What is Cyber Security & Why is it Important

What is Cyber Security?
The purpose of cyber security is to protect our digital data. The way we do that is by securing networks, devices, computers, servers and anything else that stores or transfers data from malicious attacks or unauthorized access. In today’s world, a data-centric approach with data sharing management, access controls, and audit capabilities is becoming more critical to prevent or significantly diminish the impact of a cyber security breach.
Importance of Cyber Security
Essentially every organization, from state and local governments, to financial institutions and medical providers, collect some sort of data and then store huge amounts of data on computers or digitally in the cloud. The majority of this data is made up of highly-sensitive information such as personal information, financial data, or intellectual property.
Cyber security is crucial to an organization’s overall security because data is not continuously housed in one secure network or storage space. Data is regularly passed across various networks to other devices, which is where cyber security plays an important role. Cyber attacks are becoming more sophisticated which increases the need to continually improve the security of our systems and use the right tools to protect data itself regardless of the method used to share or store it.
Types of Cyber Security
Different types of cyber security are necessary to prevent the wide array of cyber attacks and cyber systems that exist. The main types of cyber security are:
- Network security to protect the network from unauthorized access and malicious attacks.
- Application security which ensures apps have constant updates and testing to prevent programs from being attacked.
- Endpoint security to protect an organization’s network while being accessed remotely. This has become vital this year as remote access is an essential part of business but causes a weak point for data.
- Data security is another layer of security within the organization that protects company and customer information. This is also becoming more important as we share more via email and store more in the cloud.
- Identity management which recognizes the access every person has in an organization. Once you understand how, where, and by who the network is being accessed, you can better understand how to protect it.
- Database and infrastructure security to secure the physical equipment that an organization uses to house data.
- Cloud security to protect files that are stored in digital environments. Data housed and shared in the cloud possess different kinds of security challenges as opposed to physical hardware.
- Mobile security which revolves around tablets and smartphones that house data.
- End-user education to protect data by informing users accessing the network about good habits such as changing passwords and having 2-factor authentication.
Types of Cyber Attacks
Just as there are many different ways that data is shared, stored, and kept secure, there are also many different types of cyber attacks. The challenge is they are always evolving and developing to become more inconspicuous. The main types of cyber attacks are:
- Denial of service attacks (DoS)
- Hacking
- Malware
- Phishing
- Spoofing
- Ransomware
- Spamming
The threats to data and organizations are changing so quickly that it’s hard for companies and governments to keep up, making it more important to think proactively about threats and how to stay protected from them. This need leads to a continuous monitoring of security systems and having a data-centric approach to security.
How Does Cyber Security Work?
Most cyber security practices operate from a top-down approach, which is also the recommendation by the National Cyber Security Alliance through Safe Online. The top-down approach means the corporate level of the organization is in charge of cyber security and putting it at the forefront of priorities. For cyber security to work properly it needs to be divided into three categories:
- Information technology (IT) security (also known as electronic information security) is the protection of data and information where it’s stored as well as while it’s moving through a network. IT security protects digital and physical data from unauthorized users.
- Cyber security falls under the IT security umbrella, protecting the digital data in networks, computers, and devices.
- Network security (also called computer security) falls under the cyber security category. This uses hardware and software to protect any data that is sent through the computer or other devices, to the network. This protects the IT infrastructure and prevents information from being seized by cyber attackers.
All three of these categories need special security protocols to work together and create a safe environment for data to be housed, physically or digitally, and transferred throughout networks.
Cyber Security Best Practices
While there are many ways to prevent cyber attacks, the key to staying protected is realizing that the biggest cyber threats come from within the organization. According to IBM’s Cyber Security Intelligence Index report, human error is almost always a factor in security breaches. Although only 23.5% of cyber attacks were carried out by inadvertent insiders (compared to 31.5% by malicious insiders), 95% of all breaches involved someone making a mistake.
Email mistakes are a huge way that data can be compromised from within an organization, so it’s important to have email best practices in place. Although most email mistakes are harmless, some can have huge negative consequences. A mistyped email address with sensitive information can be detrimental to a company. Clicking reply-all instead of replying to one person can share sensitive information with more people than intended.
Virtru data protection can keep your information secure when you send the right email, and also save you if you send the wrong one. Virtru email encryption can encrypt your messages with the click of a button and gives you the ability to revoke emails — even after they’ve been sent or read. In addition, Virtru lets you set time limits on emails and disable forwarding to prevent recipients from sharing sensitive messages.
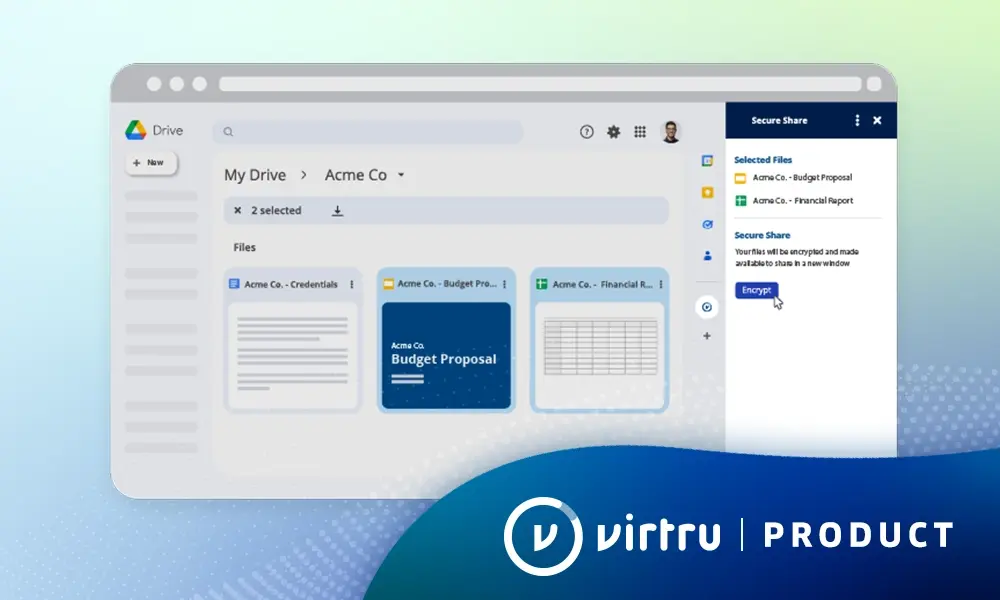
Another great way to minimize risks is to secure all software where data is stored. Hackers are usually looking for the easiest way to get data and don’t want to jump through hoops and barriers. Many companies severely under protect software which leaves the door open for hackers. Tools like Virtru Google Drive and Workspace encryption can help turn your cloud from an open warehouse to a high-security storage vault.
All in all cyber security is an important measure to take to keep data safe and secure. Data is the backbone of your organization, and understanding how your data is shared, stored and protected is key to success. Every day, we create, save, and send data to do our jobs so it’s important to have the right tools in place to secure sensitive/regulated data, meet compliance, prevent a breach, and ultimately, protect privacy while supporting collaboration and growth.
To learn more about how Virtru can provide your organization with flexible, easy-to-use, and trusted privacy technologies that govern access to data throughout its full lifecycle, contact us today.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter