plan.
“Being able to meet some of the more modern privacy and security regulations, which are more data-owner-centric, is important to future proofing some of the posture of your organization,” says McDonald. Can your file sharing, exchange and collaboration tool give those collaborators and data owners some of the data rights and privacy rights that these frameworks demand?”
3. Easy Integration Will Make or Break Zero Trust Data Sharing
It’s no secret that intuitive software and protocol makes for a smooth adoption of Zero Trust within a company–but what about for the consumer? Companies, made up of a group of largely compliant employees, have some awareness of the importance of data protection. The average consumer may not–opening up the potential for unsafe data sharing practices.
“Having that ability to control that data even after it's left our email system was a game changer for people in terms of the security over it,” explains Ellis. “We're very much out in the community trying to get people to send us cases … we don't necessarily have an ongoing email thread with those people where we have a secure channel to communicate and send documents back and forth. But they can click on that secure share link and submit our referral form. And we know that form is going to be protected by Virtru.”
4. Centering Data is the Future of Secure External File Sharing
“I think it is the future, trying to take a data-centric approach to security to secure those files,” says Ellis.
Securing the data itself regardless of where it’s stored, whether it’s on a secure network or a thumb drive.
“It’s kind of the moonshot sort of thing–we want to have the person who is supposed to have that data [be] the only one that can access it, no matter where it is, at whatever point in time. I think that Virtru has that vision, as I understand it — and that's the goal of Zero Trust.”
Watch the full webinar on demand for more insights on Virtru’s Secure Share and the external data protection conundrum. To schedule a demo, reach out to our team today.

Shelby Imes
Shelby is the Manager of Content Strategy at Virtru with a specialty in SEO, social media, and digital campaigns. She has produced content for major players in healthcare, home services, broadcast media, and now data security.
View more posts by Shelby ImesSee Virtru In Action
Sign Up for the Virtru Newsletter