6 Compliance Issues You Didn’t Know You Had

Staying compliant can feel like a never-ending battle. As your business expands, there are more rules to follow, more threats to address, and more security holes to patch. Eventually, just putting together a compliance initiative can seem like an overwhelming task.
Understandably, compliance issues can pop up everywhere — you might not even see some of them coming. If you want to prevent your business from facing hefty fines, expensive breaches, or an embarrassing scandal, you need to make sure you aren’t facing any major compliance issues. Not sure where to start? Here are the 6 most common compliance issues — and how you can deal with them.
1. Difficulty Incorporating Multiple Compliance Regimes
A large organization that conducts business in several countries can easily be subject to half a dozen or more compliance regimes — and that doesn’t count HIPAA business associate agreements, model contracts governing the movement of data across borders, and other legal agreements with partners, providers and clients. Even figuring out which product or service is governed by which law can bring up serious compliance issues. A data processor could be forced to juggle HIPAA and CJIS because it works with health data for law enforcement.
On top of that, laws change constantly. Cities, states, and counties come up with local standards. Countries negotiate new trade treaties with data protection agreements. And success just makes it harder; the more your business grows and expands into new markets, the thornier and more complex compliance issues become.
2. Inadequate Implementation
The fact is, failing to fully implement compliance is far more common than succeeding. Even enterprises with strong security cultures often have multiple compliance issues. According to the Verizon 2015 PCI Compliance Report, 4 out of 5 companies fail interim PCI testing. Although average compliance across most PCI standards is strong, there are so many standards that nearly everyone fails at something — and that’s just PCI.
According to Verizon, the problem is that many organizations see compliance “as a one-off tick-box exercise or fire drill that the security team owns and the rest of the organization begrudges.” Let’s face it — compliance is difficult, expensive, and tedious. Almost everyone fails at it, because leadership is unwilling to commit the money and time to do it right.
Poor communication and engagement also plague compliance initiatives. Companies rarely take the time to train workers, address any compliance issues or questions that come up, and monitor them on an ongoing basis. They don’t make security a part of the workplace culture, so workers go right back to old habits as often as not.
3. Partner Compliance
Compliance initiatives like HIPAA are designed to keep data secure, not to apportion blame fairly; if a business partner or contractor screws up and gives away protected data, you could be on the hook, too.
Contracts, such as HIPAA Business Associate Agreements (BAAs) and CJIS Management Control Agreements (MCAs), can help somewhat. They put rules in place for information access, security, and responding to breaches, helping both partners stay compliant, and provide crucial legal cover should your partner lose control of protected data.
Unfortunately, there’s often little you can do to ensure your partners and contractors hold up their end of the bargain. Hospitals, for example, often work with hundreds of doctors who aren’t employees. They can (and should) make those doctors sign BAAs, but there’s no realistic way to make sure they actually follow the rules.
The same goes for software vendors or cloud hosting providers. You can arrange periodic audits or select someone audited by a third party, but for day-to-day security, you have to take them at their word — even when it’s your company’s reputation on the line.
4. BYOD and Telecommuting
Organizations can safeguard workplace computers using tools such as encryption, firewalls and anti-malware programs, but many of these security features are routinely circumvented in Bring Your Own Device (BYOD) workplaces. And for every worker who takes BYOD security seriously, there will be at least a few others who put convenience ahead of compliance.
Workers may be storing their passwords and forgetting to clear their browser cache, for example. Not only does this make it easier for hackers to access their data, but if a thief steals a device, it could give them unrestricted access to protected data. If employees don’t install patches and run antivirus programs, their computers could be infected by malware that can steal corporate secrets.
Telecommuting itself can interfere with security and compliance. If your employees use public, unsecured internet connections, hackers can spy on their traffic, potentially stealing login credentials or data. And working from home doesn’t necessarily solve the problem; compliance regimes such as CJIS require a high level of network security, and there’s usually no way to know whether a particular telecommuter’s Wi-Fi is up to standards.
5. Poor DLP
Many companies approach privacy as if they were building a fort. They use strong passwords, encryption, firewalls, and other security tools to keep invaders out, but don’t consider what would happen if their defenses were breached.
The problem is a hacker could theoretically steal anything an employee has access to. If all of your employees have unrestricted access to a database of 80,000 customer names, one breach could expose them all. And it can happen even without a hacker; all an employee needs to do is send an attachment or email with login information or protected data to the wrong person, and you could have a major breach on your hands.
Data Loss Prevention (DLP) can help you minimize potential losses by limiting access to sensitive documents. Companies need to start categorizing sensitive information, such as intellectual property, and Personally Identifiable Information (PII), and ensuring that each person only has access to the information they need. If a hacker gains access, DLP can mean the difference between exposing a few records and an entire database.
6. Lack of Adequate Encryption
Data encryption is one of the most important compliance tools available. Once data is encrypted, it is unreadable and virtually impossible to crack without the cryptographic key. Even if a customer is able to access a company’s database or intercept an employee’s email, strong encryption will keep the data safe.
Unfortunately, organizations that should know better are failing to encrypt data-at-rest and data-in-motion, with disastrous results. The Anthem Hack, which exposed the personal data of tens of millions of people, is only one of many hacks that could have been prevented by encryption.
Organizations often choose not to encrypt because they view encryption as less convenient, as they fear it will make their databases unreadable. In reality, however, if companies tag their encrypted files, they can access the information they need without compromising data security.
Not all encryption is equally effective. Longer keys make encryption much harder to crack, so companies need to use 128-bit or higher encryption. In addition, they should use client-side encryption whenever possible. Client-side encryption is extra secure, as it encrypts data as it leaves your computer, and only decrypts it once it reaches its destination—meaning you can guarantee your data is safe as it travels to where it needs to go.
The Need for DLP and Universal Strong Encryption
Your security is only as good as your weakest link. Virtru helps companies solve a wide range of compliance issues with powerful security tools that anyone can use. Virtru encryption protects emails with a single click, using military-grade, client-side encryption. It is the only email encryption program that doesn’t inhibit any email functionality, or make email more difficult to use. Unlike other email encryption tools like PGP, Virtru automatically handles email keys, and can encrypt:
- Attachments
- Emails sent to multiple recipients
- Emails to people who haven't installed Virtru's plugin
Virtru adds powerful features that aid compliance and give you greater control of your communication. You can revoke emails, set time limits, and disable forwarding to prevent recipients from sharing sensitive information.
And unlike other email programs that have email revocation, Virtru Pro works no matter what email service the recipient uses — even after they’ve opened the email. When an employee accidentally inputs the wrong address and hits send, it can mean the difference between a close call and a serious compliance issue.
Virtru DLP (available for both Google Workspace (formerly G Suite) and Outlook) tackles the most difficult security and compliance problem of all: human error. It has customizable rules that can detect if an email contains sensitive information such as social security numbers, preventing employees from accidentally sending sensitive information in an unsecured email. It comes with settings for common rules, such as HIPAA and CJIS, making it easier to address the compliance issues that face your organization. We also just came up with an add-on that makes HIPAA email compliance even easier with the HIPAA Rule pack. It can also automatically encrypt emails, strip attachments to prevent disclosure of internal documents, or even CC administrators to allow monitoring of sensitive emails.
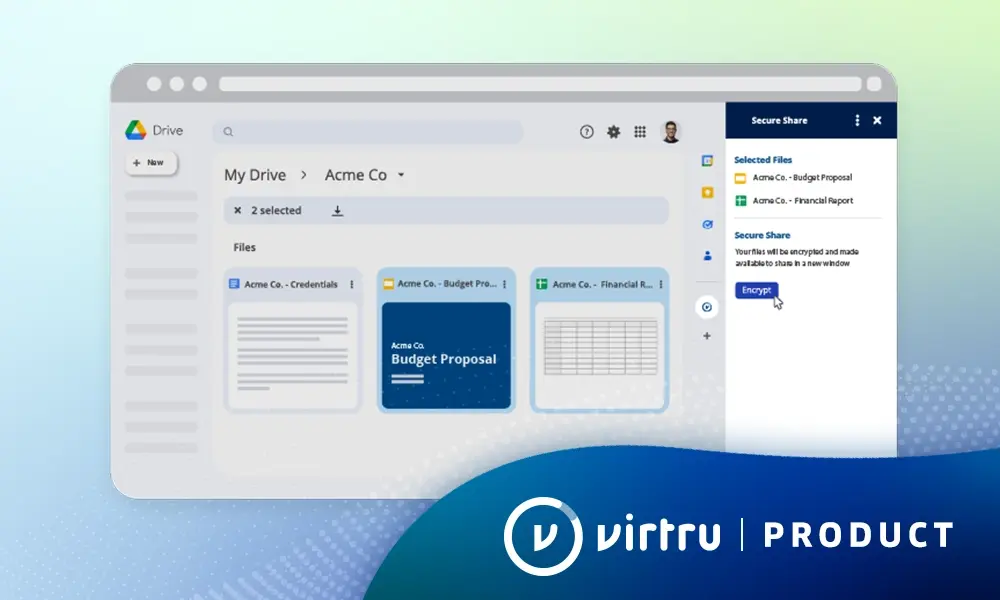
Finally, Virtru for Google Workspace helps to secure your entire cloud workspace with the same powerful, client-side encryption used in our other products. You can control keys and manage access to files and emails through your entire Google Domain, providing easy admin tools that prevent data leaks without harming productivity. For solving compliance issues in the cloud, it simply doesn’t get easier — or safer — than Google and Virtru.

Editorial Team
The editorial team consists of Virtru brand experts, content editors, and vetted field authorities. We ensure quality, accuracy, and integrity through robust editorial oversight, review, and optimization of content from trusted sources, including use of generative AI tools.
View more posts by Editorial TeamSee Virtru In Action
Sign Up for the Virtru Newsletter