Why Enterprise Encryption Solutions Have a Long Way To Go

Data security is everyone’s problem. A global study by PwC found that there were 42.8 million security incidents in 2014 — a 48% increase over 2013 — and those are just the incidents companies were aware of. Every year, organizations pour billions into information security, and every year, hackers find new ways to access sensitive data. As more businesses move to the cloud, there’s more protected data than ever traveling across the Internet — all of which is just one missed patch or clever hack away from being exposed.
Understandably, many businesses have looked to encryption in order to solve their security woes. Yet, while strong encryption is a necessary part of any company’s security plan, many of the current encryption solutions on the market are coming up short. Frequently, enterprise-level companies are asked to choose: do you want to be secure, or do you want to have easy access to your data? That choice can cause headaches and stress, forcing businesses to either gamble on their security, or risk having frustrated employees ignoring internal best practices.
That leaves many executives and IT professionals wondering: why does encryption have to be so difficult in the first place — and what is being done about it?
The Basics of Encryption
Encryption is a system used to protect data so that it can only be read by its intended recipient. Encryption uses a set of instructions called a cipher or algorithm to scramble a message, file, or other piece of data into a string of characters that don’t resemble the original message. Encrypted data can only be read using a cryptographic key, which unscrambles the message back to its original form.
A cipher can be something as simple as instructions to replace every letter in the alphabet with the letter before it (replacing B with A, C with B, and so on) but digital encryption is much more complex. The longer the key, the harder it is to break. Good encryption is basically immune to brute-force attacks — where computers try different keys until they find the right combination. It could take billions of years for a supercomputer to guess the right string. Encryption algorithms can have weaknesses or vulnerabilities, but when they’re implemented correctly, they’re extremely secure.
There are two main types of encryption: symmetric and asymmetric. Symmetric encryption uses the same key to encrypt and decrypt data. It’s fast, but it requires everyone to have the same key before data can be encrypted. Securely distributing these keys is very difficult, so messages such as email are usually sent using asymmetric encryption.
Asymmetric encryption is sometimes called public-key encryption, because it uses two keys: a public key to encrypt messages, and a private key to decrypt them. Users can distribute their public key, allowing anyone to send them a secure message that only they can decrypt, using the private key. It’s slower and more complicated than symmetric encryption, but it’s usually a better way to securely exchange information (especially when you’re communicating with multiple parties).
The Three Different Types of Data and How to Encrypt Them
1. Data at Rest
Data at rest is just what it sounds like: data that isn’t being used at the moment. It could be stored in a database, or on your laptop, for example. Data at rest is relatively easy to protect, by encrypting it and controlling who has access. Companies can implement enterprise encryption solutions with multiple keys, so that individuals and programs can only access the files they need to do their jobs. That way, even if your security were breached, it would only compromise a small amount of data.
Ideally, your organization should avoid giving out encryption keys or certificates to external parties — even administrators for cloud services — because that access can potentially be used to read or copy your data without authorization. Your organization should keep encryption keys stored in a separate location from the data, with a backup copy stored offsite in case of emergencies. Finally, it should monitor data access so that if someone manages to get ahold of data they shouldn’t, you can catch it quickly.
2. Data in Motion
Data in motion is data that’s moving, such as an email being sent to a recipient, medical information traveling through a secure portal, or a stored spreadsheet sent from a cloud service to your computer. Unencrypted email and webpages are very easy to spy on, so encrypting data in motion is becoming a standard practice.
One common method of encrypting data in motion is SSL/TLS (Secure Socket Layer / Transport Layer Security). SSL/TLS is something that you’ve likely encountered while browsing the Internet – whenever you connect to a secure webpage, chances are TLS is being used to encrypt your connection to the server. Likewise, many enterprise level services use TLS/SSL as a backbone — webmail, banks, secure health portals, and others use both protocols to secure data moving across the Internet.
These systems encrypt data separately on each stage of its journey — protecting your data as it bounces from server to server. The downside, however, is that TLS only works if every server on the journey between both computers supports the protocol — if one doesn’t the information is sent as plain text. Likewise, as each server has to decrypt and (re)encrypt the information, each hop of the journey is a potential hole for hackers to attack.
3. Data in Use
Any data a program is currently reading, writing, or changing is data in use. If you’re editing a document, or performing a spreadsheet calculation, you’re accessing data in use. There aren’t any good enterprise encryption solutions for data in use because programs need access to the raw data in order to read or change it. Instead, organizations try to protect data in motion. That way, unencrypted data doesn’t flow out of the program using it.
Researchers are trying to protect data in use with homomorphic encryption — a system that can perform operations on data while it’s encrypted. For example, if your company’s financial records were in an encrypted spreadsheet, you could send a request for third quarter profits. The spreadsheet would be able to send you the figure without ever decrypting the file.
The Challenges Facing Enterprise Encryption Solutions
Moving to the Cloud
There are great enterprise encryption solutions for backup cloud storage. If an organization keeps track of its encryption keys and controls access, the data will be pretty secure. It gets trickier when organizations need to be able to treat the cloud like a hard drive, such as with Google Apps (now known as G Suite) and other Software as a Service (SaaS) providers.
When you open or edit a document or spreadsheet, Google needs to actually access the unencrypted file, which means you can’t restrict their access to your data at rest. If there were a breach in Google’s security, your files would be vulnerable. Usually, cloud providers don’t have to disclose data leaks like banks do, so you could have your data compromised without ever knowing it.
Additionally, a SaaS company could share some of your data with intelligence agencies without you even knowing it. And you won’t have much legal protection if they do, as user agreements for services like Google Drive are often very broad, potentially granting the company a lot of access to your confidential information.
Collaboration and Encryption
The collaborative aspect of software like Google Spreadsheets or Docs poses additional security challenges. First of all, there’s a tremendous amount of data in motion, which means it’s more likely there’ll be a vulnerability somewhere along the way. Exploits such as man-in-the-middle attacks can sometimes break encryption, particularly if you’re using an old and outdated — or very new and untested — algorithm.
Accessing cloud data outside of traditional workplaces creates more security hazards. Contractors or employees may use unsecured WiFi connections in coffee shops and other public places. They may also have weak passwords, or even store passwords on their devices. One stolen phone, or one laptop left logged in at the coffee shop, and a hacker could access customer information, financial records, and other sensitive data.
Locking Down Email Without Making it Unusable
As mentioned above, many encrypted email systems depends on SSL, or the newer TLS standard. SSL and TLS normally encrypt data along each stage of its journey, but it doesn’t always work. If an email travels to a server that doesn’t support encryption, your email will be sent in plain text, allowing anyone with access to the server to read it. If the server only supports an outdated SSL standard, your email will also be vulnerable, potentially allowing a hacker to see the contents of your message. Additionally, TLS won’t stop your mail service from reading your email.
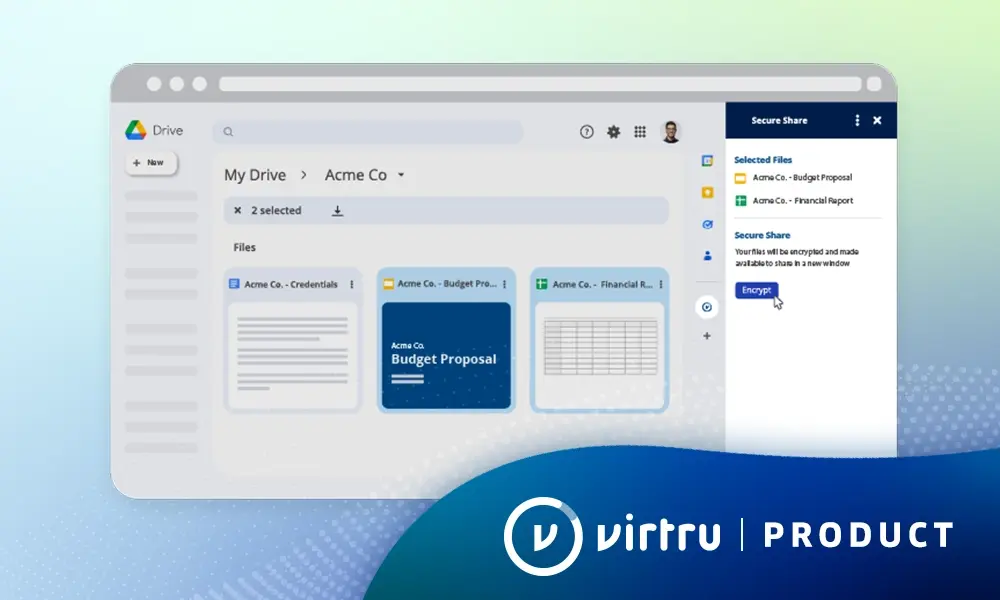
Client-side encryption, like what is provided by Virtru, protects your data from these flaws by encrypting it along its entire journey. Your email is encrypted when it leaves your computer and only decrypted at your recipient’s inbox. Virtru is an ideal enterprise encryption solution because it doesn’t rely on outside servers being compliant in any specific protocol — if you send an encrypted message with Virtru, only your recipient will be able to decrypt it. This also prevents your email provider from reading your emails and attachments, since they’re encrypted before being sent (and there’s no need for your provider to unencrypt and encrypt your message to send it on its way).
Doing Business in the Age of the Cloud
Companies depend on the cloud more than ever before, which makes it crucial to implement enterprise encryption solutions that don’t negatively affect performance. Workers may need to access cloud data any time, day or night, so services need to provide 100% up time.
Software services also need to be intuitive and easy to use. Clunky interfaces and poor integration between systems not only cause frustration, they also eat up time. Any time spent in training, or any extra steps or delays in accessing and processing data results in lost productivity.
Most importantly, everything has to be optimized for collaboration. Cloud services must be able to support multiple users accessing the same data at the same time, from locations across the world. And business software must accomplish all of this while implementing enterprise encryption solutions that are robust enough to resist data leaks, malware, hackers, unsecured networks, and all the other security threats businesses face.
The Need for Greater Security
Even as the need for cloud and web-based services continues to grow, cyberespionage is becoming a bigger problem than ever before. In the 2015 Data Breach Investigation Report, Verizon found 79,790 security incidents, compromising 700 million records in 2015. These incidents occurred all over the world, and although the public sector, the information industry, and finance were most heavily affected, no industry was unaffected.
The report found that in 70% of cases with known motives, the attackers were going after a secondary target. That means that, even if your company doesn’t have data that’s valuable to hackers, they could still target you specifically to compromise your customers or partners. Perhaps the most disturbing statistic is that 70% of attacks could have been prevented. At least one exploited a security flaw that should have been fixed in 1999. Forget keeping up with cutting-edge cyberattacks — many companies aren’t even plugging 16-year-old security holes!
Business Partners, Third Parties, and Vendors
As the Data Breach Investigation Report showed, hackers are willing to look for the weakest link in order to get at the data they want. Even if your organization does its due diligence, a partner with access to your confidential records might not be, and their poor security could be your downfall.
The same goes for your technology vendors. If they don’t plug security holes quickly, they could compromise your organization, or even your whole industry. It’s not enough for individual organizations to protect their data anymore. Enterprise encryption solutions need to be adopted across industries, so that there is no weak link hackers and cyber spies can exploit to access protected information.
The Cost of Compliance
As hackers and cyber spies get more sophisticated, regulatory regimes are placing increasing demands on organizations, and heavier penalties for data breaches. HIPAA, CJIS, and other regulatory requirements are both exacting and vaguely worded, making it hard for many enterprises to even budget for adequate security, let alone implement it.
In the case of HIPAA, the gap between regulatory estimates and actual costs is extreme. One HHS estimate put the cost at about $1,040 per organization, but security expert Tod Ferran at the Security Metrics blog estimates a small organization would pay $4,000 at minimum for HIPAA compliance, and the cost for a large enterprise will run $50,000 or more. In the case of PCI, level 1 merchants — enterprises processing over 6 million credit card transactions per year — can spend as much as $5 million, and even small companies often have to invest tens of thousands of dollars just to achieve a minimum level of compliance.
The situation is compounded by the fact that many organizations are subject to multiple regulatory regimes. Hospitals take credit card payments, subjecting them to both PCI and HIPAA, for example. It’s clear that a new paradigm is needed — a situation where instead of constructing pricey ad hoc security systems, organizations can collaborate on a security regime that benefits all.
The Solution: A Default Encrypted World
For encryption to really protect data, it has to go beyond your laptop, your server, or even your entire organization. We need to develop enterprise encryption solutions that make security the default. Encryption as a service needs to become standard for any app and any type of data — at rest, in use, or in motion.
The technology isn’t there yet, but at Virtru, we’re already taking the next step. Our client-side encryption works with Gmail, Microsoft Outlook, and all common browsers to secure email easily and effectively. There’s no need for exchanging keys or using clunky portals. Once the app is installed, all you have to do is click the blue “v” before you send an email, and it is automatically encrypted. From the point of view of your recipient, it works like any other email, but it’s virtually invulnerable to hackers, spies, and anyone else who could threaten your data security.
Virtru is a great way to protect your emails and attachments, but it’s also a first look at what Internet security could be. By preventing unauthorized access to email without adding unnecessary steps or slowdowns, we’re proving that it’s possible to build enterprise encryption standards that work with the Apps your business already depends on.
Take the Next Step with Virtru
Virtru goes beyond email encryption, giving your organization unprecedented control over messages and attachments. Virtru allows businesses to rescind emails, even after they’ve been read, and to set time-limits on sensitive messages to decrease the risk of exposure.
Virtru DLP helps prevent human error, allowing you to stop employees from exposing protected data over email. It can pop up warnings when they type in social security numbers, encrypt sensitive emails automatically, or even alert your administrator when an employee sends a message outside the organization. Whether your security is threatened by a sophisticated hacker or an absent-minded employee, Virtru can help you stop data breaches before they happen.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter