The Importance of PII Encryption for Nonprofit Organizations

Protecting Personally Identifiable Information (PII) is a serious obligation for any organization, but it’s particularly important for nonprofits. With businesses, PII encryption can save customers from damaged credit and identity theft, and save the business from lost revenue, legal and compliance fines, or even ruin. But for human rights groups, reliable and easy email encryption can be vital.
Understanding Nonprofit Security Risk
Nonprofits should already use PII encryption for the reasons other businesses do. Cyber thieves can steal HR records, donor billing information and other sensitive data. This data can be used to impersonate or steal from members and employees, infiltrate the nonprofit, or even attack other groups. Nonprofits may also be subject to personally identifiable information HIPAA rules and other compliance requirements, depending on their mission, funding source, location, and other factors.
However, human rights groups often need to protect a much greater range of information much more carefully. You may be advocating for groups already in a precarious position, such as persecuted sexual or racial minorities, in a hostile environment. In some situations, revealing the location of a meeting, the identity of a participant or even the fact that your group is active could make things worse. For example, a totalitarian government could use the activities of a pro-democracy group with foreign funding as an excuse to further crackdown on civil liberties, or a means to harm individual participants.
It’s important to use threat modeling to investigate the capabilities of your adversaries and choose the most appropriate techniques to mitigate risk. This includes both their technological capabilities and the legal framework. For example, if you do work in a country that restricts encryption, you may have to consider using low-tech safeguards, such as limiting the information you share, and relying on face-to-face meetings.
However, in most situations, the best strategy is to combine security tools like PII encryption, online privacy tactics, and careful public conduct. Encryption will protect your data from hostile government and non-state actors, while also reducing the risks of cyber theft and accidental breaches.
Identify Your Most Important Data
Start by thinking about what types of data your organization has in its possession. This includes ordinary things like the aforementioned membership roles and billing data, as well as what might be called secure business data in other industries — that includes:
- HR records
- Financial data
- Organizational strategy documents
- Field intelligence
- Contacts
- Meeting locations and notes
- Cloud data
Also, think about other types of data you may not have control over. For example, if employees or volunteers post about their activities online, could it contain PII that puts them and others at risk? What about partner organizations? Do they have data that could endanger your members or harm your organization?
Once you identify all the data, grade it by the likelihood of being compromised and the possible consequences of the data being exposed. The point of this isn’t necessarily to rule out any data, but to ensure that you protect all of the most critical information. For example, although PII encryption may be more important than encrypting, say, national meeting notes, there’s no reason not to also protect the latter with encryption while you’re at it.
Use Data Security Solutions That Minimize Reliance on Trust
For many nonprofits, relying on employees and volunteers to keep sensitive personal information safe is a necessity. However, the less you have to rely on people the better. If you can take trust out of the equation or reduce the amount of trust required, it’s almost always a good idea to do so.
Choosing the right technology can make a big difference in this regard. For example, older techniques used for PII encryption require the user to keep track of their own encryption key, and manually configure the program. The recipient likewise has to install encryption, and store their own keys to communicate. If either party loses control of their keys, incorrectly uses the software or leaves a sensitive message unencrypted, it could compromise sensitive personal information.
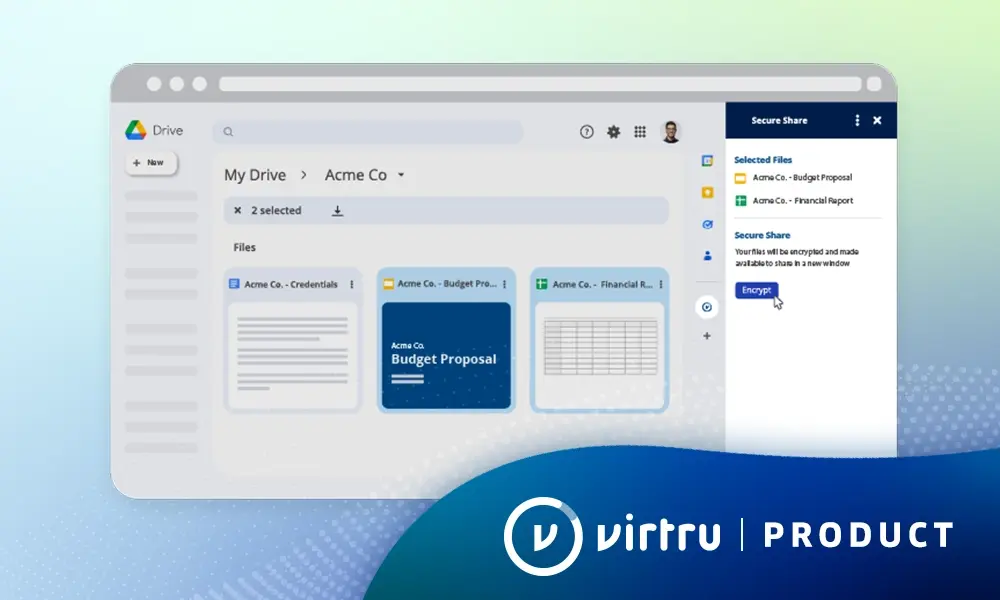
Virtru data protection software works with your existing email account, encrypts with a single click (or automatically, using Virtru DLP), and can send secure messages to anyone — even users who don’t have encryption installed. This drastically reduces the amount of trust you put in users, which lowers the risk of them doing something wrong.
Virtru’s access control features further reduce the necessity of trust — both in your own organization as well as outside contacts and partners. Your users can set time limits on sensitive emails, such as messages with meeting locations, or disable forwarding to prevent contacts from inadvertently sharing PII. Encryption keys also remain under your control, so your users can rescind access to a message if, for example, you suspect a contact has been compromised.
Back Up Your Solutions With Training
No matter how good your technology is, it can only protect workers if they understand how to use it correctly. It’s crucial to train your workers frequently in both existing security techniques and evolving threats. The goal isn’t just to let workers know how to use the technology (that should be the easy part), but to get them focusing on security on an ongoing basis.
Ideally, you should have multiple trainings and reviews throughout the year to make sure that workers never become complacent. Contacts should be trained as well whenever possible. User-friendly PII encryption software will make it easier to train local contacts in situations where available time and resources are limited.
Data loss prevention software can catch dangerous mistakes while also providing ongoing training. VIrtru DLP uses configurable rules to detect sensitive data, alert users and admins and automatically trigger settings to decrease risk. For example, it can trigger encryption automatically when communicating with certain contacts, strip attachments from emails sent outside of the organization, display warnings or even BCC admins when messages contain sensitive data like PII.
Virtru client-side encryption also makes it easier to hold workers accountable for breaches and track down potential leaks. Read receipts show exactly who has viewed an email or document. This can be an invaluable source of intelligence if, for example, you’re trying to track down a mole sharing data with local authorities or opposition.
Virtru PII Encryption Keeps Your Contacts Safe
Virtru offers persistent data protection for nonprofits by encrypting your confidential information shared in emails and files directly from Gmail, Microsoft Outlook, and other tools. You maintain control even after messages have been read or forwarded, to protect donor information and keep volunteers safe in the field.
With the use of client-side encryption, you can prevent third party access to operations plans, overseas communications, and other confidential data by encrypting content before it leaves the device, and enable compliance for common privacy and data residency requirements.
For maximum protection, Virtru lets you manage or host encryption keys, which prevents unauthorized cloud provider or government access requests for your international correspondences, financial statements, and other sensitive info.
Contact us to learn how Virtru can make your nonprofit safer and more effective.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter