TABLE OF CONTENTS
See Virtru In Action

Sign Up for the Virtru Newsletter

Organizations today face a multitude of challenges to enable secure data sharing, all while maintaining workforce productivity and hitting innovation goals.
With the average cost of a data breach across South East Asia totaling US$2.71 million*, it’s a stark reminder that traditional security approaches alone are not working and security pros need new solutions that actually protect the data itself while promoting collaboration to unlock its potential.
In a recent webinar co-hosted with our partner eCloud Asia, 83% of attendees reported regularly sharing sensitive information outside of their organization, yet only 19% of attendees felt that they were prepared in the event of a data breach.
Implementing data security practices can often feel overwhelming, but the key here is to shift the focus from keeping everything out (or in) to protecting the most important asset—data—enabling secure movement, collaboration and bolstering productivity.
End-to-end encryption protects data from the moment it’s created to the moment it’s accessed by the intended recipient. It ensures that data remains protected, everywhere it’s shared, at all times. Virtru takes this a step further by providing users with persistent visibility into, and control of, their information, even after it’s been shared. If data sharing needs or circumstances change, data owners can revoke access to shared data at any time, ensuring it remains fully under their control.
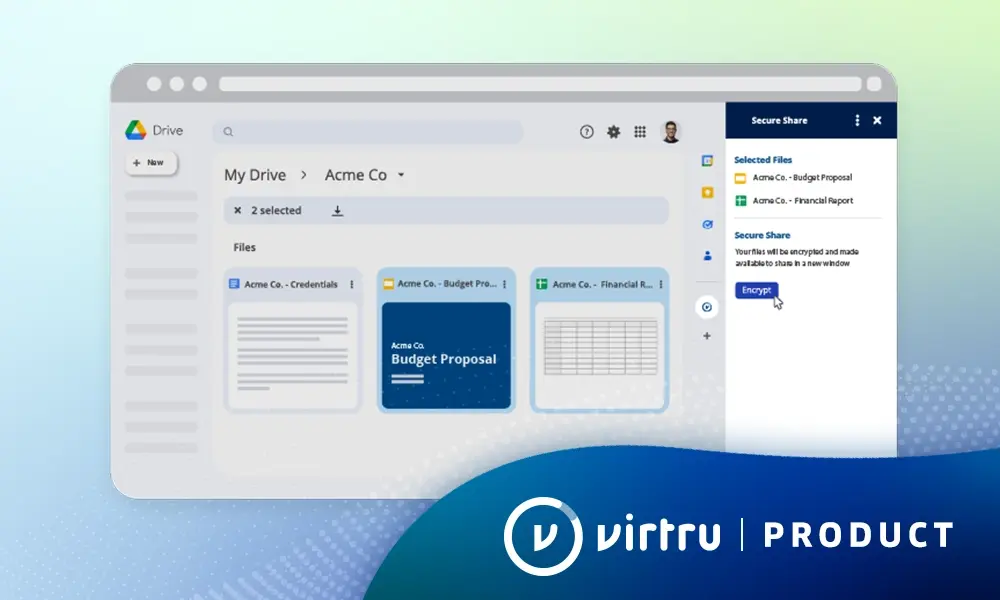
With Virtru, end-to-end encryption is easy. Our solutions integrate seamlessly with Outlook, Gmail, and Google Workspace, as well as enterprise apps such as Salesforce, SAP, and Zendesk. Virtru’s approach to key management allows you to host your own encryption keys to meet data sovereignty requirements, meaning you’re never forced to trust Virtru or any cloud service provider with access to your data.
59% of attendees relied on password-protected documents and native client encryption to secure sensitive data in transit—but there’s a better way! Learn more about how Virtru’s end-to-end encryption and key management solutions can empower your organization to share data more freely and more securely. Contact Virtru or eCloud Asia today to start the conversation.

The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter










Contact us to learn more about our partnership opportunities.