Insider Threats in Cyber Security: How to Detect Them

Business leaders tend to put a lot of faith in their judgment and intuition. They believe they can trust the people they hire to have the organization’s best interests at heart, and exercise appropriate care when it comes to company security. At some point, that trust is going to be betrayed, and that intuition is going to be called out.
Either a malicious insider is going to intentionally exploit their access to your data, or a negligent worker is going to inadvertently expose it. Although you can’t completely eliminate the risk posed by insider threats in cyber security, you can reduce the chances of a breach, and the potential damage an insider can cause if you’re willing to make security a priority.
The Threat Landscape: Where Insider Threats Come From
Security technology continues to advance to combat new hacking threats and techniques, but human behavior changes much more slowly. The biggest threat isn’t a misguided genius exploiting a cutting-edge attack vector — it’s someone in your organization making a mistake.
According to IBM’s 2015 Cyber Security Intelligence Index report, human error is almost always a factor in breaches. Although only 23.5% of cyber attacks were carried out by inadvertent insiders (compared to 31.5% by malicious insiders), 95% of all breaches involved someone making a mistake.
The threats come from any level in an organization, and higher level employees with more access are often a bigger threat. According to a Dell study which surveyed cyber security professionals, 59% listed managers as one of the biggest insider threats in cyber security, followed by contractors (48%), regular employees (46%), IT admin and staff (41%) and 3rd party service providers (30%). Likewise, security pros see danger in a variety of applications, including collaboration & communication apps (45%), cloud storage & file sharing tools (43%), finance & accounting tools (38%) and social media (33%).
What Exactly is an Insider Threat?
The term “insider threat” is often used to refer to malicious insiders willfully stealing, damaging or exposing internal data or systems, but employees motivated by grievances or profit are only one small part of the total threat. Companies face a much more serious threat from workers inadvertently damaging cyber security or disclosing data. In some cases, a worker’s action might comprise the entire breach — for example, an employee could send a confidential file to the wrong client, or lose a flash drive with sensitive information in a public place.
However, the most serious insider threats in cyber security usually occur when employees and partners leave doors open for the bad guys — either through personal negligence, poor or inadequate security practices, or both. The 2013 Target breach is a perfect example of this. The investigation suggests that someone at Fazio Mechanical — a Target partner — screwed up and opened an email infected with malware. According to investigators, once the hackers appears entered Fazio Mechanical’s system, poor internal controls allowed them to infect Target.
The negligence of Target’s own staff helped them, since they were using weak and even default passwords, and even storing login credentials on servers where the hackers could access them. On top of that, Target used outdated software with inadequate patching, creating more security holes for the hackers to exploit.
So who let the hackers in? The Fazio Mechanical employee who opened the email? Target’s security team? The company that certified Target as PCI compliant without noticing their poor security? Employees with lousy passwords? The answer is it that it doesn’t matter; every one of those security errors contributed to the hackers gaining access, and any one of them could let them in again. Good security has to be a team effort, because bad security already is.
Unsecured Software: The First Major Security Threat
We’ve said it before, but it bears repeating: most hackers are motivated by profit, not challenge. In most cases, they behave like any professional thief would — they look for poorly guarded, valuable property, take the easiest way in they can find and try to cover their tracks when they’re done. Sure, there are brilliant hacking teams who will spend years constructing elaborate heists, but they’re the exception. Few crooks are going to work that hard, especially when so many companies are already using software that leaves the door wide open.
From unpatched vulnerabilities to third-party apps installed by employees, unsecured software is one of the biggest insider threats to companies. In fact, according to Verizon’s 2015 Data Breach Investigation, 99.9% of successful hacks take advantage of vulnerabilities that have been known for at least a year. Sometimes the IT team is negligent, but often there are complex organizational or infrastructure problems behind poor software security.
Many companies hire IT staff for development, but then force them to do double duty as system admins. They may be overburdened and not have time to keep up with the latest patches, or not have expertise in systems administration. Other organizations use legacy software that doesn’t support advanced security features, such as encryption (hey, if it happened to the OPM — an organization that stores extensive background data on federal employees — it can happen to anyone). Even companies running up-to-date software often store older information in neglected data silos, and these silos can serve as back doors for thieves.
And it’s not just core applications that pose a security threat. Workers (particularly millennials) tend to adopt cloud apps to enhance productivity and mobility, or provide functionality that company software doesn’t offer. Unfortunately, many of these applications prioritize convenience over security. They automatically synchronize data with the cloud whenever an open connection is available without using encryption, allowing hackers to spy on workers’ data over public connections and steal login credentials for your system. A hacker sitting near a worker in a coffee shop could steal, alter or destroy records, without the worker even knowing their device had been compromised.
It’s a complex problem, and it requires a complex solution. On the administrative end, companies need to audit their systems, and make sure their software is up to date, and regularly being patched. Legacy systems should be migrated to more secure, modern systems. If that’s not feasible, they need to be insulated from outside access as much as possible. For employees and contractors, companies need to strictly control app use, enforcing a software whitelist to prevent breaches through low-security apps.
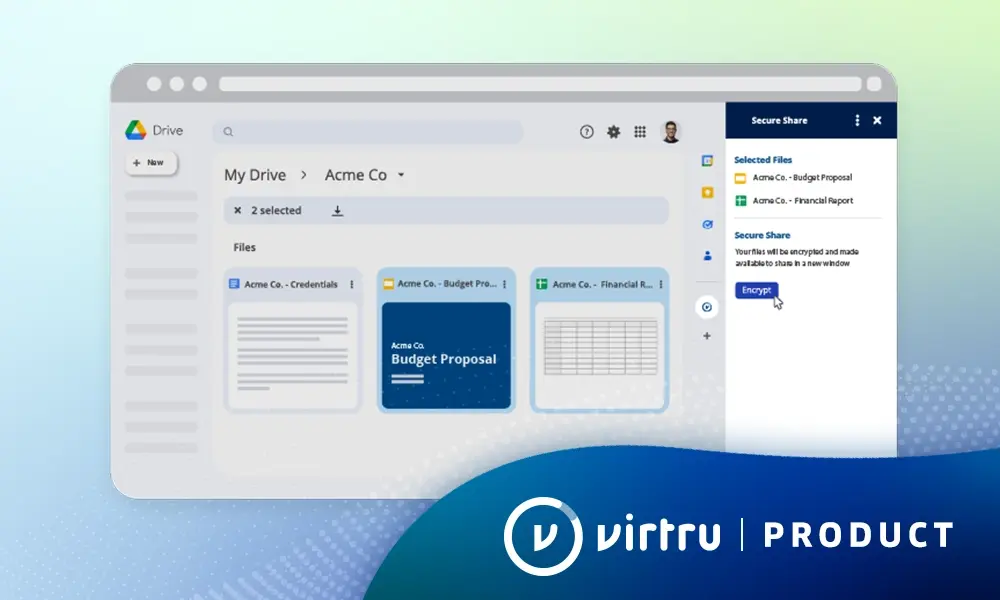
But most importantly, companies need to mitigate the risks of potential security breaches through encryption. Tools like Virtru email encryption and Virtru Google Apps (now known as G Suite) encryption turn your cloud from an open warehouse to a high-security storage vault. Combined with good password enforcement and access control, encryption will make breaches less likely, and drastically limit how much information a successful hacker can access. It can mean the difference between the loss of a few records, and a big, expensive breach.
Unsecured Devices: Another Possible Security Vector
Having a mobile workforce outside of a traditional office setting has a lot of advantages, but security isn’t one of them. It’s much harder to secure mobile devices scattered around the world, than it is to secure a row of office computers on a company network. There are a huge number of ways employees can breach security on their personal devices, including:
- Downloading malware that gives hackers control over the device
- Having hackers spy on their wifi
- Losing their devices, or having them stolen
- Failing to adhere to the company whitelist or technology use guidelines
Employers need to carefully weigh the benefits of allowing workers to work outside the traditional workplace against the risks, and take actions to mitigate potential breaches. Organizations subject to CJIS compliance rules or other strict security requirements may wish to ban personal devices, and issue official work devices with stringent security controls. They may also wish to restrict what information can be accessed outside of the office, requiring employees to use the organization’s secure network to access the most sensitive data.
Companies also need to adequately train and supervise workers in safe technology usage — even if they’re across the world. They should enforce security best practices, and monitor employee accounts for unauthorized access and violations of security policy, using tools like the Google Apps Security (now known as G Suite) reports. Organizations also need mechanisms to allow employees to quickly report stolen devices or suspected security breaches from anywhere, without fear of reprisal; finally, companies need to employ encryption and access control to limit the damage caused by a successful breach.
Bad Access Practices: Setting Security Standards
No matter how many times you tell them, people are going to screw up password safety. One recent survey found that 73% of online accounts use duplicate passwords, and 47% of users haven’t changed their passwords in five years or more. Add to this the prevalence of easily hacked passwords like “123456,” “qwerty,” and the ever-cringeworthy “password,” and you have a recipe for disaster. If an employee shares one easily-guessed password across their accounts, a hacker will be able to get access to everything — including company assets — by hacking a single account.
Plenty of other bad access practices erode security too, including:
- Storing passwords in browsers on shared or public computers
- Failing to clear the browser cache after using public computers
- Leaving computers logged in and unsupervised
- Jumping online on unsecured wifi
- Saving passwords in unencrypted documents
You can never completely stop people from being careless, but you can mitigate the risks. Google Apps security tools allow you to enforce multi-factor authentication, and many other business productivity suites have similar functionality. With multi-factor authentication, employees will have to enter both their password and a code sent to their phone every time they want to login. Even if a hacker is able to guess the password, they won’t be able to gain access without the phone code.
You also need to implement a strong password policy, requiring users to use 12 or more characters, combining uppercase and lowercase letters, numbers and symbols. You should require frequent password changes — ideally at least once every ninety days — to further reduce the likelihood of hackers breaching an employee’s account.
Email Accidents: Or How a Reply All Can Sink Your Company
Email accidents happen all the time, but usually they range from harmless to mildly embarrassing. You’ll autocomplete the wrong address and not notice, click “send” before you’ve finished rewording a message or hit “reply to all” when you should really only send the message to one person.
But these sorts of mistakes can have serious consequences. One mistyped address can break compliance, or even leak a document. Send a sensitive message to a large pool of recipients instead of one particular person, and you could lose several clients — the one whose information you’ve breached, and the others, to whom you’ve just demonstrated that you can’t be trusted with sensitive information.
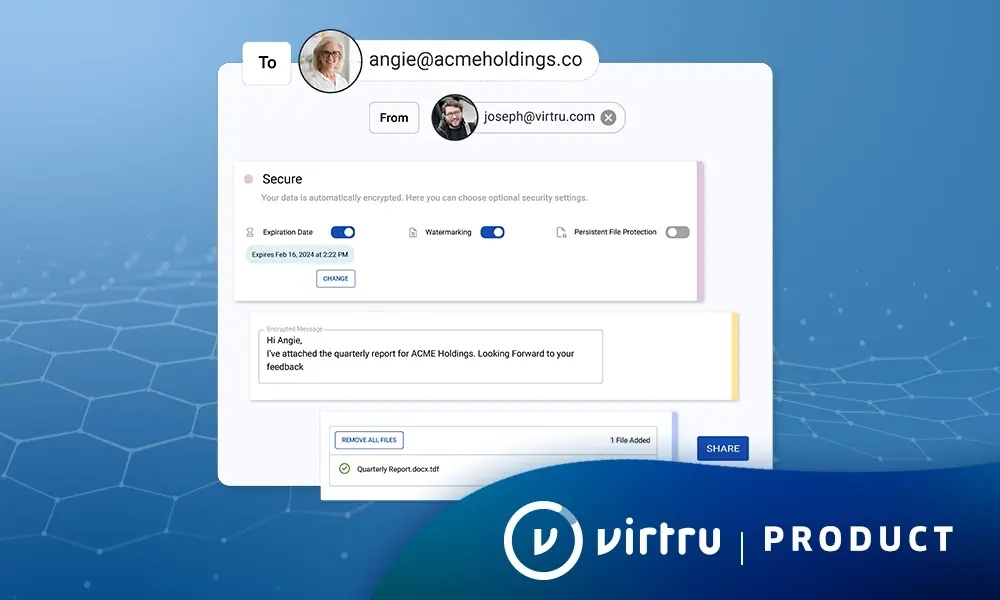
Virtru Pro can keep your information secure when you send the right email, and save your hide when you send the wrong one. Like Virtru Basic, it can encrypt your messages with the push of a button. But, Pro also gives you the ability to revoke emails — even after they’ve been read. In addition, Virtru Pro lets users set time limits on emails, and even disable forwarding to prevent recipients from sharing sensitive messages.
Where Virtru Pro allows you to retract emails after they’ve been sent, Virtru DLP can stop sensitive information from ever leaving your outbox. It can detect social security numbers, credit card numbers, attachments and other data that may breach security and compliance, and automatically take action to prevent a breach.
Virtru admin-controllable rules can be configured to protect your whole organization in a variety of ways, including:
- Forcing encryption on sensitive emails
- Stripping attachments sent to addresses outside the organization
- Warning employees who are about to email sensitive information, or
- Forwarding copies of certain emails to an admin
The warning messages also help train employees in compliance rules, decreasing the likelihood of future compliance violations while preventing immediate breaches.
Malicious Insiders: A Constant Threat
There will always be insider threats in cyber security, because you can’t keep information 100% safe from the people you give it to. Malicious insiders in particular are always going to be a risk, because they’re already past your defenses. They have sensitive data already in their hands, and they know your weaknesses, which can help them steal even more valuable assets.
A Maginot Line approach to data protection does next to nothing to mitigate malicious insider threats in cyber security. In fact, it can encourage the sort of lax internal security that enables internal breaches. Too many companies neglect DLP techniques, allowing anyone with valid credentials to access any piece of sensitive company information, even if it’s not necessary for their job. The single biggest thing organizations can do to mitigate the damage caused by malicious insiders is to restrict access, limiting workers to the data necessary to do their jobs. Combined with encryption, this can sharply limit the damage any one insider can do.
In addition, organizations need to keep detailed logs, recording each user’s access, and monitor them for unusual or suspicious activity. If someone starts downloading lots of information, or sending lots of traffic out of the organization, your security team can investigate it, or even close that account until they can make sure the activity doesn’t represent a breach.
Finally, you need to make security part of your organizational culture. Workers are going to be inclined to trust each other; they’ll feel comfortable leaving computers logged in when their in shared spaces, or giving coworkers access to information those coworkers might not be authorized to view — behaviors a malicious insider can exploit. The only hope of overcoming these tendencies is making security a priority across your organization.
Combat insider threats in cybersecurity by protecting data. No matter how good your intrusion detection systems and firewalls, careless and malicious insiders will always pose a threat to security. Encryption prevents catastrophic breaches, by building walls around each piece of data. Virtru, Virtru DLP and Virtru G Suite Encryption give organizations the power to secure emails, attachments and files, ensuring that they can only be accessed by authorized users. It decreases the risk of breaches, and curtails the amount of damage an insider can do.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter